[ad_1]

Hacking group StrongPity APT distributes fake Shagle chat app which is a trojanized version of Telegram app for Android with an additional backdoor.
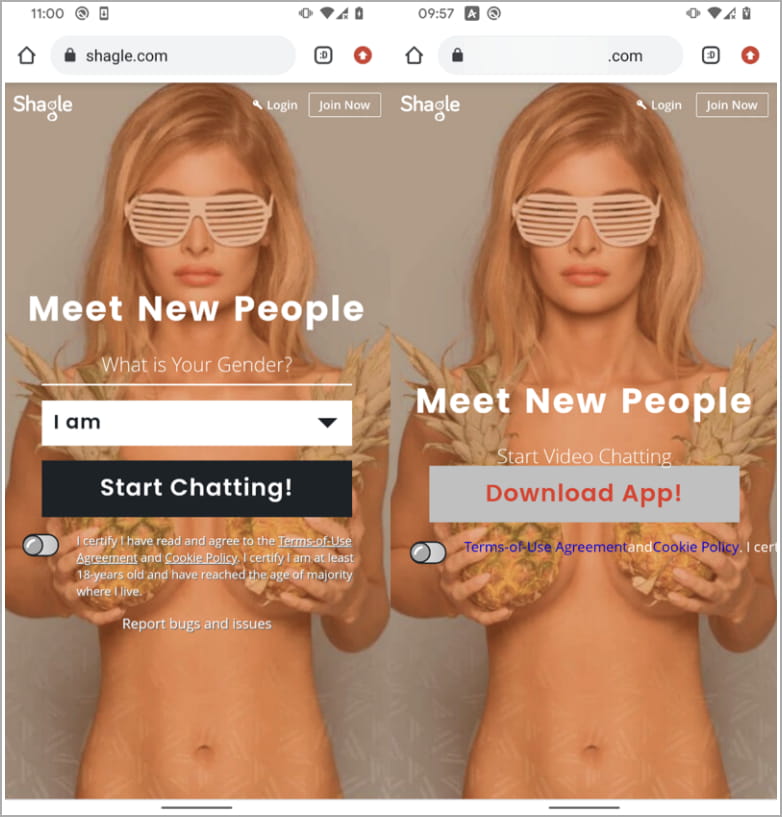
Shagle is a legit random video chat platform allowing strangers to talk through an encrypted communication channel. However, the platform is entirely web-based and does not offer a mobile app.
StrongPity was found using a fake website since 2021 that impersonates the real Shagle site to trick victims into downloading malicious Android.
Once installed, this app allows hackers to spy on targeted victims, including monitoring phone calls, collecting text messages, and grabbing contact lists.
Source: ESET
StrongPity, also known as Promethium or APT-C-41, was previously attributed to a campaign that distributed Trojanized Notepad++ installers and malicious versions of WinRAR and TrueCrypt to infect targets with malware.
Last StrongPity activity was discovered by ESET researchers who attributed the campaign to the APT spy group based on code similarities to past payloads.
Additionally, the Android app is signed with the same certificate the APT used to sign an app that mimicked the Syrian e-gov Android app in a 2021 campaign.
Android Telegram App Trojan
The malicious Android application distributed by StrongPity is an APK file named “video.apk”, the standard Telegram v7.5.0 (February 2022) application modified to pose as a Shagle mobile application.
ESET could not determine how victims arrive at the fake Shagle website, but it is likely through phishing emails, smishing (phishing SMS) or instant messages on online platforms. line.
The malicious APK is provided directly from the fake Shagle site and was never made available on Google Play.
ESET says the cloned site first appeared online in November 2021, so the APK has likely been in active distribution since then. However, the first detection confirmed in the wild came in July 2022.
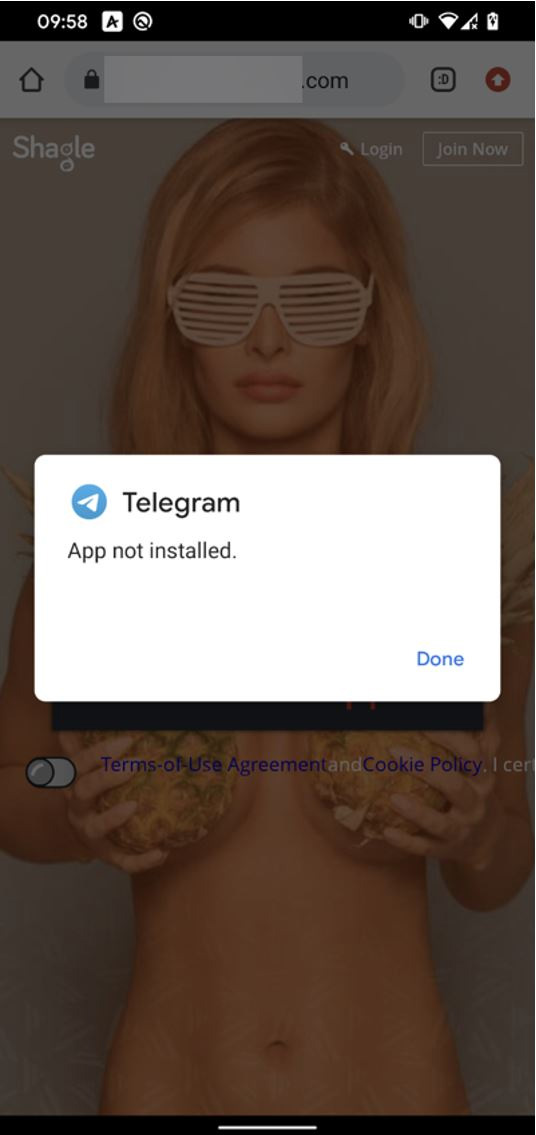
One of the downsides of using Telegram as the base for the hacking group fake app is that if the victim already has the real Telegram app installed on their phone, the stolen version will not be installed.
Source: ESET
Currently, the API ID used in captured samples has been throttled due to overuse, so the trojanized app will no longer accept new user registrations; therefore, the backdoor will not work.
ESET believes this indicates that StrongPity successfully deployed the malware to the targeted victims.
Backdoor designed to spy on victims
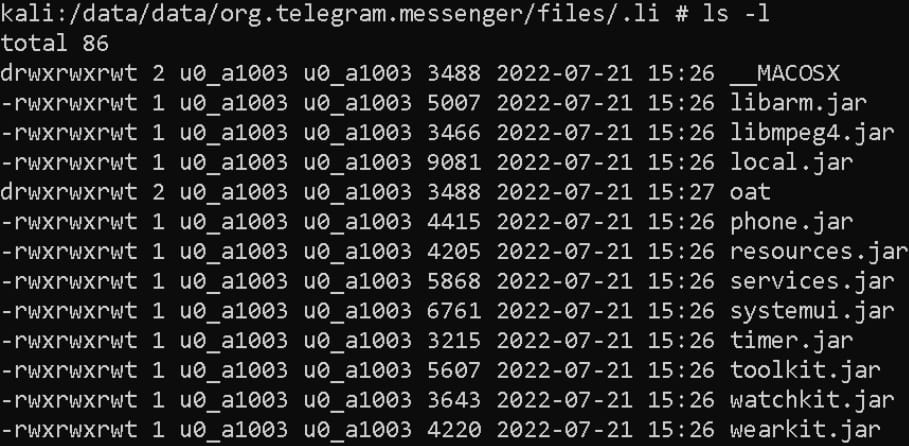
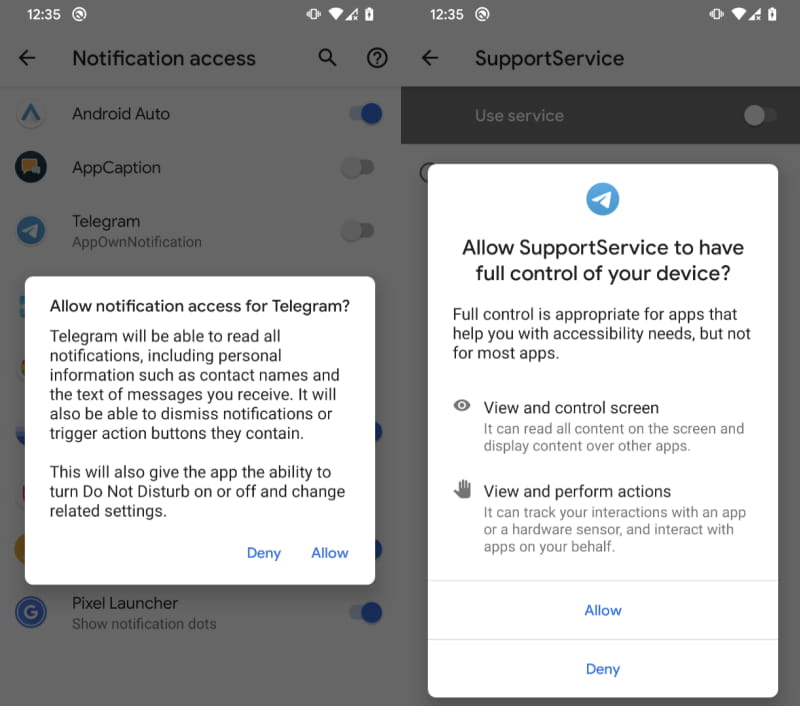
During installation, the malware requests access to the Accessibility Service and then retrieves an AES-encrypted file from the attacker’s command-and-control server.
This file consists of 11 binary modules extracted on the device and used by the backdoor to perform various malicious functionality.
Source: ESET
Each module performs a spy function and is triggered as needed. The full list of malicious spyware modules is listed below:
- libarm.jar – records phone calls
- libmpeg4.jar – collect text of incoming notification messages from 17 applications
- local.jar – collects the list of files (file tree) on the device
- phone.jar – misuse accessibility services to spy on messaging apps by exfiltrating contact name, chat message and date
- resources.jar – collects SMS messages stored on the device
- services.jar – get device location
- systemui.jar – collects device and system information
- timer.jar – collects a list of installed applications
- toolkit.jar – collect contact list
- watchkit.jar – collects a list of device accounts
- wearkit.jar – collect a list of call logs
Collected data is stored in the application directory, encrypted with AES, and ultimately sent back to the attacker’s command-and-control server.
By abusing the accessibility service, the malware can read the content of notifications from Messenger, Viber, Skype, WeChat, Snapchat, Tinder, Instagram, Twitter, Gmail, etc.
Source: ESET
On rooted devices where the regular user has administrator privileges, the malware automatically allows itself to change security settings, write to the file system, reboot, and perform other dangerous functions.
The StrongPity hacking group has been active since 2012, usually hiding backdoors in legitimate software installers. According to ESET’s report, the threat actor continues to employ the same tactics after a decade.
Android users should be careful with APKs from outside Google Play and pay attention to permission requests when installing new apps.
[ad_2]
Source link
