[ad_1]

A financially motivated cybercriminal hacks into telecommunications service providers and business process outsourcing companies, actively overriding defensive mitigations applied when the breach is detected.
The campaign was spotted by Crowdstrike, which claims the attacks began in June 2022 and are still ongoing, with security researchers able to identify five separate intrusions.
The attacks have been attributed with low confidence to hackers tracked as the “Scattered Spider”, who demonstrate persistence in maintaining access, reversing mitigations, evading detection, and pivoting to other valid targets if countered.
The ultimate goal of the campaign is to breach telecommunications network systems, gain access to subscriber information, and conduct operations such as SIM swapping.
.png)
Campaign Details
Threat actors gain initial access to corporate networks using a variety of social engineering tactics.
These tactics include calling employees and impersonating IT staff to harvest credentials or using Telegram and SMS messages to redirect targets to personalized phishing sites that feature the logo of the company.
If MFA protected target accounts, attackers used either push notification MFA Fatigue Tactics or engaged in social engineering to obtain victim codes.
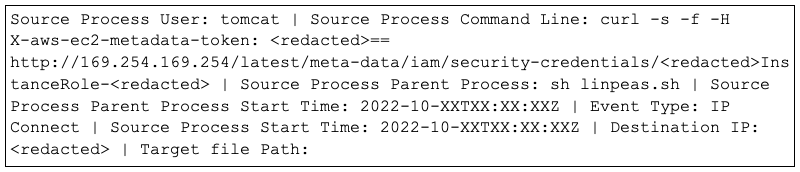
In one instance, adversaries exploited CVE-2021-35464a flaw in the ForgeRock AM server, to execute code and elevate their privileges on an AWS instance.
“By leveraging AWS instance roles to assume or elevate Apache Tomcat user privileges, the adversary would request and assume the permissions of an instance role using a compromised AWS token,” explains Crowdstrike.
Once hackers gain access to a system, they attempt to add their own devices to the list of trusted MFA (multi-factor authentication) devices using the compromised user account.
Crowdstrike has noticed hackers using the following Remote Monitoring and Management (RMM) utilities and tools in their campaigns:
- AnyDesk
- BeAnywhere
- Domotz
- DWservice
- Fixme.it
- Fleetdeck.io
- Italian Terminal Manager
- Level.io
- Login
- manage engine
- N-Able
- Pulseway
- Report
- Rsocx
- Screen connection
- SSH Tunnel RevShell and RDP over SSH
- Team Viewer
- TrendMicro Basecamp
- Sorilla
- ZeroTier
Many of the above software are legitimate software commonly found in corporate networks and are therefore unlikely to generate security tool alerts.
In the intrusions observed by Crowdstrike, adversaries have been relentless in their attempts to maintain access to a hacked network, even after being detected.
“In multiple investigations, CrowdStrike observed the adversary becoming even more active, implementing additional persistence mechanisms, i.e. VPN access and/or multiple RMM tools, if mitigations are slowly being implemented,” CrowdStrike warned.
“And in several cases, the adversary reversed some of the mitigations by reactivating accounts previously disabled by the victim organization.”
In all intrusions observed by Crowdstrike, adversaries used various VPNs and ISPs to gain access to the victim organization’s Google Workspace environment.
To move laterally, threat actors mined various types of reconnaissance information, downloaded user lists from hacked tenants, abused WMI, and performed SSH tunneling and domain replication.
Crowdstrike shared a long list of Indicators of Compromise (IoCs) for this activity at the bottom of the report, which is critical for defenders to note as the threat actor uses the same tools and IP addresses for different intrusions.
[ad_2]
Source link
