[ad_1]

A team of university researchers has developed a new side-channel attack called “Freaky Leaky SMS”, which relies on the timing of SMS delivery reports to infer a recipient’s location.
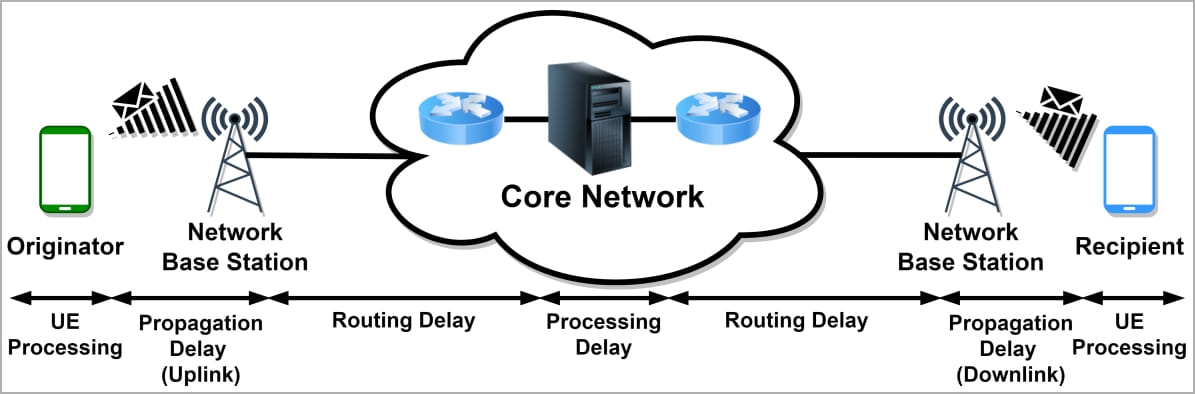
SMS delivery reports are managed by the mobile network’s SMSC (Short Message Service Center) to inform when a message has been delivered, accepted, failed, undeliverable, expired or rejected.
Although there are routing, network node propagation, and processing delays in this process, the fixed nature and specific physical characteristics of mobile networks result in predictable times when standard signal paths are followed.
Researchers have developed a machine learning algorithm that analyzes the timing data in these SMS responses to find the recipient’s location with an accuracy of up to 96% for locations in different countries and up to 86% for two locations in the same country.
Preparatory work
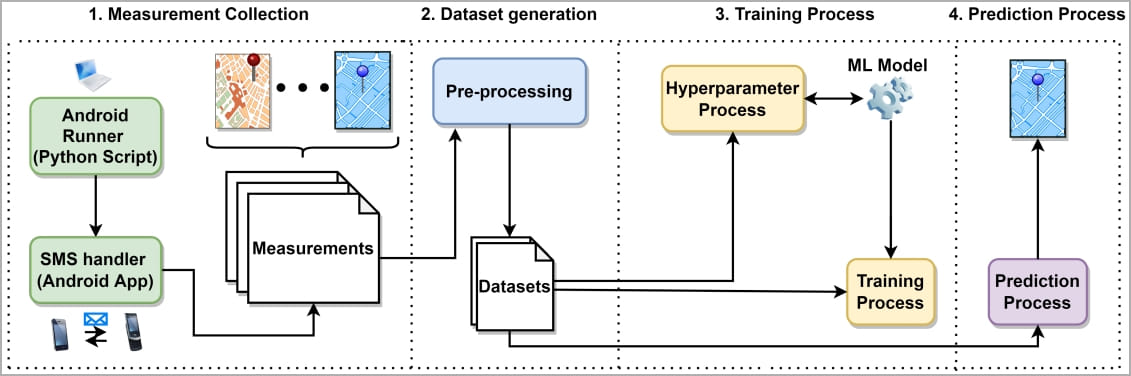
The attacker will first need to collect measurement data to establish concrete correlations between SMS delivery reports and the known locations of their target.
The more precise the attacker has data on the location of his targets, the more accurate the results of the location classification in the ML model predictions will be during the attack phase.
To collect the data, the attacker must send multiple SMS messages to the target, either masking them as marketing messages that the recipient will ignore or not consider spam, or using silent SMS messages.
A silent SMS is a “type 0” message without content, which does not produce any notification on the target’s screen, but its reception is always acknowledged by the device on the SMSC.
In their experiments, the paper’s authors used ADB to send bursts of 20 silent text messages every hour for three days to multiple test devices in the United States, United Arab Emirates, and seven European countries, covering ten carriers. and various communication technologies and generations. .
Next, they measured the timing of SMS delivery reports in each case and aggregated the data with the corresponding location signatures to generate a complete ML assessment dataset.
The ML model used a total of 60 nodes (10 inputs, 10 outputs, 40 hidden) and the training data also included receive location, connectivity conditions, network type, receive distances, etc.
Location of recipients
The experiment focuses on “closed world” attack scenarios, i.e. classifying the location of the target to one of the predetermined locations.
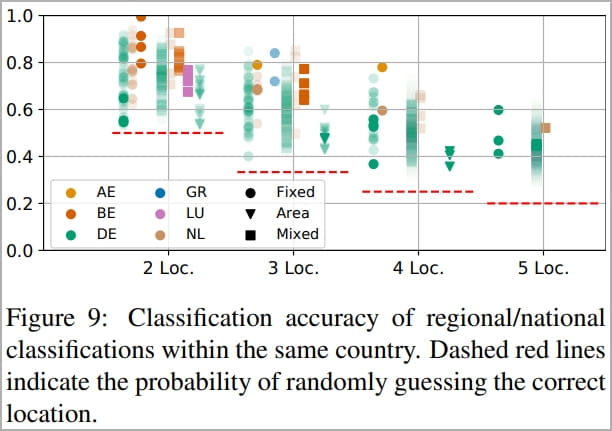
The academics found that their model achieved high accuracy in distinguishing between domestic and foreign locations (96%), similarly good guesses in classifying countries (92%) and reasonably good performance for locations in the same region. (62%-75%).
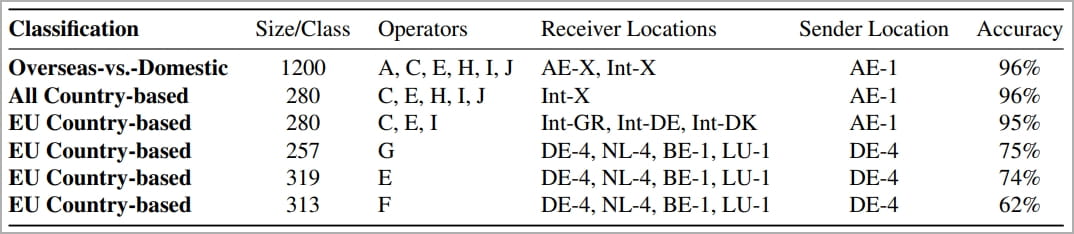
Accuracy depends on location, operator and conditions. For example, in Germany, the system had an average accuracy of 68% across 57 different classifications, with the best performance being 92% in a specific German region.
Belgium obtained the best results, with an average of 86% correct estimates and a maximum of 95% in the best performing region.
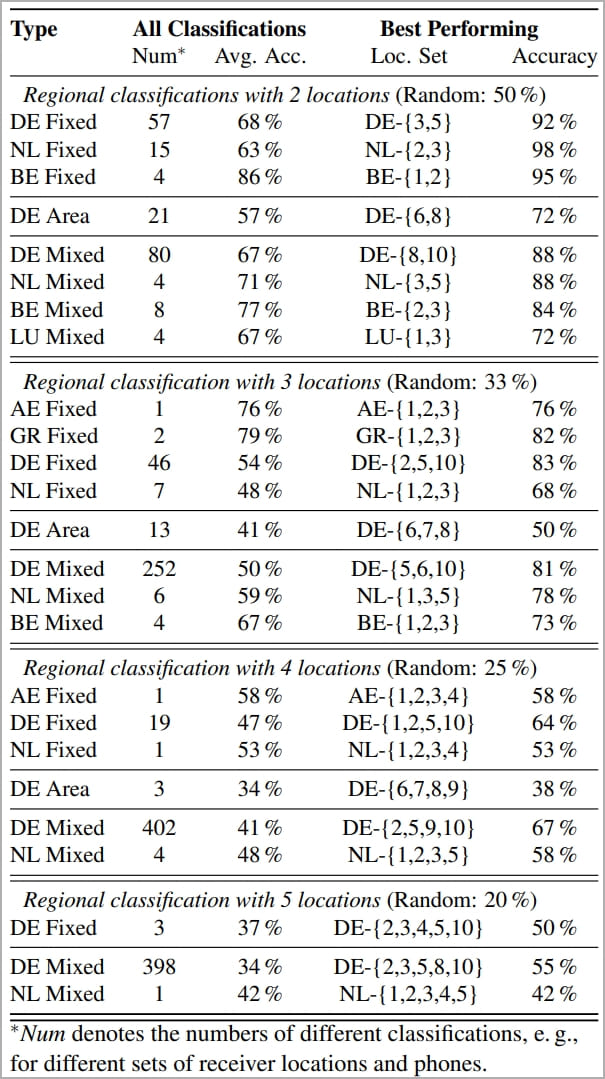
When three locations are considered in Germany, the model’s prediction accuracy drops to an average of 54% and peaks at 83% in the best-performing case, which is still significantly higher than the 33% random guess.
For Greece, the model provided a notable average of 79% correct location predictions for three locations (random 33%) and reached 82% in the best case.
The researchers left “open world” instances where the target visits unknown locations for future work. However, the paper again provides a short assessment to explain how the prediction model can be adapted to these scenarios.
In short, open-world attacks are feasible based on the use of probability outputs, anomaly detection, and the inclusion of landmarks and other locations of interest throughout ML training data. However, the scale of the attack is growing exponentially and its scope is beyond this document.
Conclusion
Although the attack involves tedious preparatory work, is not trivial to perform, does not work well in all circumstances, and has several practical limitations, it still poses a potential risk to users’ privacy.
One of the researchers who signed the paper, Evangelos Bitsikas, told BleepingComputer that for this experiment, they thought of themselves as grassroots attackers, meaning they were limited in terms of resources, machine learning knowledge and technical capacity.
This means that sophisticated attackers with more resources could theoretically have more impact and even moderate success in “open world” attack scenarios.
It should also be noted that the same team of researchers developed a similar timing attack last year and proved that it was possible to roughly locate users of popular instant messengers such as Signal, Threema and WhatsApp using message receipt reports.
[ad_2]
Source link
