[ad_1]

Cybersecurity firm Rubrik has confirmed that its data was stolen using a zero-day vulnerability in the Fortra GoAnywhere secure file transfer platform.
Rubrik is a cloud data management service that offers enterprise data backup and recovery services and disaster recovery solutions.
In a statement from Rubrik CISO Michael Mestrovitchon, the company revealed that it suffered a large-scale attack against GoAnywhere MFT devices worldwide using a zero-day vulnerability.
GoAnywhere is a secure web-based file transfer solution that allows businesses to securely transfer encrypted files with their partners while maintaining detailed audit logs of who accessed the files.
Rubrik claims the breach was contained in a non-production IT test environment and no customer data was affected.
“We have detected unauthorized access to a limited amount of information in one of our non-production IT test environments due to the GoAnywhere vulnerability,” the report says. Statement Item.
“It is important to note that, based on our current investigation, conducted with the assistance of third-party forensic experts, the unauthorized access did NOT include the data we secure on behalf of our customers through the products. Rubrik.”
Mestrovichon also says threat actors did not spread laterally to internal systems and the test environment was taken offline to prevent further intrusions.
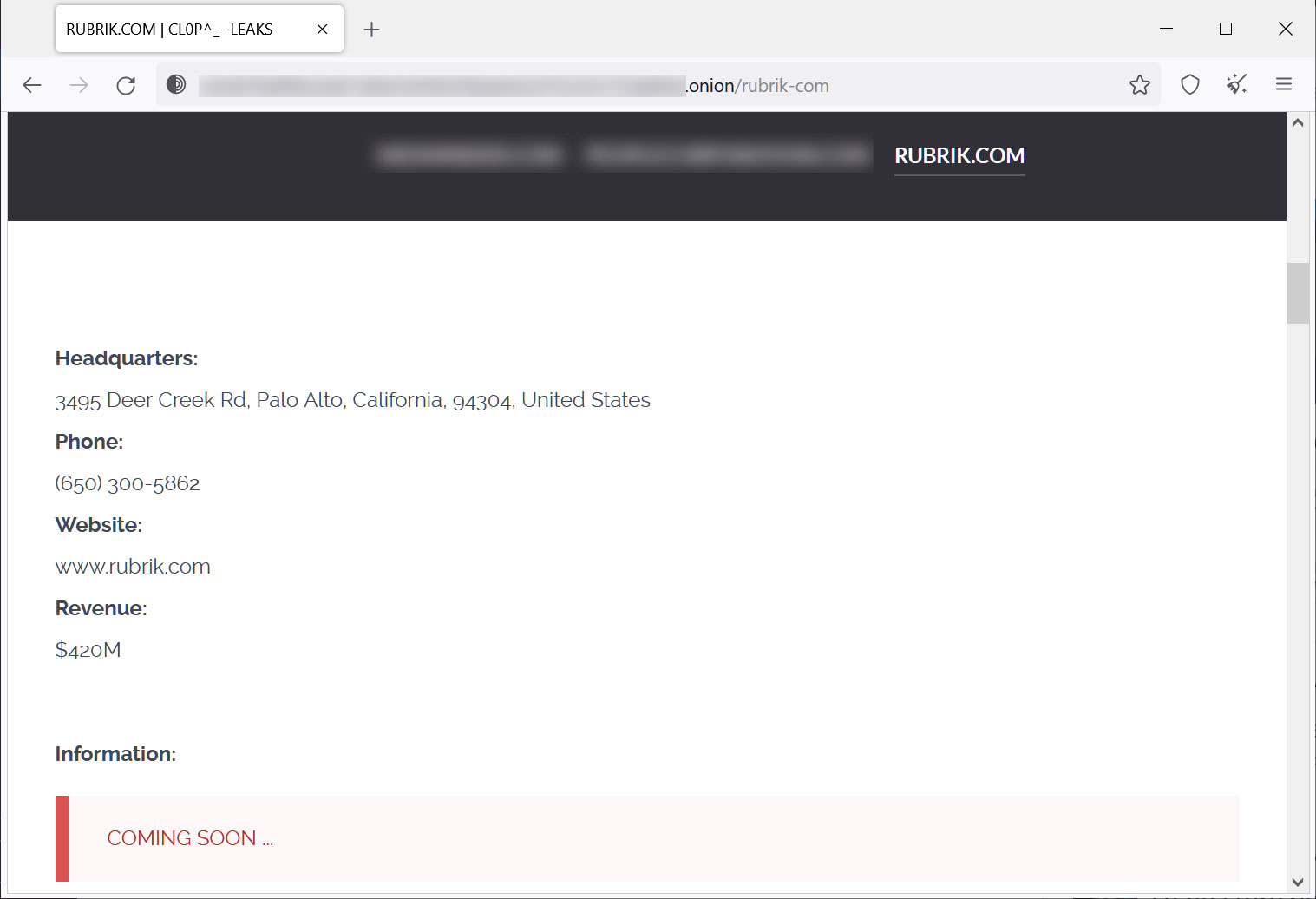
The disclosure comes after the Clop ransomware gang added Rubrik to its data leak site, sharing samples of stolen files and saying the data would soon be made public.
The screenshots shared by the threat actors are spreadsheets containing what appears to be internal Rubrik data, such as employee names, email addresses, and locations.
Source: BleepingComputer
THE Clop ransomware gang claimed responsibility for the Forta GoAnywhere attacks, telling BleepingComputer they breached 130 organizations to steal data for ten days.
The attacks took place earlier this year, with Fortra discloses in February that the vulnerability was being actively exploited and release a patch.
Last week the The Clop ransomware gang started sending email extortion demands to victims when they added them to their data leak site on Friday to apply leverage.
One of the listed victims, Hatch Bank, has already disclosed a data breach resulting from the attacks, saying the attackers stole customers’ names and social security numbers.
Another victim, Community Health Systems (CHS)also revealed they were hacked through the GoAnywhere vulnerability but are not listed on Clop’s site.
[ad_2]
Source link
