[ad_1]

The Royal ransomware gang has started testing a new encryptor called BlackSuit which shares many similarities with the regular operation encryptor.
Royal launched in January 2023, considered the direct successor to the infamous Operation Conti, which closed in June 2022.
This group is a private ransomware operation made up of pentesters, “Conti Team 1” affiliates, and affiliates they recruited from other ransomware gangs targeting businesses.
Since its launch, Royal ransomware became one of the most active operations, responsible for numerous attacks against the company.
Royal starts testing BlackSuit
Since late April, there have been rumors that the Operation Royal Ransomware was about to change its name to a new name. It got even worse after they started to feel pressure from law enforcement after attacking the city of Dallas, Texas.
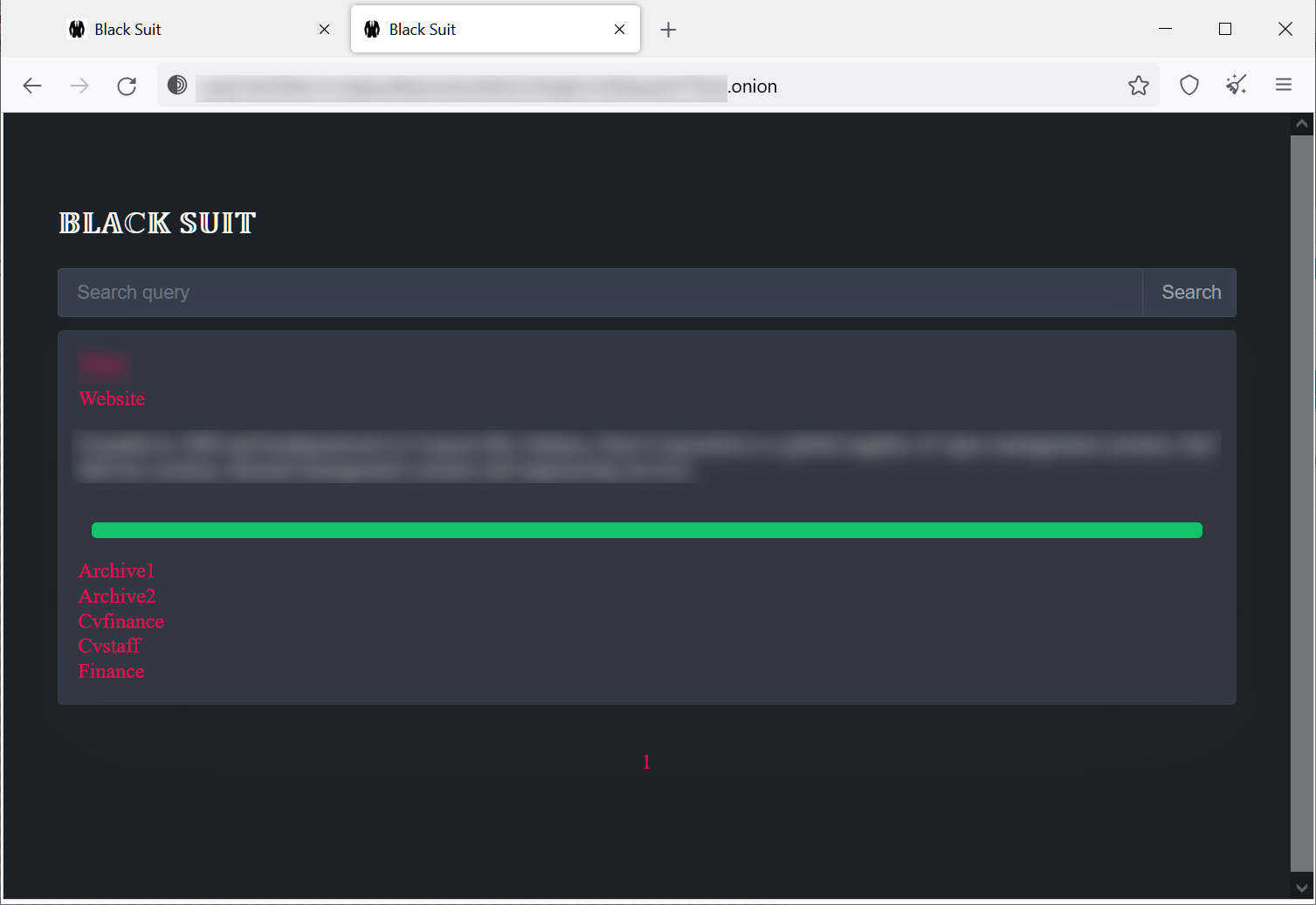
A new BlackSuit ransomware operation was discovered in May that used its own branded encryptor and Tor trading sites. This was believed to be the ransomware operation in which the Royal ransomware group would rebrand itself.
However, a rebranding never happened and Royal is still actively attacking the company while using BlackSuit in limited attacks.
“Royal: Conti’s direct heir, consisting of over 60 pentesters drawn from Conti’s “old guard” or recruited from various elite ransomware groups. Operating in small teams of 4-5 people, they remain loyal to their leaders: the administrator and the chief engineer.”, Yelisey Bohuslavskiy, Partner and Head of R&D at RedSense, published on LinkedIn.
“The group uses Royal and BlackSuit lockers, with Emotet and IcedID as precursors. They favor alternatives to CobaltStrike, particularly Sliver, and are developing custom precursor loaders.”
Bohuslavskiy further told BleepingComputer that it’s possible Royal is just testing a new encryptor, as they’ve been with other tools used by the group, including a new loader, IcedID, and an Emotet revitalization.
“They keep improving Emoted to try to revitalize it, and are working a lot on IcedID. Their experiments with new lockers are natural in that sense.” explained Bohuslavskiy.
“I think we’ll see more things like the Blacksuit soon. But so far it seems like the new Blacksuit Charger and Locker has been a failed experiment.”
As BlackSuit is a standalone operation, it’s possible that Royal might consider launching a subgroup focused on certain types of victims, or that it may be registered for a rebrand later.
Source: BleepingComputer
However, a brand change would no longer make sense, because recent report from Trend Micro showed clear similarities between BlackSuit and Royal Ransomware encryptors, which makes it difficult to convince anyone that this is a new ransomware operation.
These similarities include command line arguments, code similarities, file exclusions, and similar intermittent encryption techniques.
Although it is unclear how BlackSuit will be used, the ransomware is actively used in a small number of attacks.
BleepingComputer is aware of at least three attacks where the BlackSuit encryptor has been used, with ransoms, so far, less than $1 million.
Currently, the operation has one victim listed on its data leak site, but that could change quickly if the new encryptor gets more use.
At this point, we’ll have to wait and see if BlackSuit is, in fact, a failed experiment or the start of a new subgroup like Conti had with Diavol.
Either way, network advocates should know that this new operation is backed by Royal, who have proven expertise in breaching networks or deploying their ciphers.
[ad_2]
Source link
