[ad_1]

A threat actor called “RomCom” is targeting organizations supporting Ukraine and guests of the upcoming NATO summit due to start tomorrow in Vilnius, Lithuania.
The BlackBerry Research and Intelligence Team recently discovered two malicious documents posing as the Ukrainian organization of the World Congress and NATO summit related topics to lure selected targets.
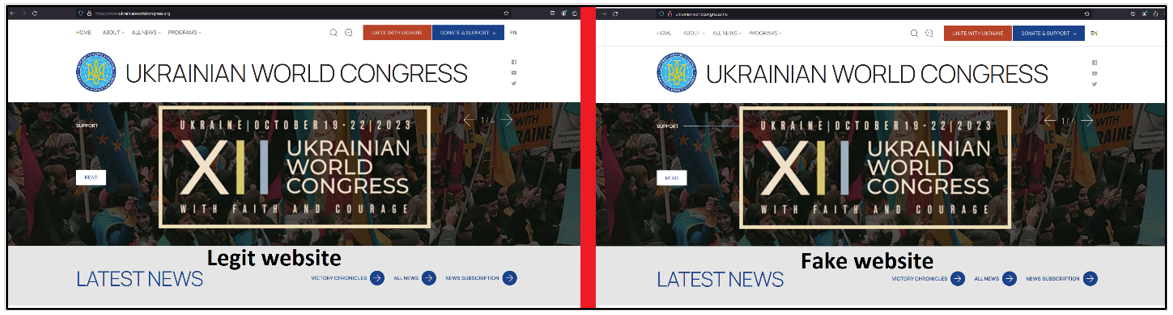
The attackers used a replica of the Ukrainian World Congress website hosted on an “.info” domain instead of the real one which uses an “.org” top-level domain.
The downloaded documents are accompanied by malicious code that exploits the RTF file format to initiate connections to external resources, possibly loading malware onto the victim’s system.
Blurred background RomCom
The RomCom malware was first discovered by Unit 42 in August 2022, which linked it to a subsidiary of Cuba Ransomware, an assessment that the Computer Emergency Response Team of Ukraine (CERT-UA) seemed to agree with based on an October 2022 report.
However, Analysis of BlackBerry from that era stated that the threat actors behind RomCom follow a rather globalized targeting approach, pointing out that Cuba ransomware has never been inclined towards hacktivism.
In November 2022, the cybersecurity firm discovered a new RomCom campaign who misused software brands and used fake English and Ukrainian language sites to target unsuspecting victims with malicious installers.
More recently, in May 2023, a report from Trend Micro on RomCom’s latest campaign showed that threat actors now impersonate legitimate software like Gimp and ChatGPT or create fake software developer sites to push their backdoor to victims via Google Ads and SEO techniques black.
Final campaign details
The latest campaign analyzed by BlackBerry uses download links on a typo-squatted domain for the Ukrainian World Congress site, likely promoted through spear-phishing, to infect visitors with malware.
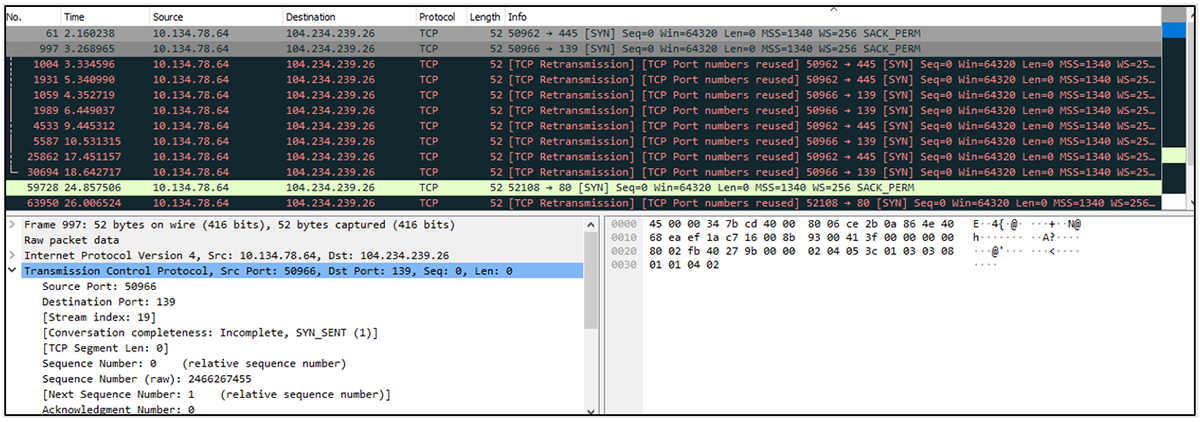
Documents downloaded from the fake website establish an outbound connection upon launch and download additional components from the attacker’s command and control (C2) server.
The additional component observed during research is a script using the Microsoft Support Diagnostic Tool (MSDT) Follina vulnerability (CVE-2022-30190).
“If successfully exploited, it allows an attacker to conduct a remote code execution (RCE)-based attack via the creation of a malicious .docx or .rtf document designed to exploit the vulnerability,” explains The report.
“This is achieved by leveraging the specially crafted document to run a vulnerable version of MSDT, which in turn allows an attacker to pass a command to the utility for execution,” the report adds.
“This includes doing so with the same level of privileges as the person who executed the malicious document. […] and is effective even when macros are disabled and even when a document is opened in Protected View.” – BlackBerry
The final stage of the attack is to load the RomCom backdoor onto the machine, which arrives as an x64 DLL file named “Calc.exe”.
RomCom connects to C2 to register the victim and returns details such as username, network adapter information, and RAM size of the compromised computer.
The backdoor eventually writes ‘security.dll’ to autorun on reboot for persistence and waits for commands from C2, which based on previous reports include data exfiltration, downloading additional payloads, deleting files or directories, creating processes with a spoofed PID, as well as starting a reverse shell.
BlackBerry believes that the analyzed campaign is either a renamed RomCom operation or one that includes core members of the old group supporting new threat activity.
The researchers’ report includes indicators of compromise for decoy documents, second-stage malware, and the IP addresses and domain used for the campaign.
[ad_2]
Source link
