[ad_1]

In the ever-changing ransomware landscape, we’ve seen new ransomware gangs emerge, threat actors return from a long absence, operations changing extortion tactics, and a wave of attacks on the business.
Over the past few weeks, we have reported new ransomware operations that have emerged in enterprise attacks, including the new Cactus, Akira, AR Group operations.
This week, a relatively new operation named Abyss hit L3Harris, a $17 billion defense firm, putting them in the spotlight.
We have also discovered MalasLocker, a ransomware operation targeting Zimbra servers since March. The hackers also have an unusual extortion tactic, requiring victims to donate to an approved charity to receive a decryptor and prevent a data leak.
It’s too early to tell whether or not the ransomware gang will stick to the arrangement or if it’s just an interesting marketing campaign.
Regarding the change in extortion tactics, a joint FBI and CISA report confirmed that the BianLian ransomware operation has switched to extortion only attacks after Avast released a decryptor.
We also learned about new attacks and important developments in previous ones:
Finally, researchers and law enforcement released new reports:
Contributors and those who provided new ransomware information and stories this week include: @serghei, @LawrenceAbrams, @PolarToffee, @malwhunterteam, @DanielGallagher, @Ionut_Ilascu, @demonslay335, @billtoulas, @Seifreed, @BleepinComputer, @fwosar, @VK_Intel, @struppigel, @BrettCallow, @TalosSecurity, @CrowdStrike, @pcrisk, @GroupIB, @zscaler, @MsftSecIntelAnd @juanbrodersen.
May 13, 2023
Capita Warns Customers to Assume Data Has Been Stolen
Business process outsourcing firm Capita is warning customers to assume their data was stolen in a cyberattack that affected its systems in early April.
May 15, 2023
Hypervisor Jackpotting Part 3: Lack of Antivirus Support Opens Door to Adversary Attacks
In April 2023, for example, CrowdStrike Intelligence identified a new RaaS program named MichaelKors, which provides affiliates with ransomware binaries targeting Windows and ESXi/Linux systems. Other RaaS platforms capable of targeting ESXi environments, such as Nevada ransomware, have also been released.
New RA Group ransomware targets US organizations in double extortion attacks
A new ransomware group named “RA Group” targets pharmaceutical, insurance, wealth management and manufacturing companies in the United States and South Korea.
Ransomware gang steals data from 5.8 million PharMerica patients
Pharmaceutical services provider PharMerica has disclosed a massive data breach affecting more than 5.8 million patients, exposing their medical data to hackers.
You’ve been kept in the dark (web): exposing Qilin’s RaaS program
In this blog, we aim to provide a detailed breakdown of the ransomware group – Qilin (aka Agenda ransomware). This group, discovered in August 2022, targets companies in critical sectors with ransomware written in the Rust* and Go* (Golang) languages.
Cyberattack contained at LACROIX
LACROIX announces having intercepted during the night of Friday May 12 to Saturday May 13 a cyberattack targeted on the French (Beaupréau), German (Willich) and Tunisian (Zriba) sites of the Electronics activity. Measures to secure all the other sites of the Group were immediately taken.
New variant of STOP ransomware
Risk found a new STOP ransomware variant that adds the .xash extension.
New Variant of VoidCrypt Ransomware
PCrisk has found a new VoidCrypt ransomware variant that adds the .cyb extension and drops a ransom note named Decryption-guide.txt.
New variant of Phobos ransomware
PCrisk has found a new Phobos ransomware variant that adds the .Black Rock extension.
May 16, 2023
Russian ransomware subsidiary accused of critical infrastructure attacks
The US Department of Justice has filed charges against a Russian citizen named Mikhail Pavlovich Matveev (also known as Wazawaka, Uhodiransomwar, m1x, and Boriselcin) for his involvement in three ransomware operations targeting victims across the United States. United.
CryptNet Ransomware Technical Analysis
Zscaler ThreatLabz followed a new ransomware group known as CryptNet which emerged in April 2023. The group claims to exfiltrate data before performing file encryption and hosts a data leak site hosted on a hidden service Tor which currently contains two victims.
New STOP ransomware variants
PCrisk has found new STOP ransomware variants that add the .xatz And .xaro expansions.
New variant of MedusaLocker ransomware
PCrisk has found a new MedusaLocker ransomware variant that adds the .olsavelock31 (number may differ) extension and drops a ransom note named How_to_back_files.html.
May 17, 2023
MalasLocker ransomware targets Zimbra servers and demands charity donation
A new ransomware operation hacks Zimbra servers to steal emails and encrypt files. However, instead of demanding ransom payment, threat actors claim to demand donation to charity to provide encryptor and prevent data leakage.
FBI confirms switch of BianLian ransomware to extortion-only attacks
A joint cybersecurity advisory issued by government agencies in the United States and Australia and published by the Cybersecurity and Infrastructure Security Agency (CISA) alerts organizations to the latest tactics, techniques, and procedures (TTPs) used by the BianLian ransomware group .
ScanSource says ransomware attack causes multi-day outages
Technology provider ScanSource has announced that it has been the victim of a ransomware attack affecting some of its systems, business operations and customer portals.
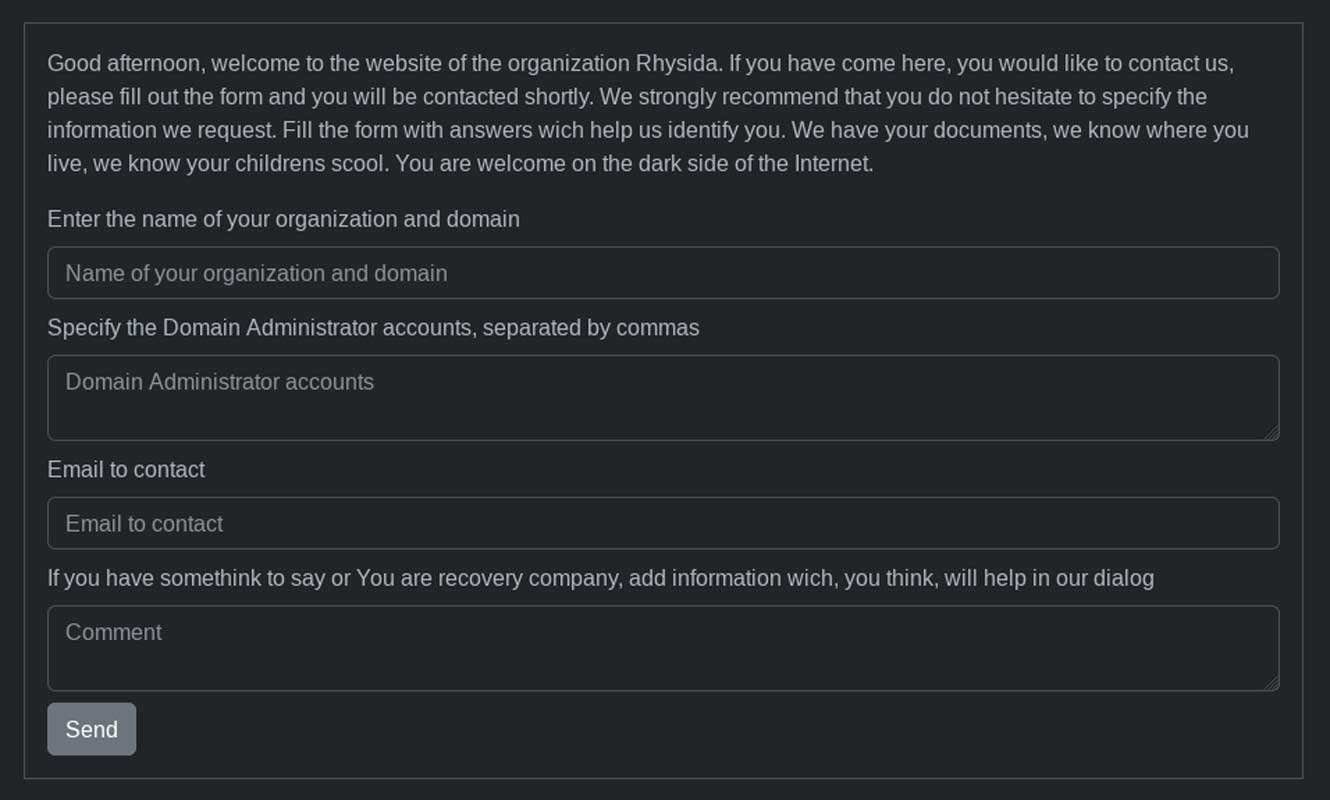
New Rhysida ransomware
MalwareHunterTeam found the new Rhysida ransomware operation.
May 18, 2023
Cyber attack on pharmacies: hackers give themselves a month to pay the ransom or publish the stolen information
Lockbit, the cybercriminal group that carried out the attack on the Farmalink prescription drug system, gave itself a deadline of about a month to negotiate a ransom payment and return the stolen information. After this period, they will publish the data.
New variant of Snatch ransomware
PCrisk has found a new Snatch ransomware variant that adds the .adfuhbazi extension and drops a ransom note named HOW TO RESTORE YOUR ADFUHBAZI.TXT FILES.
May 19, 2023
Dish Network likely paid ransom after recent ransomware attack
Dish Network, a US television provider, most likely paid a ransom after being hit by a ransomware attack in February based on wording used in data breach notification letters sent to affected employees.
Microsoft: Notorious FIN7 hackers return in Clop ransomware attacks
A group of financially motivated cybercriminals known as FIN7 resurfaced last month, with Microsoft threat analysts associating it with attacks whose end goal was to deploy Clop ransomware payloads on the networks of victims.
New AlphaWare ransomware
PCrisk has found a new AlphaWare ransomware that adds the .alphaware extension and drops a ransom note named readme.txt.
It’s all for this week ! I hope everyone is having a good weekend!
[ad_2]
Source link
