[ad_1]

Law enforcement has arrested a suspect believed to be a key member of cybercrime group OPERA1ER, which has targeted mobile banking and financial institutions in malware, phishing and email compromise campaigns professionals (BEC).
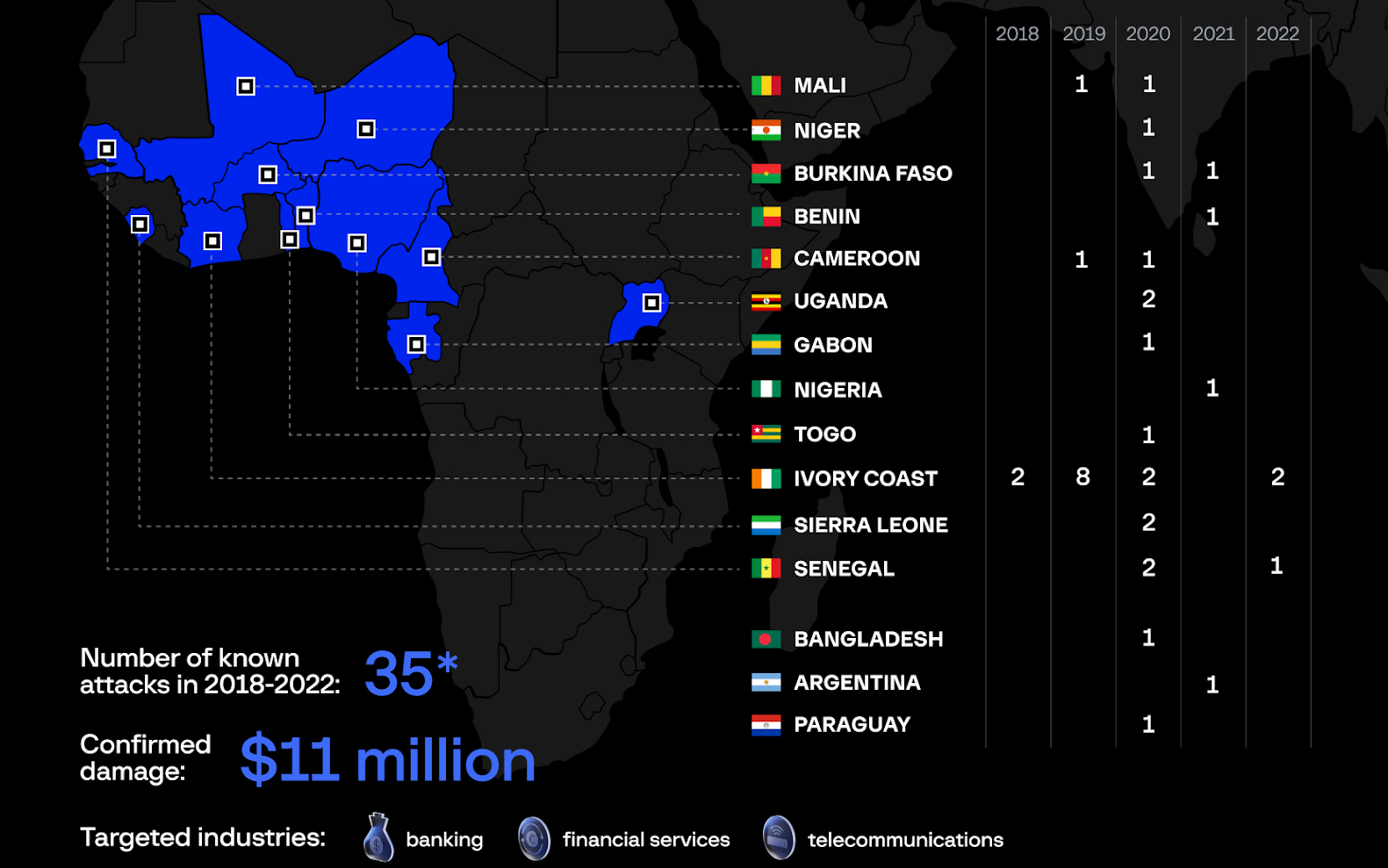
The gang, also known as NX$M$, DESKTOP Group and Common Raven, is believed to have stolen between $11 million and $30 million over the past four years in more than 30 attacks spanning 15 countries in Africa , Asia and Latin America. .
The suspect was arrested by the Ivorian authorities in early June following a joint law enforcement action dubbed Operation Nervone with the help of AFRIPOL, Interpol’s Cybercrime Directorate, the cybersecurity Group-IB and the telecommunications operator Orange.
Other information that helped the investigation was shared by the United States Secret Service Criminal Investigations Division and cybersecurity researchers at Booz Allen Hamilton DarkLabs.
“According to INTERPOL’s Africa Cyber Threat Assessment 2022 report, cybercrime is a growing threat in the West African region, with victims worldwide. Operation NERVONE highlights the INTERPOL’s commitment to proactively address the threat of cybercrime in the region,” Interpol said. said Today.
“Operation Nervone was supported by two key INTERPOL initiatives: the African Joint Operation Against Cybercrime and the INTERPOL African Union Support Program in relation to AFRIPOL, funded respectively by the UK Department for Foreign, Commonwealth and Development Affairs and the German Federal Foreign Office.”
Group-IB analysts and the CERT-CC service at Orange, followed by the OPERA1ER group since 2019, have linked threat actors to more than 35 successful attacks between 2018 and 2022, about a third of them completed in 2020.
OPERA1ER members speak mostly French and are believed to be operating from Africa, and they rely on various tools in their attacks, including open source solutions, common malware, and frameworks such as Metasploit and Cobalt Strike.
However, initial access to the targets’ networks is gained through spear phishing emails that exploit popular topics such as bills or postal delivery notifications and deliver a wide range of first-stage malware, including Netwire, BitRAT, venomRAT, AgentTesla, Remcos, Neutrino, BlackNET and Venom RAT, as well as password sniffers and dumpers.
OPERA1ER has been observed maintaining access to compromised networks for a period ranging from three to twelve months, sometimes targeting the same company multiple times.
They also typically focus on operator accounts that control large sums of money, using stolen credentials to transfer funds to channel user accounts before redirecting them to subscriber accounts. under their control. The group withdraws stolen money in cash through a large network of ATMs during holidays or weekends to avoid detection.
Researchers at Symantec also found links between OPERA1ER and a group of cybercriminals they track like Bluebottle who used a signed Windows driver in attacks against at least three banks in French-speaking African countries.
“Any attempt to investigate a sophisticated threat actor such as OPERA1ER, which has stolen millions from financial services companies and telecommunications providers around the world, requires a highly coordinated effort between public and private sector agencies. “, said Dmitry Volkov, CEO of IB Group.
“The success of Operation Nervone illustrates the importance of threat data sharing, and through our collaboration with INTERPOL, Orange-CERT-CC and private and public sector partners, we have been able to collectively reconstruct the ‘whole puzzle.’
[ad_2]
Source link
