[ad_1]

The Play ransomware group has developed two custom tools in .NET, namely Grixba and VSS Copying Tool, which it uses to improve the effectiveness of its cyberattacks.
Both tools allow attackers to enumerate users and computers on compromised networks, gather information about remote security, backup and administration software, and easily copy files from Volume Shadow Copy Service (VSS ) to bypass locked files.
Symantec security researchers discovered and analyzed the new tools and shared their findings with BleepingComputer before publishing their report.
New custom tools
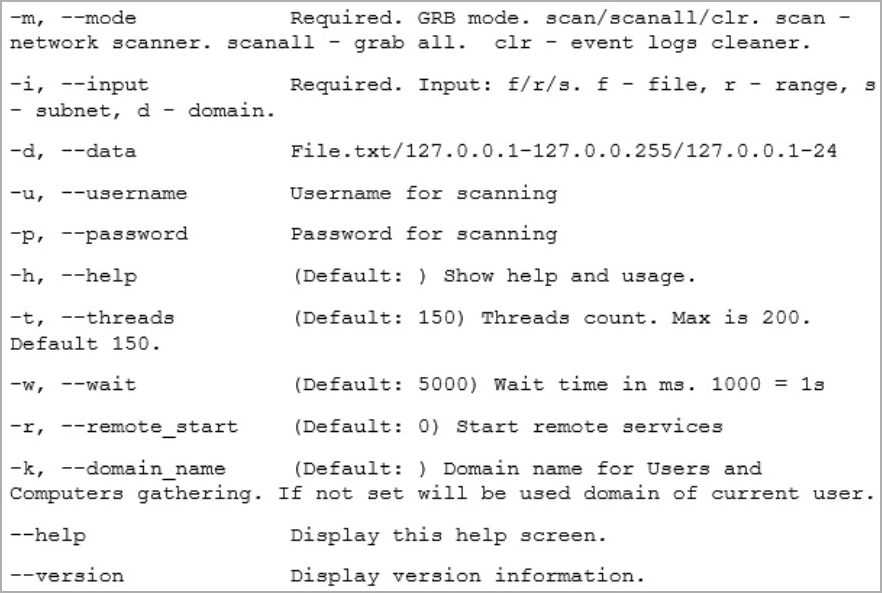
Grixba is a network analysis and information theft tool used to enumerate users and computers in a domain. It also supports a “scan” mode that uses WMI, WinRM, Remote Registry, and Remote Services to determine what software is running on network devices.
While running the scan function, Grixba will check anti-virus and security programs, EDR suites, backup tools, and remote administration tools. In addition, the scanner checks common office applications and DirectX, possibly to determine the type of computer scanned.
The tool saves all collected data into CSV files, compresses it into a ZIP archive, and then exfiltrates it to the attackers’ C2 server, giving them vital information on how to plan the next steps of the attack.
Source: Symantec
The second custom tool spotted by Symantec in Play ransomware attacks is the VSS Copy Tool, which allows attackers to interact with the Volume Shadow Copy Service (VSS) via API calls using ‘A AlphaVSS .NET Library.
Volume Shadow Copy Service is a Windows feature that allows users to create system snapshots and point-in-time backup copies of their data and restore them in the event of data loss or system corruption.
The VSS Copy Tool allows Play ransomware to steal files from existing Volume Shadow Copies, even when those files are in use by applications.
Both tools analyzed by Symantec were written using the Costura .NET development tool, which can create standalone executables that require no dependencies, making it easier to deploy to compromised systems.
Usage of customized tools by Play ransomware indicates that the notorious threat actor aims to increase the effectiveness of its attacks and perform its malicious tasks more efficiently.
Since the start of the year, Play ransomware has claimed several high-profile victims, including the City of Oakland in California, A10 networks, Arnold ClarkAnd rack space.
[ad_2]
Source link
