[ad_1]
Cybersecurity researchers and IT administrators have raised concerns about Google’s new ZIP and MOV internet domains, warning that threat actors could use them for phishing attacks and malware distribution.
Earlier this month, Google presented eight new top-level domains (TLDs) that can be purchased to host websites or email addresses.
The new domains are .dad, .esq, .prof, .phd, .nexus, .foo, and for the purpose of our article, the .zip and .mov domain TLDs.
While the ZIPPER And MOV TLDs have been available since 2014, only this month they became generally available, allowing anyone to purchase a domain, like bleepingcomputer.zip, for a website.
However, these domains could be perceived as risky as TLDs are also file extensions commonly shared in forum posts, messages and chat, which will now be automatically converted to URLs by some online platforms or applications.
Preoccupation
Two common file types seen online are ZIP archives and MPEG 4 videos, which have filenames ending in .zip (ZIP archive) or .mov (video file).
Therefore, it is very common for people to post instructions containing filenames with .zip and .mov extensions.
However, now that it’s TLDs, some email platforms and social media sites automatically convert filenames with .zip and .mov extensions to URLs.
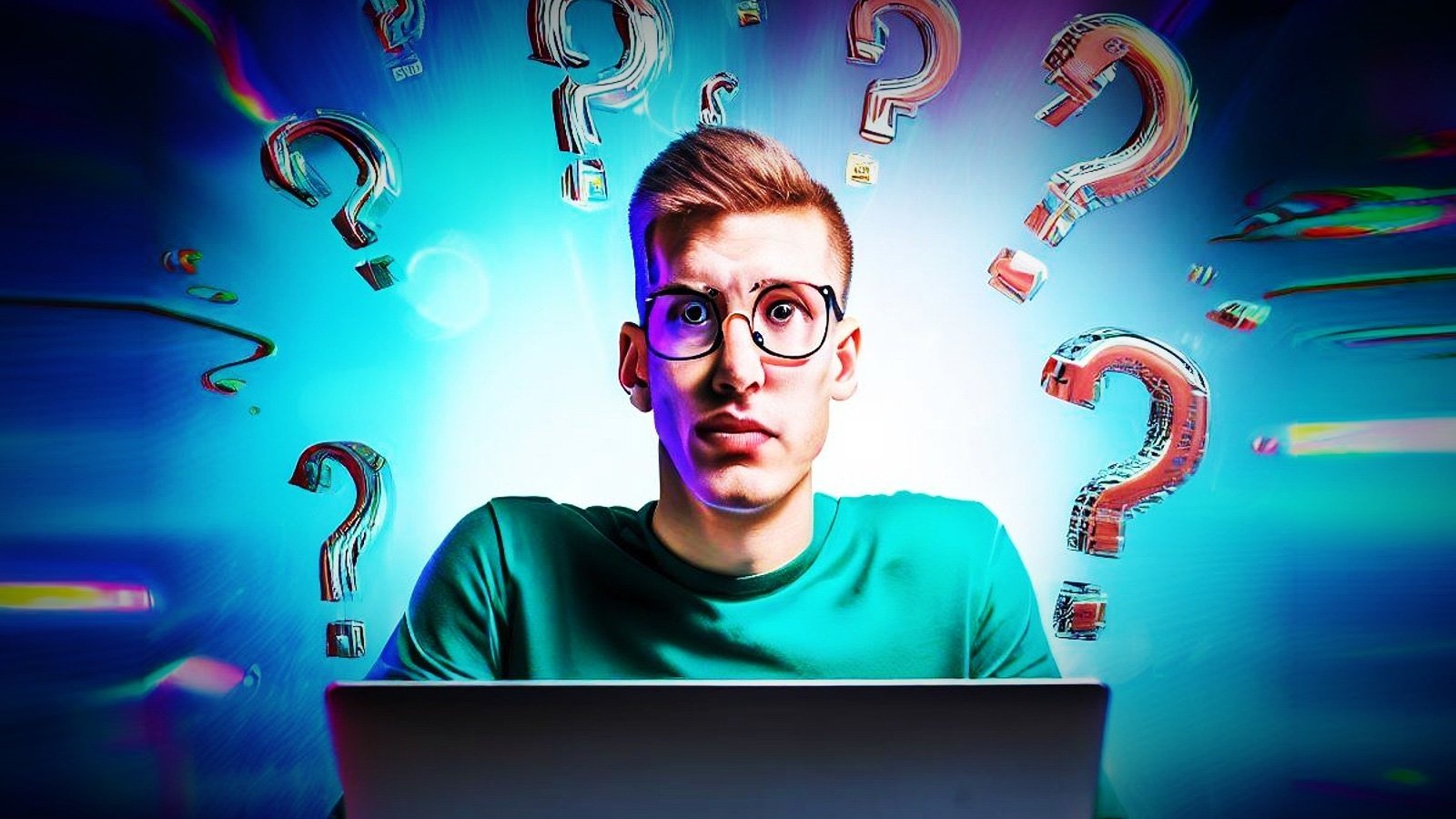
For example, on Twitter, if you send someone instructions on how to open a zip file and access a MOV file, the innocuous filenames are converted to URLs, as shown below.
Source: BleepingComputer
When people see URLs in the instructions, they usually think the URL can be used to download the associated file and can click the link. For example, linking filenames to downloads is how we typically provide instructions for BleepingComputer in our articles, tutorials, and discussion forums.
However, if a threat actor had a .zip domain with the same name as a linked filename, a person might visit the site by mistake and fall for a phishing scam or download malware, thinking that the URL is safe because it comes from a trusted source.
While threat actors are highly unlikely to register thousands of domains to catch a few victims, it only takes one company employee mistakenly installing malware for an entire network to be affected.
Abuse of these domains is not theoretical, with a cyber-intel society Silent push labs already discovered what appears to be a phishing page at microsoft-office[.]zip attempts to steal Microsoft account credentials.
Cybersecurity researchers have also started playing with domains, with Bobby Rauch research publication on developing compelling phishing links using Unicode characters and user info delimiter (@) in URLs.
Rauch’s research shows how threat actors can create phishing URLs that look like legitimate file download URLs on GitHub, but actually take you to a v1.27.1 website[.]zip when clicked as shown below.
https://github.com/kubernetes/kubernetes/archive/refs/tags/@v1.27.1.zipConflicting opinions
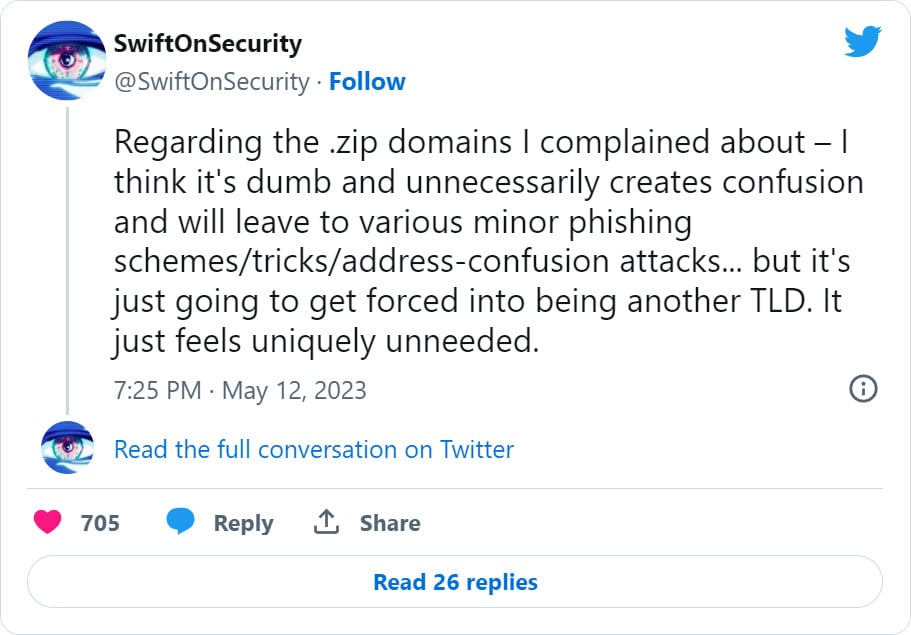
These developments have sparked debate among developers, security researchers, and IT administratorswith some believing that the fears are unwarranted and others believing that ZIP and MOV TLDs add unnecessary risk to an already risky online environment.
People started registering .zip domains associated with common ZIP archives, such as update.zip, financial statement.zip, setup.zip, attachment.zip, officeupdate.zipAnd backup.zipto display information about the risks of ZIP domains, to you RickRoll, or to share harmless information.
Open source developer Matt Holt has also asked that the ZIP TLD be removed from Mozilla List of public suffixesa list of all public top-level domains to integrate into apps and browsers.
However, the PSL community was quick to explain that although there may be a slight risk associated with these TLDs, they are still valid and should not be removed from the PSL as this will affect the operation of legitimate sites.
“Removing existing TLDs from the PSL for this reason would simply be a mistake. This list is used to a lot different reasons, and just because these inputs are bad for a very specific use case, they are still needed for (almost) all the others,” explained software engineer Felix Fontein.
“These are legitimate TLDs in the ICP3 root. This will not continue,” added Jothan Frakes, head of PSL.
“Really, the concerns expressed are more of a glaring example of the disconnect between the developer community and domain name security and governance, where they would benefit from greater engagement within ICANN.”
Meanwhile, other security researchers and developers have said they believe fears about these new domains are overblown.
When BleepingComputer contacted Google about these concerns, they said the risk of file name and domain name confusion was nothing new and that browser mitigations were in place to protect users from abuse.
“The risk of confusion between domain names and file names is not new. For example, 3M’s Command products use the domain name order.com, which is also an important program on MS DOS and early versions of Windows. Apps have mitigations for this (such as Google Safe Browsing), and those mitigations will work for TLDs such as .zip.
At the same time, new namespaces provide extended naming possibilities such as community.zip And url.zip. Google takes phishing and malware seriously and Google Registry has existing mechanisms to suspend or remove malicious domains in all of our TLDs, including .zip. We will continue to monitor the use of .zip and other TLDs and if new threats emerge, we will take appropriate action to protect users.” – Google.
What should you do?
The reality is that you don’t need to do anything more than what you already do to protect yourself from phishing sites.
As everyone should already know, it’s never safe to click on links from people or download files from sites you don’t trust.
Like any link, if you see a .zip or .mov link in a message, search for it before clicking on it. If you’re still not sure if the link is safe, don’t click on it.
By following these simple steps, the impact of new TLDs will be minimal and will not significantly increase your risk.
However, exposure to these links will likely increase as more apps automatically turn ZIP and MOV filenames into links, giving you another thing to watch out for when online.
[ad_2]
Source link