[ad_1]

Security researchers have discovered a new backdoor called WhiskerSpy being used in a campaign by a relatively new advanced threat actor being tracked as Earth Kitsune, known to target individuals showing an interest in North Korea.
The actor used a tried-and-true method and picked victims from visitors to a professional North Korean website, a tactic known as the waterhole attack.
The new operation was uncovered late last year by researchers from cybersecurity firm Trend Micro, who have been tracking Earth Kitsune activity since 2019.
Attack at the watering hole
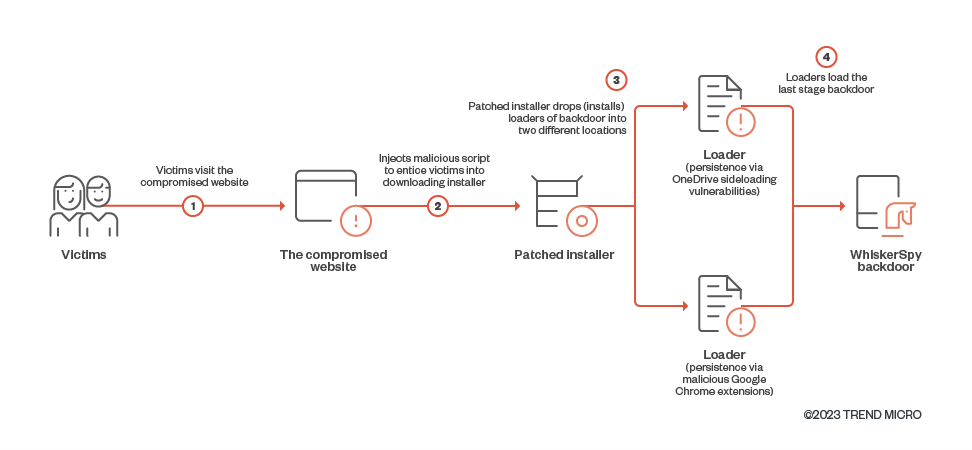
According to Trend Micro, WhiskerSpy was delivered when visitors tried to watch videos on the website. The attacker compromised the website and injected a malicious script that required the victim to install a video codec for the media to play.
To avoid suspicion, the threat actor modified a legitimate codec installer to eventually load “a previously invisible backdoor” onto the victim’s system.
source: Trend Micro
The researchers claim that the threat actor only targeted website visitors with IP addresses from Shenyang, China; Nagoya, Japan; and Brazil.
It is likely that Brazil was only used to test the waterhole attack using a VPN connection and that the real targets were visitors from both cities in China and Japan. Affected victims would receive the fake error message below which prompts them to install a codec to watch the video.
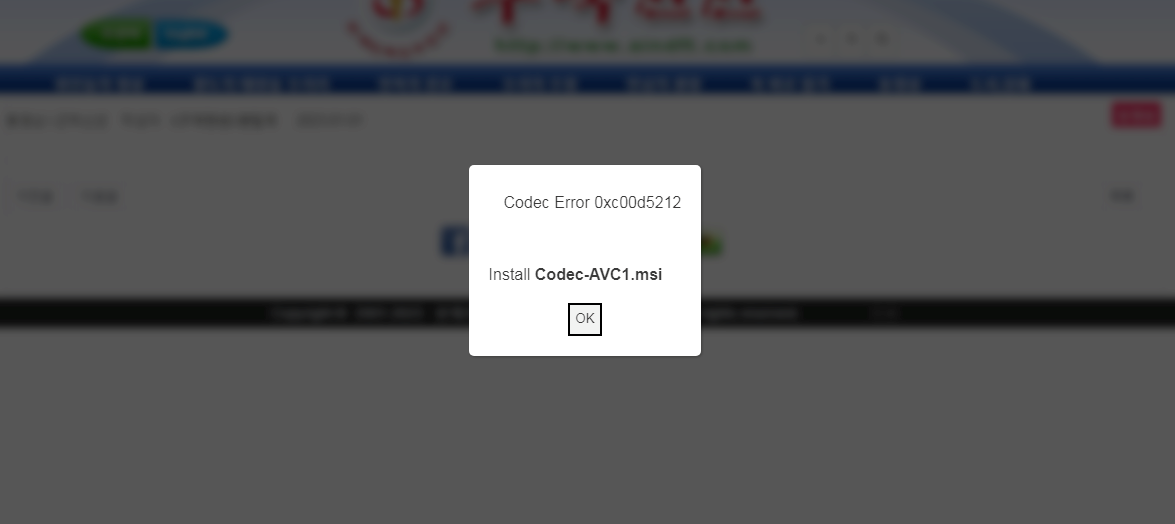
In reality, the codec is an MSI executable that installs on the victim’s computer shellcode that triggers a series of PowerShell commands that lead to the deployment of the WhiskerSpy backdoor.
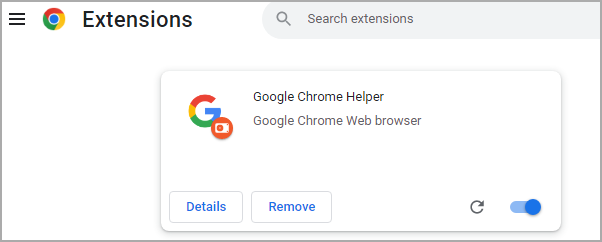
THE researchers note this persistence technique used by Earth Kitsune in this campaign abuses the native Google Chrome mail host and installs a malicious Google Chrome extension called Google Chrome Helper.
The role of the extension is to allow the execution of the payload each time the browser is started.
The other method to achieve persistence is to take advantage of OneDrive’s sideloading vulnerabilities that allow a malicious file (fake “vcruntime140.dll”) to be dropped into the OneDrive directory.
Details of WhiskerSpy
WhiskerSpy is the main payload used in the latest “Earth Kitsune” campaign, providing remote operators with the following features:
- interactive shell
- download a file
- upload a file
- delete file
- list files
- take a screenshot
- load the executable and call its export
- inject shellcode into a process
The backdoor communicates with the command and control server (C2) using a 16-byte AES key for encryption.
WhiskerSpy periodically connects to C2 for updates on its status and the server can respond with instructions for the malware, such as running shell commands, injecting code into another process, exfiltrating specific files, taking screenshots of screen.
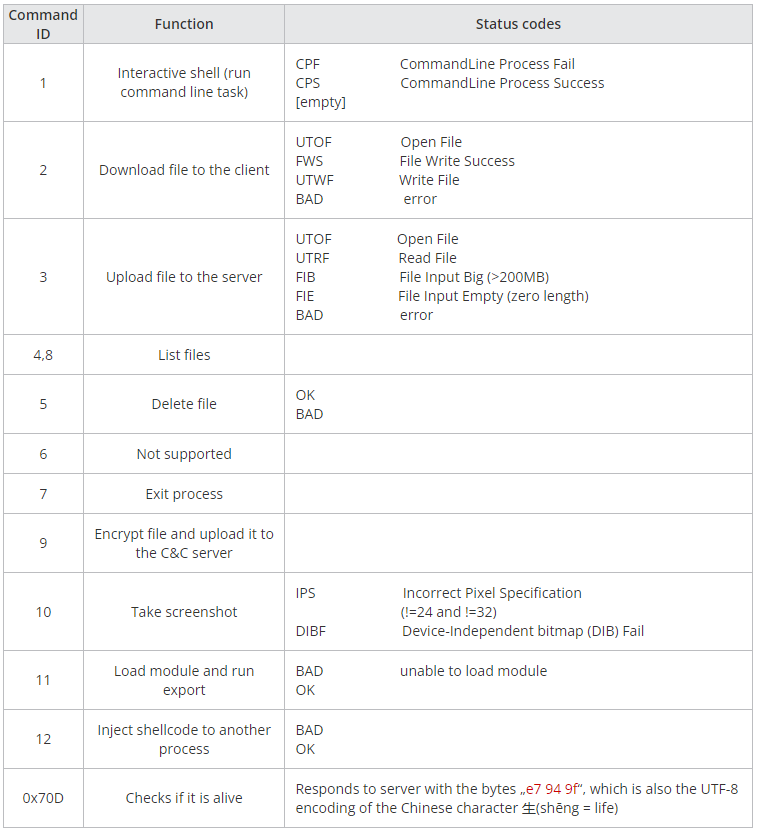
Trend Micro discovered an earlier version of WhiskerSpy that uses FTP protocol instead of HTTP for C2 communication. This old variant also checks for the presence of a debugger at runtime and notifies the C2 with the appropriate status code.
Note, the confidence of the researchers in the attribution of this watering hole attack to Earth Kitsune is medium but the modus operandi and the targets are similar to the activities previously associated to the group.
[ad_2]
Source link
