[ad_1]

A new ransomware operation named Royal is growing rapidly, targeting businesses with ransom demands ranging from $250,000 to over $2 million.
Royal, aka Royal Zeon, is a relatively new operation that was launched in February 2022 and consists of a group of vetted and experienced ransomware actors from previous operations.
Unlike most active ransomware operations, Royal does not operate as a Ransomware-as-a-Service but is rather a private group with no affiliates.
Vitali Kremez, CEO of AdvInteltold BleepingComputer that they use other first-boot ransomware operation encryptors, such as LockBit and BlackCat.
Shortly after, the cybercrime firm started using its own encryptors, the first being Zeon, then from mid-September 2022 they switched to the alias “Royal” in a new encryptor.
How Royal Rapes His Victims
Since June, Operation Royal Zeon has been operating in the shadows, using no data leak sites and keeping news of their attacks quiet.
However, as the gang has become more active this month, victims have emerged at BleepingComputerand a sample was uploaded to VirusTotal.
In conversations with Kremez and a victim, BleepingComputer created a better picture of how the gang operates.
According to Kremez, the Royal Zeon group uses callback phishing attacks where they impersonate food delivery services or software providers in emails claiming to be fake subscription renewals.
These phishing emails contain phone numbers that the victim can contact to cancel the alleged subscription, but, in reality, it is a number of a service hired by the threat actors.
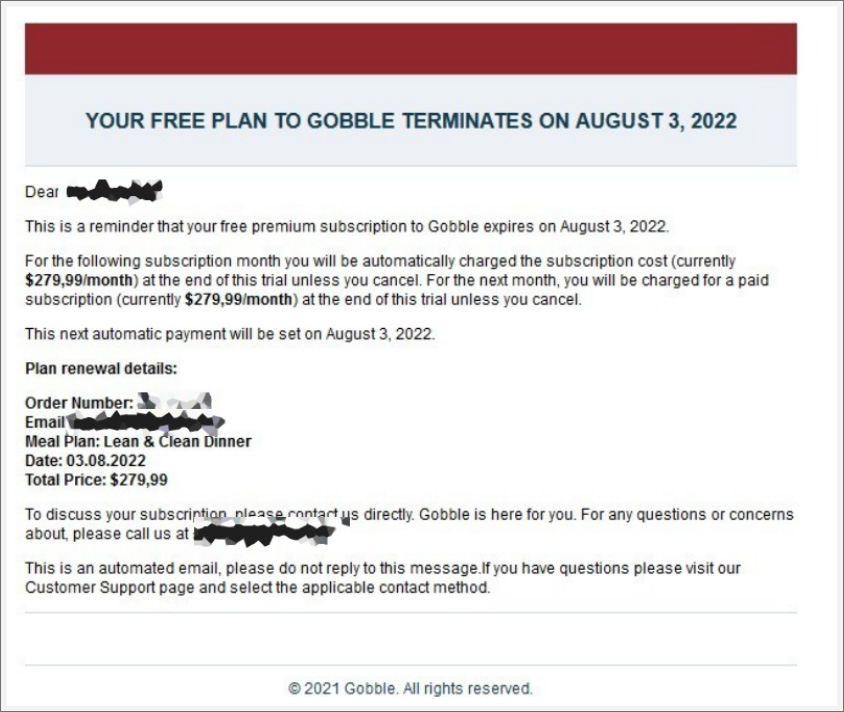
Source: Adv Intel
When a victim calls the number, threat actors use social engineering to convince the victim to install remote access software, which is used to gain initial access to the corporate network.
A royal victim who spoke to BleepingComputer shared that threat actors breached their network using a vulnerability in their custom web application, showing that threat actors are also getting creative with how they access a network.
Once they gain access to a network, they perform the same activities commonly used by other human-operated ransomware operations. They deploy Cobalt Strike for persistence, harvest credentials, spread laterally in the Windows domain, steal data, and ultimately encrypt devices.
When encrypting files, Royal Crypt will add the .Royal extension to filenames of encrypted files. For example, test.jpg would be encrypted and renamed to test.jpg.royal as shown below.
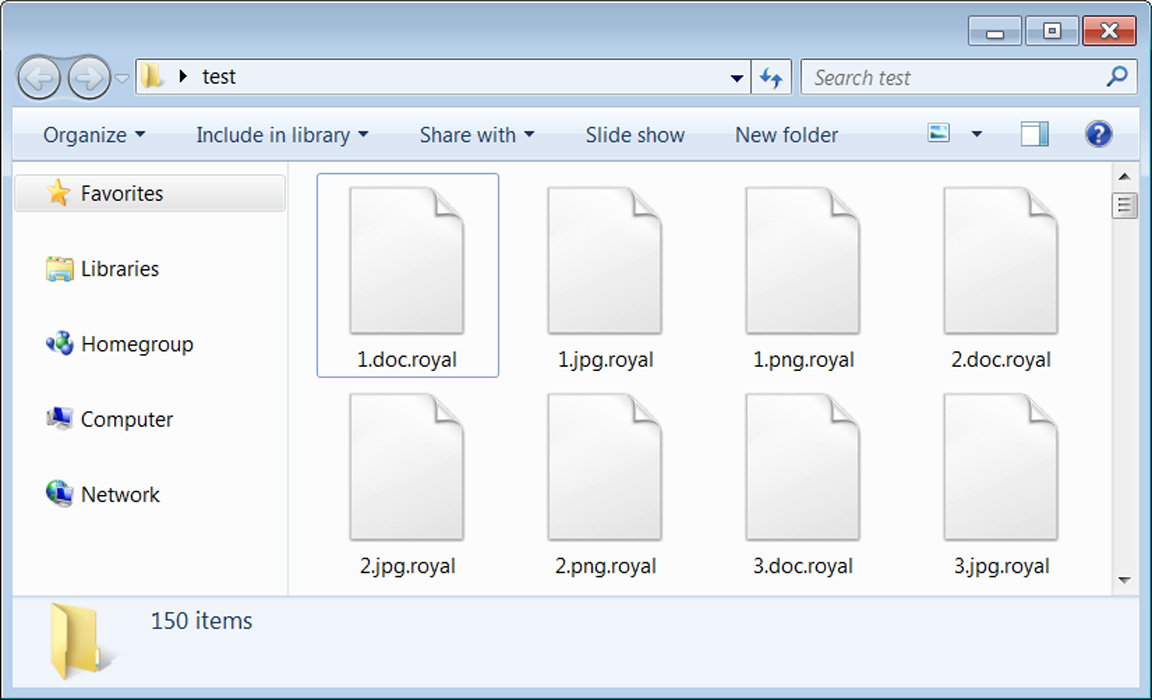
Source: BleepingComputer
A victim of Royal also told BleepingComputer that they target virtual machines by directly encrypting their virtual disk (VMDK) files. Threat actors then print the ransom notes on network printers or create them on encrypted Windows devices.
These ransom notes are named README.TXT and contain a link to the victim’s private Tor trading page at royal2xthig3ou5hd7zsliqagy6yygk2cdelaxtni2fyad6dpmpxedid.onion. XXX in the ransom note below has been redacted but is unique to the victim.
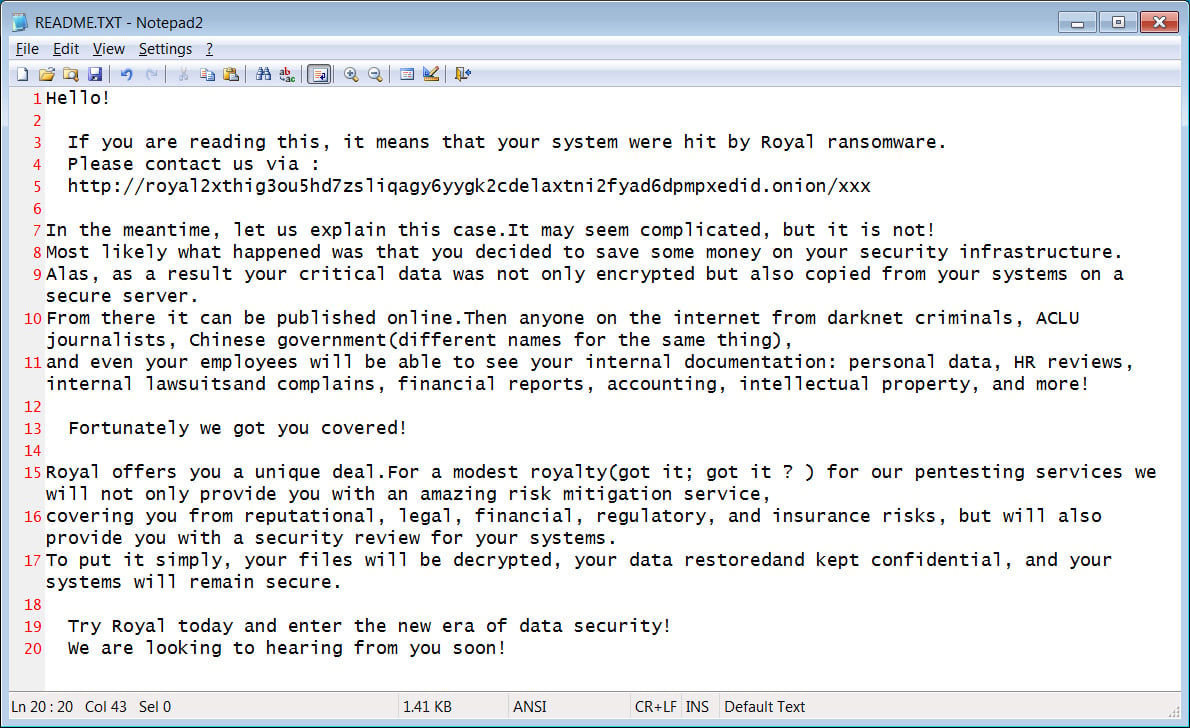
Source: BleepingComputer
The Tor trading site is nothing special, merely containing a chat screen where a victim can communicate with Royal ransomware operators.
As part of these negotiations, the ransomware gang will provide the ransom note, with ransom demands ranging from $250,000 to over $2 million.
The ransomware gang will also usually decrypt a few files for the victims to prove that their decryptor works and share the file lists of the stolen data.
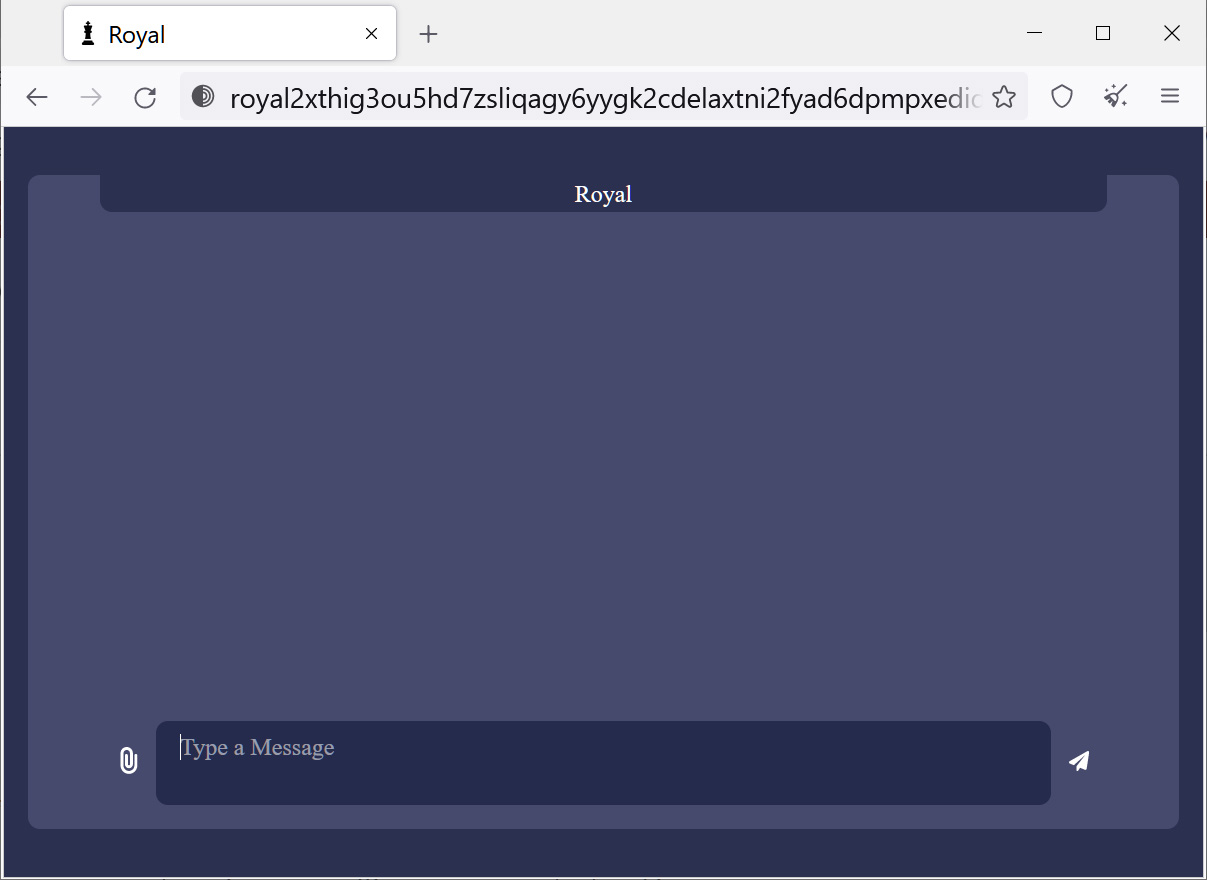
Source: BleepingComputer
BleepingComputer is not aware of successful payments and has not seen a decryptor for this ransomware family.
While the group previously had a data leak site at zeonrefpbompx6rwdqa5hxgtp2cxgfmoymlli3azoanisze33pp3x3yd.onion when operating under the Zeon name, it does not appear that a site has launched under the Royal brand at this time.
However, network, Windows, and security administrators are strongly advised to keep an eye on this group, as they are rapidly escalating their operations and will likely become one of the most prominent business-targeting ransomware operations.
[ad_2]
Source link
