[ad_1]
New ransomware attacks targeting organizations in Ukraine first detected on Monday have been linked to the notorious Russian military threat group Sandworm.
The Slovak software company ESET, which was the first to spot this wave of attacks, claims that the ransomware they named RansomBoggs was found on the networks of several Ukrainian organizations.
“Although the malware written in .NET is new, its deployment is similar to previous attacks attributed to Sandworm,” ESET Research Labs said. said.
“There are similarities to previous Sandworm attacks: a PowerShell script used to distribute .NET ransomware from the domain controller is almost identical to the one seen last April during Industrial2’s attacks on the energy.”
The PowerShell script used to deploy RansomBoggs payloads to victims’ networks is known as POWERGAP and was also behind the CaddyWiper destructive malware delivery in attacks on Ukrainian organizations in March.
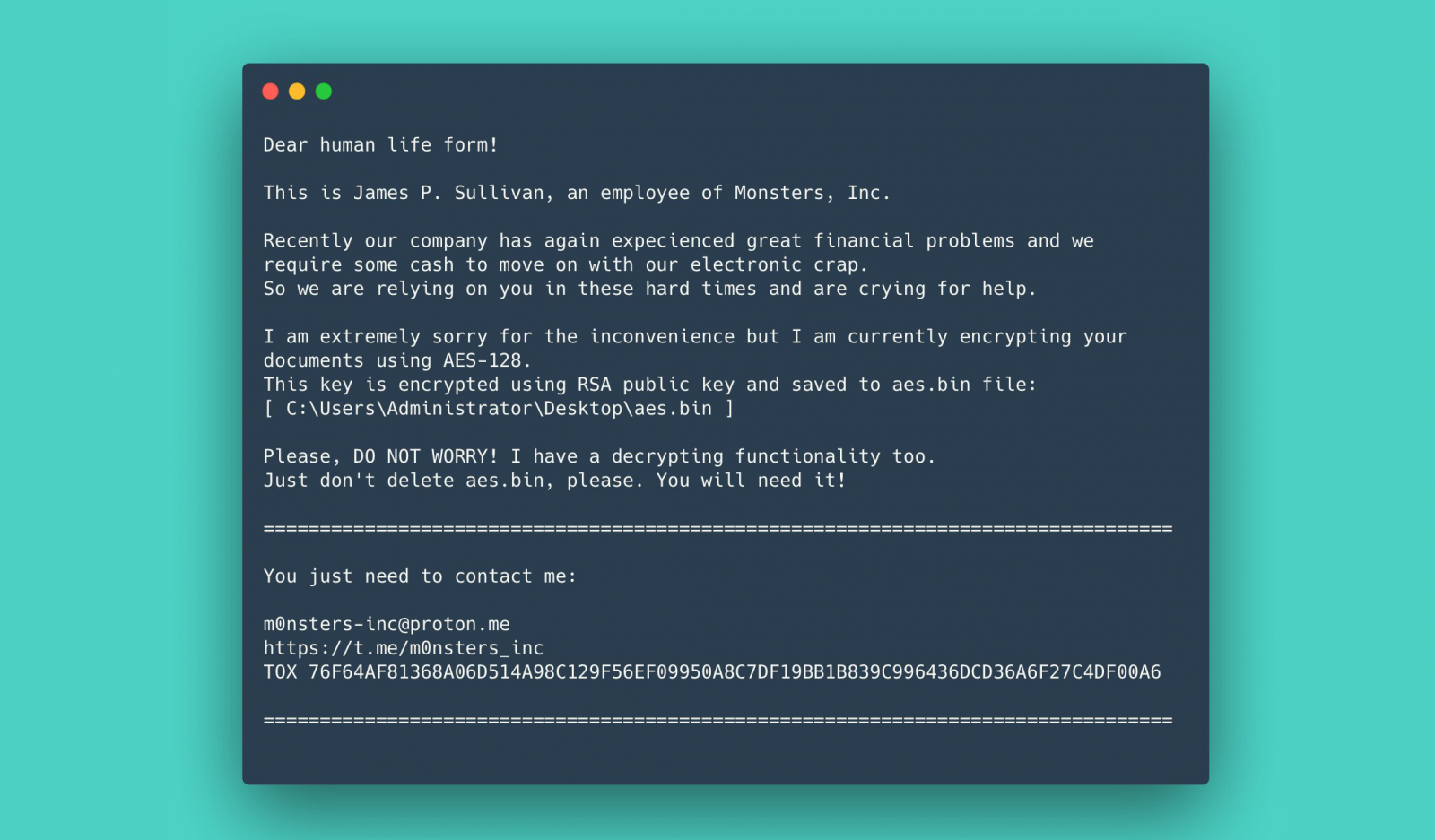
Once pushed onto a victim’s network, RansomBoggs encrypts files using AES-256 in CBC mode using a random key (randomly generated, RSA encrypted and written to aes.bin), and it adds a .chsch extension to all encrypted file extensions.
Depending on the variant used in the attack, the RSA public key may be hard-coded into the malware itself or provided as an argument.
On encrypted systems, the ransomware also drops ransom notes impersonating James P. Sullivan, the main character from the movie Monsters Inc, with other references also found in the malware code.
Earlier this month, Microsoft also linked cyber espionage group Sandworm (tracked by Redmond as IRIDIUM) to Prestige ransomware attacks targeting transportation and logistics companies in Ukraine and Poland since October.
“The Prestige campaign may highlight a measured change in the calculation of destructive IRIDIUM attacks, signaling an increased risk for organizations directly providing or transporting humanitarian or military assistance to Ukraine,” MSTIC said. said.
“More broadly, this may pose an increased risk to organizations in Eastern Europe that may be seen by the Russian state as providing war-related support.”
In February, a joint security advisory issued by the US and UK cybersecurity agencies also pinpointed the Cyclops Blink botnet. on the Russian military threat group before his disturbancepreventing its use in the wild.
sandworm is a group of elite Russian hackers active for at least two decades who are part of unit 74455 of the Main Center for Special Technologies (GTsST) of the Russian GRU.
They have previously been linked to attacks leading to the KillDisk wiper attacks targeting banks in Ukraine and the Ukrainian blackouts of 2015 and 2016 [1, 2, 3].
Sandworm is also believed to have developed NotPetya ransomware which caused billions in damage as of June 2017.
The US Department of Justice accused six of the group’s agents in October 2020 with the coordination of hacking operations related to the NotPetya ransomware attack, the PyeongChang 2018 Winter Olympics, as well as the 2017 French elections.
[ad_2]
Source link
