[ad_1]

Security researchers have discovered a new strain of ransomware they have named Mimic that leverages the APIs of the “Everything” file search tool for Windows to search for files targeted for encryption.
Discovered in June 2022 by researchers from a cybersecurity company Trend Microthe malware seems to mainly target English and Russian speaking users.
Part of Mimic’s code shares similarities with Conti ransomware, the source of which was leaked March 2022 by a Ukrainian researcher.
Mimic attacks
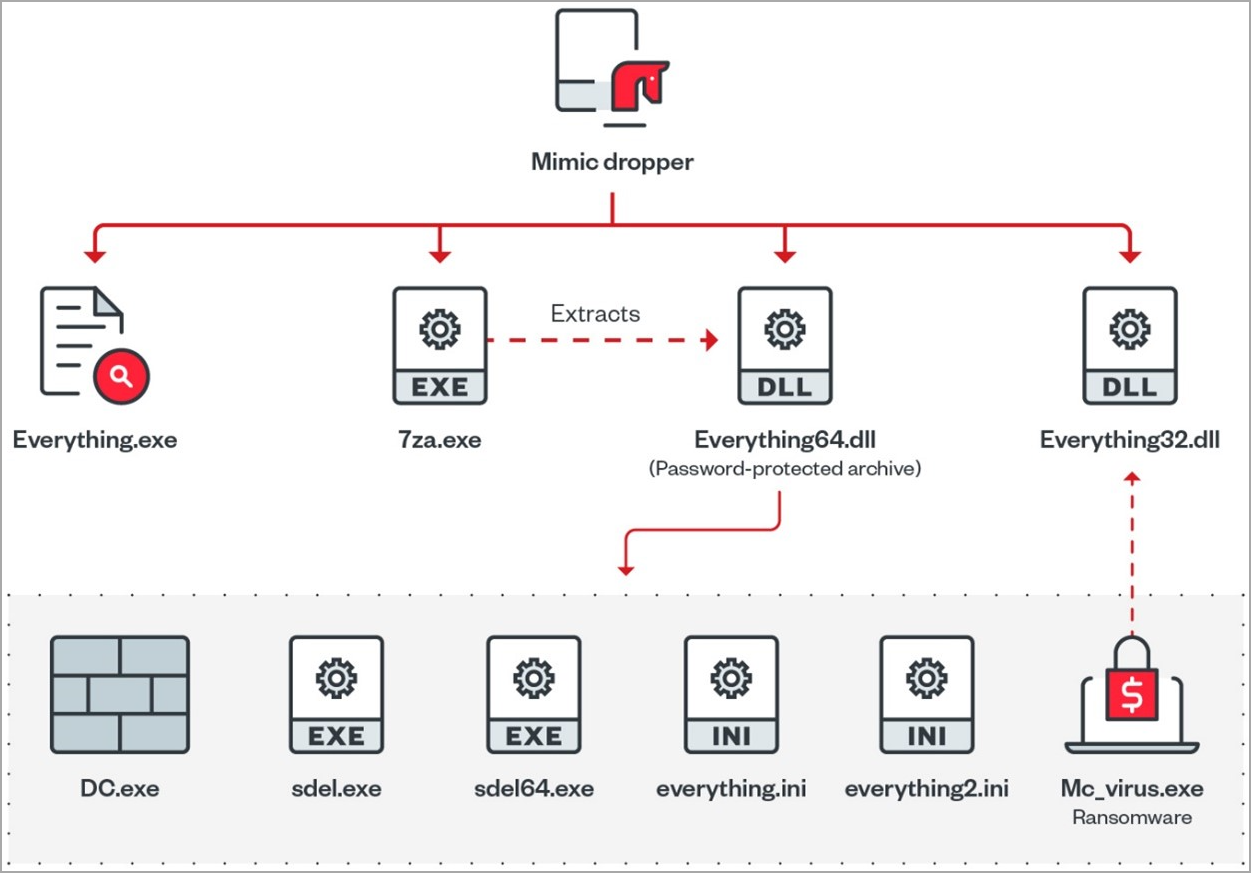
Mimic ransomware attacks begin with the victim receiving an executable, presumably via email, which extracts four files onto the target system, including the main payload, auxiliary files, and tools to disable Windows Defender.
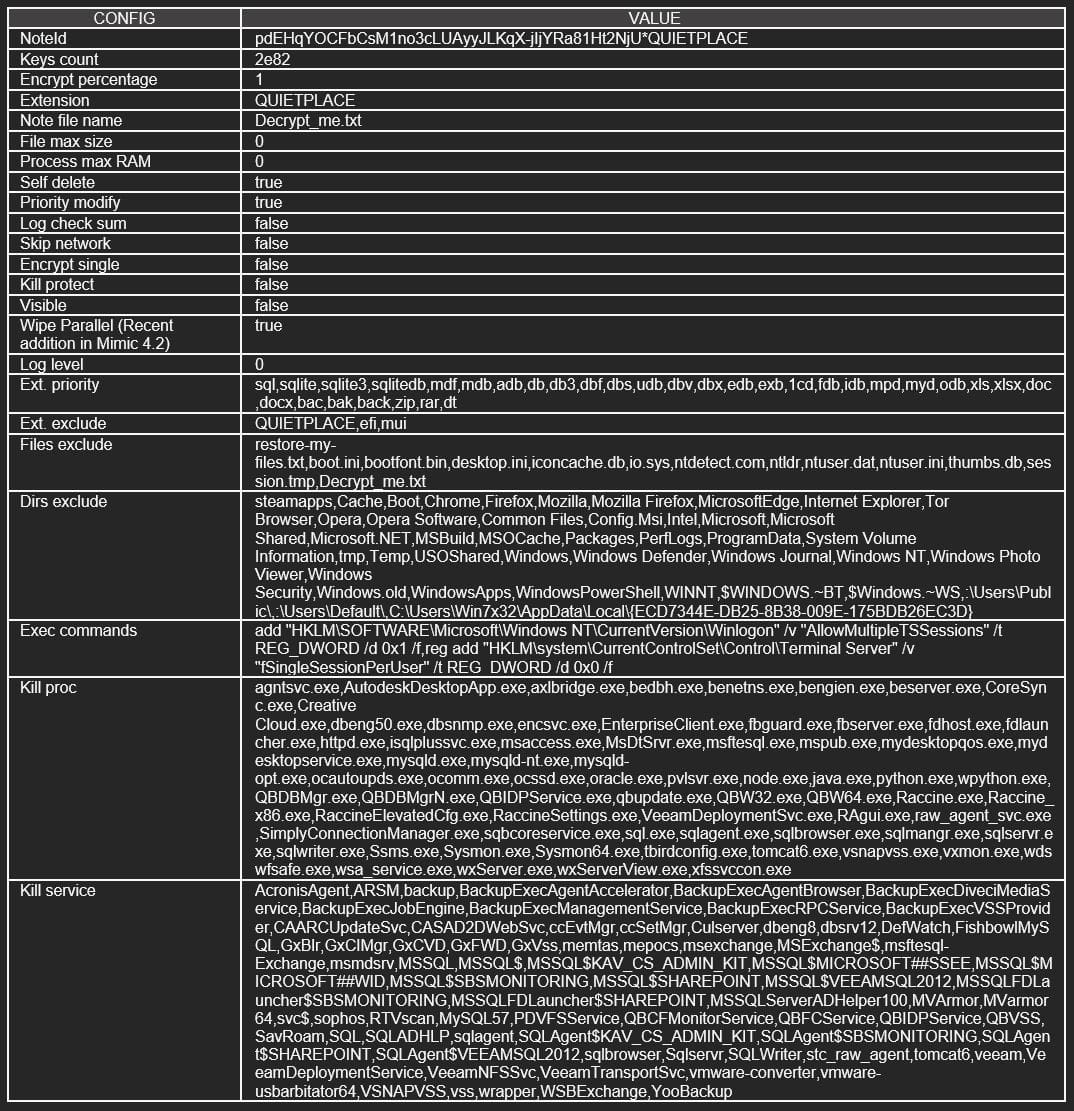
Mimic is a versatile ransomware strain that supports command line arguments to fine-tune file targeting, while also being able to use multiple CPU threads to speed up the data encryption process.
The new ransomware family has several features found in modern strains, such as:
- System information collection
- Creation of persistence via the RUN key
- Bypassing User Account Control (UAC)
- Disabling Windows Defender
- Disabling Windows Telemetry
- Enable anti-shutdown measures
- Activate anti-kill measures
- Unmount virtual drives
- Terminate processes and services
- Disabling sleep mode and shutting down the system
- Deleting flags
- Inhibit System Recovery
Killing processes and services aim to disable protective measures and release important data such as database files, making them available for encryption.
abuse everything
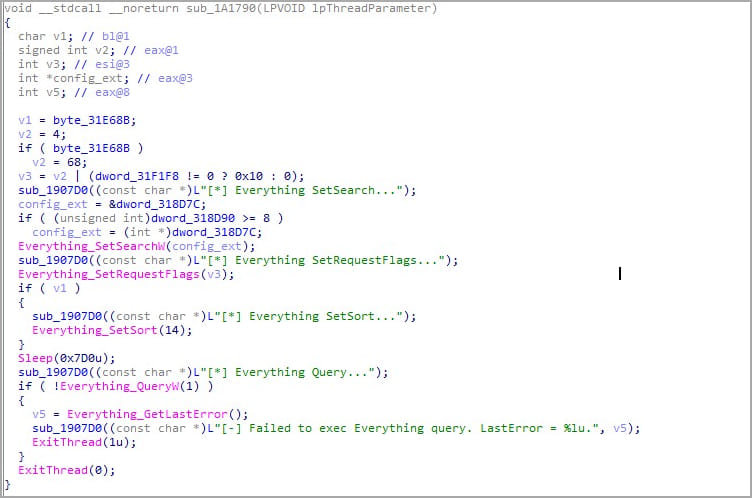
“Everything” is the name of a popular filename search engine for Windows developed by empty tools. The utility is lightweight and fast, uses minimal system resources and supports real-time updates.
Mimic ransomware uses Everything’s search capabilities in the form of “Everything32.dll” dropped during the infection phase to search for specific filenames and extensions in the compromised system.
Everything helps Mimic locate valid files for encryption while avoiding system files that would render the system unbootable if locked.
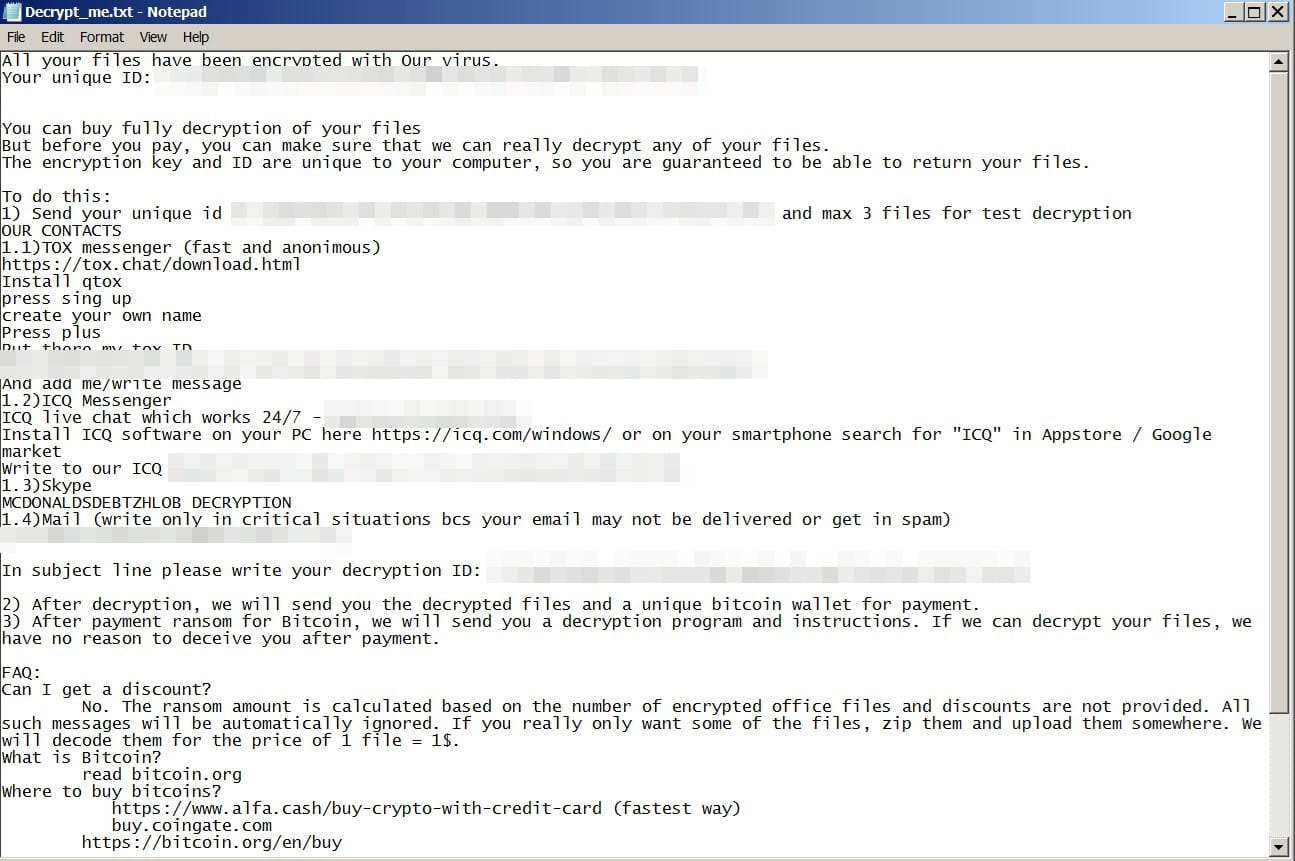
Files encrypted by Mimic are given the extension “.QUIETPLACE”. A ransom note is also dropped, informing about the attacker’s demands and how the data can be recovered after paying a ransom in Bitcoin.
Mimic is a new strain with as yet unproven activity, but the use of Conti builder and Everything API proves that its authors are proficient software developers who have a clear understanding of how they can achieve their goals.
[ad_2]
Source link
