[ad_1]

A new Android malware called “FluHorse” has been discovered, targeting East Asian users with malicious apps that mimic legitimate versions.
The malware was discovered by Check Point Research, which reports that it has been targeting various sectors in East Asia since May 2022.
The FluHorse malware is distributed via email, while its objective is to steal account credentials and credit card data of its target and, if necessary, to snatch two-factor authentication codes (2FA).
Top targets
FluHorse attacks begin with malicious emails sent to high-profile targets, urging them to take immediate action to resolve a payment issue.
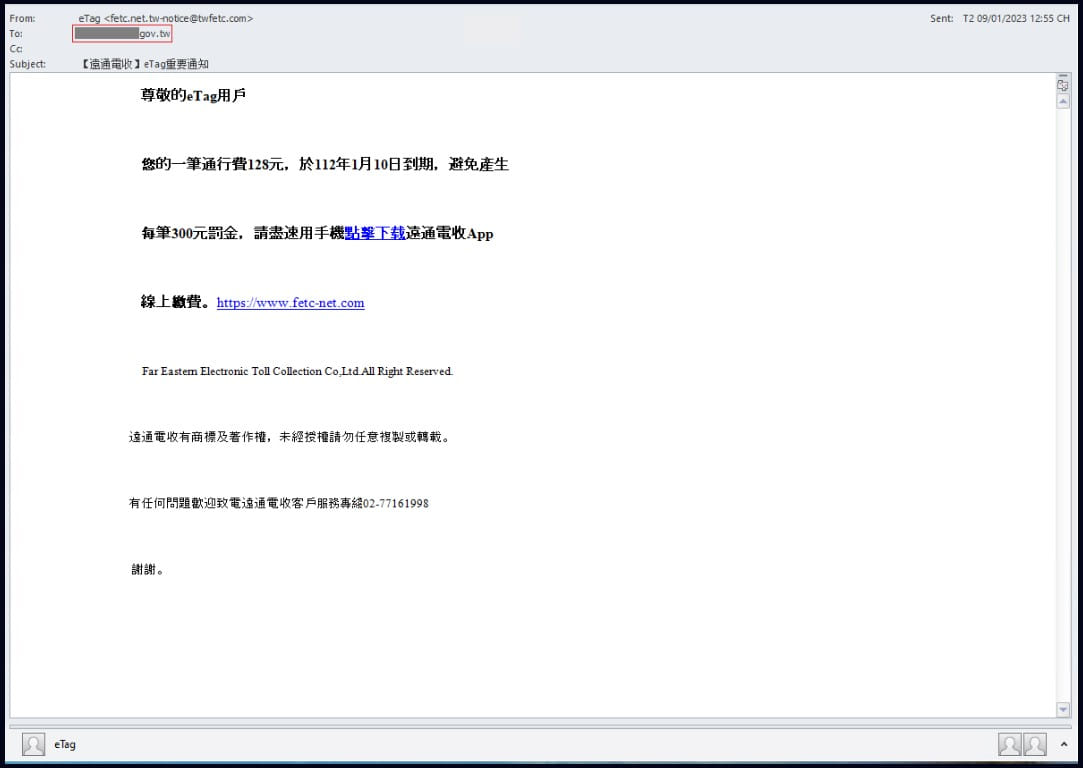
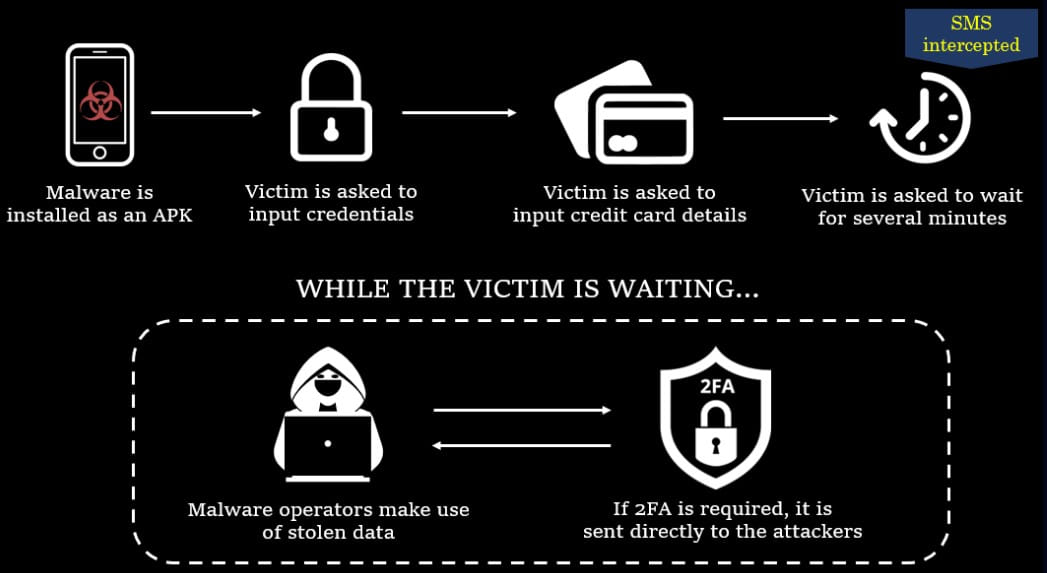
Typically, the victim is directed to a phishing site via a link provided in the email, from where they download the fake APK (Android package file) application.
The apps imitated by FluHorse carrier apps are “ETC”, a toll app used in Taiwan, and “VPBank Neo”, a banking app in Vietnam. The two legitimate versions of these apps each have over a million downloads on Google Play.

Check Point also observed the malware posing as a transportation app used by 100,000 people, but its name was not disclosed in the report.
All three fake apps request SMS access upon installation to intercept incoming 2FA codes in case there is a need to hijack accounts.

(checkpoint)
Analysts comment that the fake apps copy the GUI of the originals but don’t have many features other than two or three windows that load forms that capture victim information.

After capturing victims’ account credentials and credit card details, the apps display a “system is busy” message for 10 minutes, likely to make the process realistic while operators act back- plan to intercept 2FA codes and exploit stolen data.
CheckPoint says the malicious apps were built in Dart, using the Flutter platform, and reverse engineering and decompiling the malware was difficult.
“The Flutter runtime for ARM uses its own stack pointer register (R15) instead of the built-in stack pointer (SP),” it reads. Check Point Report.
“Which register is used as the stack pointer makes no difference in the execution of the code or in the process of reverse engineering. However, it makes a big difference to the decompiler. Due to non-standard use of registers, a fake and ugly pseudocode is generated.”
The analysis was so difficult that CheckPoint ended up making improvements to existing open source tools such as “flutter-re-demo” and “reFlutter”.
Ultimately, this work revealed the functions responsible for exfiltrating the victims’ credentials, credit card data, and the HTTP POST communication that sent the intercepted SMS messages to the C2 server.
CheckPoint warns that the FluHorse campaign is ongoing, with new infrastructure and malicious apps appearing every month, so this is an active threat to Android users.
[ad_2]
Source link
