[ad_1]

A new Android subscription malware named “Fleckpe” has been spotted on Google Play, the official Android app store, disguised as legitimate apps that have been downloaded over 620,000 times.
Kaspersky reveals that Fleckpe is the newest addition to the malware field that generates unauthorized charges by subscribing users to premium services, joining the ranks of other malicious Android malware, such as joker And Harry.
Threat actors make money from unauthorized subscriptions by receiving a share of monthly or one-time subscription fees generated by premium services. When threat actors exploit the services, they retain all revenue.
Kaspersky data suggests that the Trojan has been active for the past year but was only recently discovered and documented.
Most Fleckpe victims reside in Thailand, Malaysia, Indonesia, Singapore, and Poland, but smaller numbers of infections are found across the world.
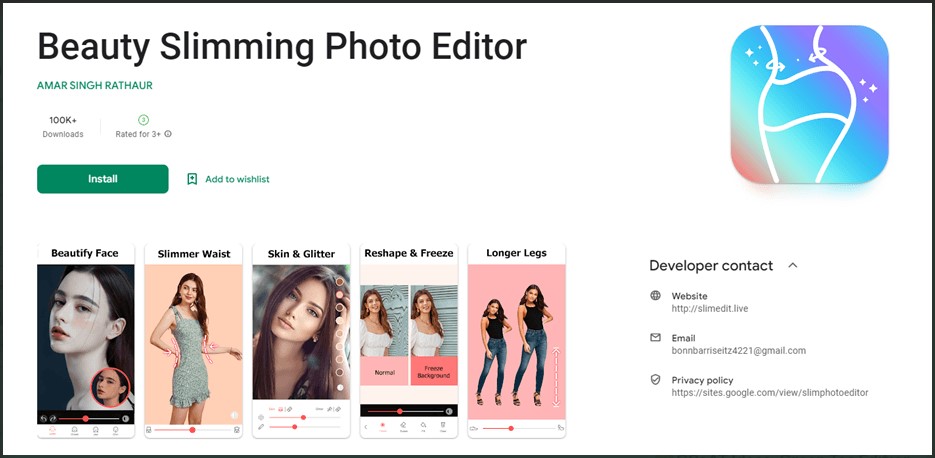
Kaspersky discovered 11 Fleckpe trojan apps posing as image editors, photo libraries, premium wallpapers and more on Google Play, distributed under the following names:
- com.impressionism.prozs.app
- com.picture.pictureframe
- com.beauty.minceur.pro
- com.beauty.camera.plus.photoeditor
- com.microclip.vodeoeditor
- com.gif.camera.editor
- com.apps.camera.photos
- com.toolbox.photoeditor
- com.hd.h4ks.wallpaper
- com.draw.graffiti
- com.urox.opixe.nightcamreapro
“All apps had been removed from the market at the time of our report, but malicious actors may have deployed other apps not yet discovered, so the actual number of installs may be higher.” explains Kaspersky in his report.
Android users who have already installed the apps listed above are advised to remove them immediately and run an AV scan to root out any remnants of malicious code still hidden in the device.
Subscribe in the background
Upon installation, the malicious app requests access to notification content required to capture subscription confirmation codes on many premium services.
When a Fleckpe app launches, it decodes a hidden payload containing malicious code, which is then executed.
This payload is responsible for contacting the threat actor’s command and control (C2) server to send basic information about the newly infected device, including the MCC (Mobile Country Code) and MNC ( Mobile Network Code).
The C2 responds with a website address which the Trojan opens in an invisible web browser window and subscribes the victim to a premium service.
If a confirmation code needs to be entered, the malware will retrieve it from device notifications and submit it on the hidden screen to complete the subscription.
The app’s foreground still provides victims with the promised functionality, hiding their true purpose and reducing the likelihood of arousing suspicion.
In the latest versions of Fleckpe analyzed by Kaspersky, the developers have moved most of the payload’s subscription code to the native library, leaving the payload responsible for intercepting notifications and displaying web pages. .
.jpg)
Additionally, an obfuscation layer has been incorporated into the most recent version of the payload.
Kaspersky believes that the malware’s creators implemented these changes to increase Fleckpe’s evasiveness and make it harder to scan.
Although not as dangerous as spyware or data-stealing malware, subscription Trojans can still incur unauthorized charges, collect sensitive user information from the infected device, and potentially serve as entry points for more powerful payloads.
To protect against these threats, Android users are advised to only download apps from trusted sources and developers and pay attention to the permissions requested during installation.
[ad_2]
Source link
