[ad_1]

Mandiant has released a scanner to check if a Citrix NetScaler Application Delivery Controller (ADC) or NetScaler Gateway Appliance was compromised in widespread attacks exploiting the CVE-2023-3519 vulnerability.
The critical CVE-2023-3519 Citrix flaw was discovered in mid-July 2023 as a zero-day, with hackers actively exploiting it to execute code remotely without authentication on vulnerable devices.
A week after Citrix made security updates to address the problem available, Shadowserver reported that there were still 15,000 internet-exposed appliances that hadn’t applied the patches.
However, even for organizations that installed the security updates, the risk of being compromised remains, as the patch does not remove malware, backdoors, and webshells planted by the attackers in the post-compromise phase.
Scanner checks for hacked devices
Today, Mandiant released a scanner that enables organizations to examine their Citrix ADC and Citrix Gateway devices for signs of compromise and post-exploitation activity.
“The tool is designed to do a best effort job at identifying existing compromises,” reads Mandiant’s post.
“It will not identify a compromise 100% of the time, and it will not tell you if a device is vulnerable to exploitation.”
Mandian’t Ctrix IOC Scanner must be run directly on a device or a mounted forensic image, as it will scan the local filesystem and configuration files for the presence of various IOCs.
When finished, the scanner will display a summary detailing if it encountered any signs of compromise, as shown below.
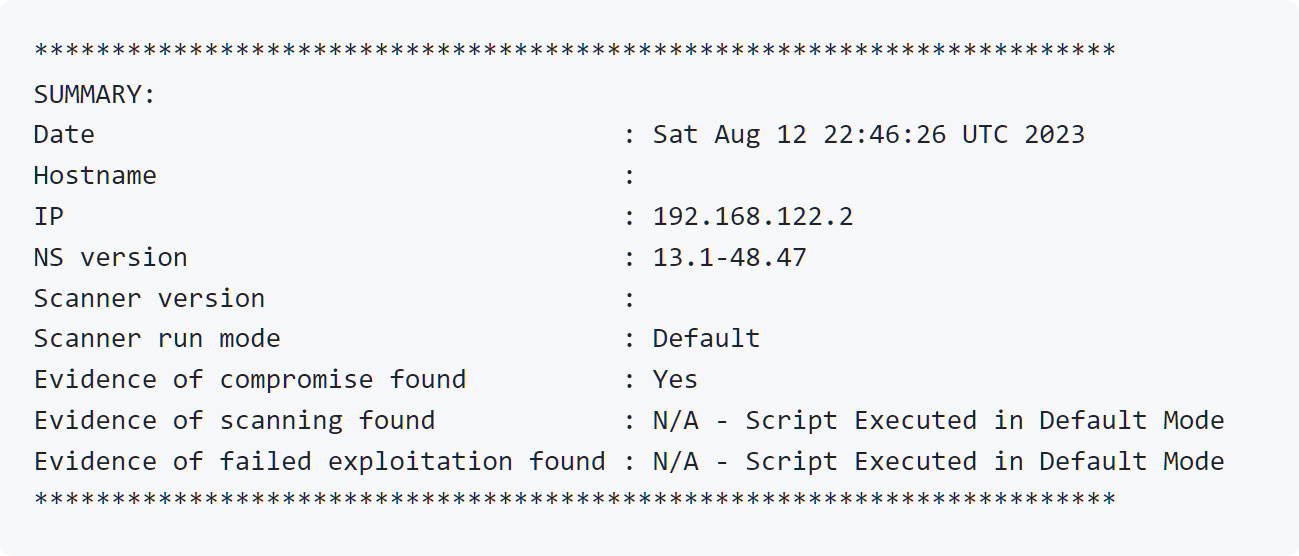
Source: Mandiant
If it detects that the device was compromised, the scanner will display a detailed report listing the various indicators of compromise that were detected.
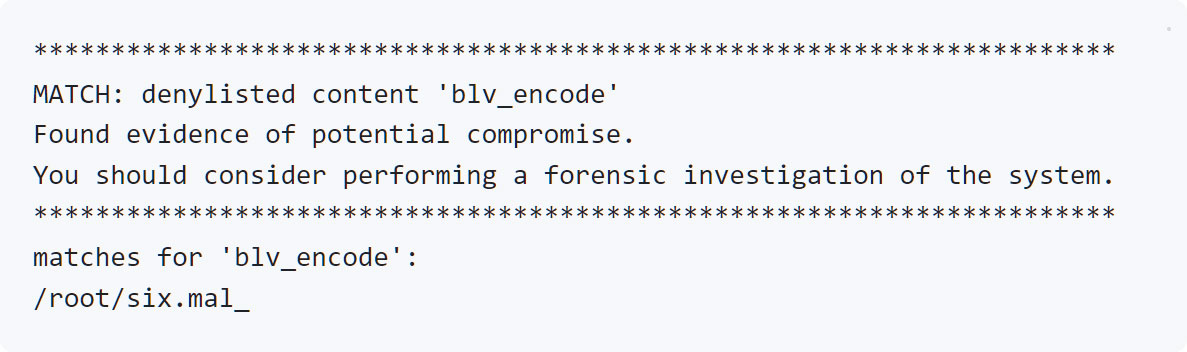
Source: Mandiant
Some of the indicators of compromise that the scanner looks for on Citrix devices are listed below:
- File system paths containing that may contain suspicious files:
- /var/netscaler/logon/LogonPoint/uiareas
- /var/netscaler/logon/LogonPoint/uiareas/*/
- /netscaler/ns_gui/epa/scripts/*/
- /netscaler/ns_gui/vpns/theme/default
- /var/vpn/themes/
- Known attacker or suspicious commands in the shell history:
- whoami$
- cat /flash/nsconfig/keys
- ldapsearch
- chmod +x /tmp
- openssl des3
- ping -c 1
- cp /bin/sh
- chmod +s /var
- echo <?php
- Files in NetScaler directories with contents matching known IOCs:
- /var/vpn/theme/.theme.php
- /var/tmp/the
- /var/tmp/npc
- /var/tmp/conf/npc.conf
- /var/tmp/conf/multi_account.conf
- Files with suspicious permissions or ownership, such as unusual setuid binaries.
- Crontab files for the ‘nobody’ user.
- Historical cron jobs running as ‘nobody’.
- Suspicious running processes running as ‘nobody’ or running from ‘/var/tmp’.
More details on using the scanner tool and interpreting the results can be found on Mandiant’s GitHub repository for the project.
If the scanner reveals signs of compromise, it is recommended to perform a complete forensic examination on the impacted appliances and network parts to evaluate the scope and extent of the breach, which requires a different set of tools.
It is important to note that a negative result should not be taken as a guarantee that a system hasn’t been compromised, as attackers still have many ways to hide their traces and, in many cases, had ample time to do so.
“Log files on the system with evidence of compromise may have been truncated or rolled, the system may have been rebooted, an attacker may have tampered with the system to remove evidence of compromise and/or installed a rootkit that masks evidence of compromise.” – Mandiant
It is recommended to run the scanner on all appliances exposed to the internet while running a vulnerable firmware version at any time.
The scanner was designed to be used with Citrix ADC and Citrix Gateway versions 12.0, 12.1, 13.0, and 13.1.
[ad_2]
Source link
