[ad_1]
A new ransomware operation called Cactus exploits vulnerabilities in VPN appliances for initial access to the networks of “large commercial entities”.
The Cactus ransomware operation has been active since at least March and seeks large payouts from its victims.
While the new threat actor adopted the usual tactics seen in ransomware attacks – file encryption and data theft – it added its own twist to evade detection.
Encrypted configuration twist
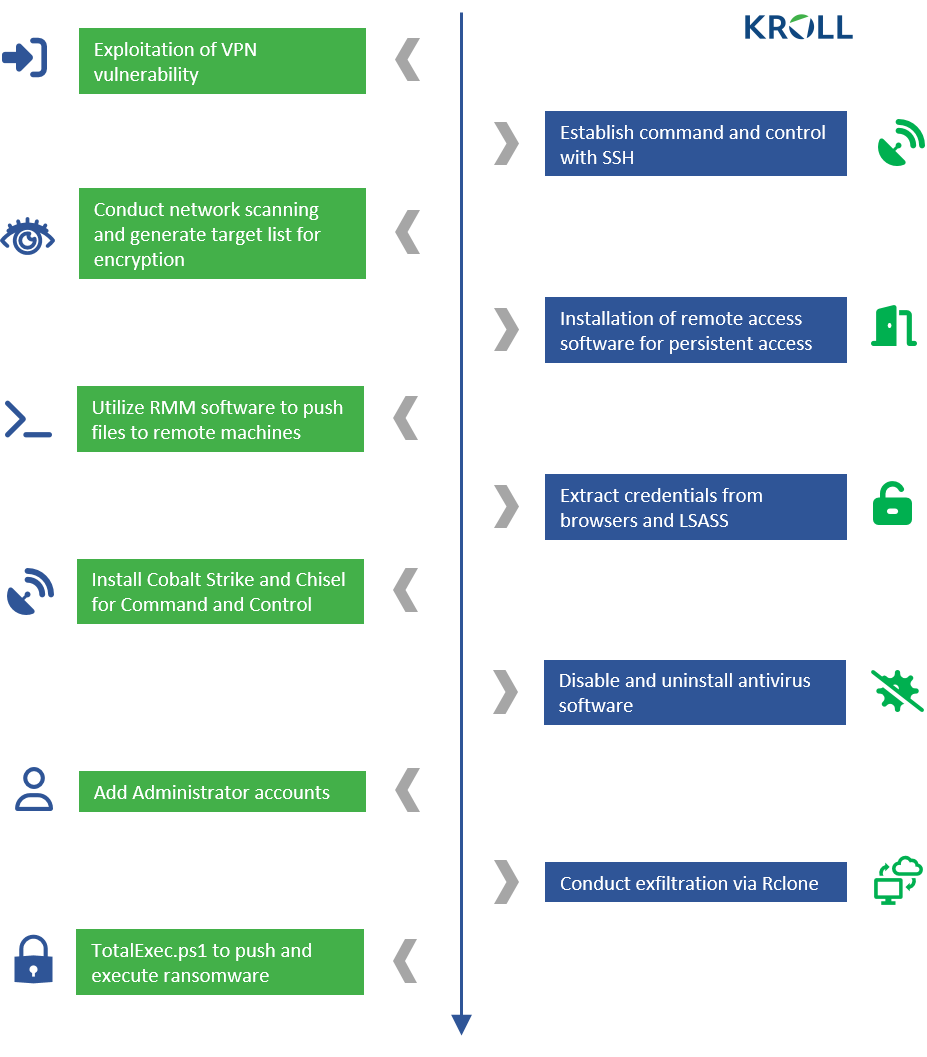
Researchers from risk management and investigation consulting firm Kroll believe that Cactus gains initial access to the victim’s network by exploiting known vulnerabilities in Fortinet VPN appliances.
The assessment is based on the observation that in all of the incidents studied, the attacker pivoted inside a VPN server with a VPN service account.
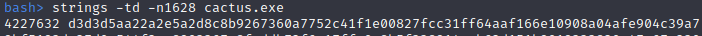
What sets Cactus apart from other operations is the use of encryption to protect the ransomware binary. The actor uses a batch script to get the encryptor binary using 7-Zip.
The original ZIP archive is deleted and the binary is deployed with a specific flag that allows it to run. The whole process is unusual and the researchers believe it is to prevent detection of the ransomware encryptor.
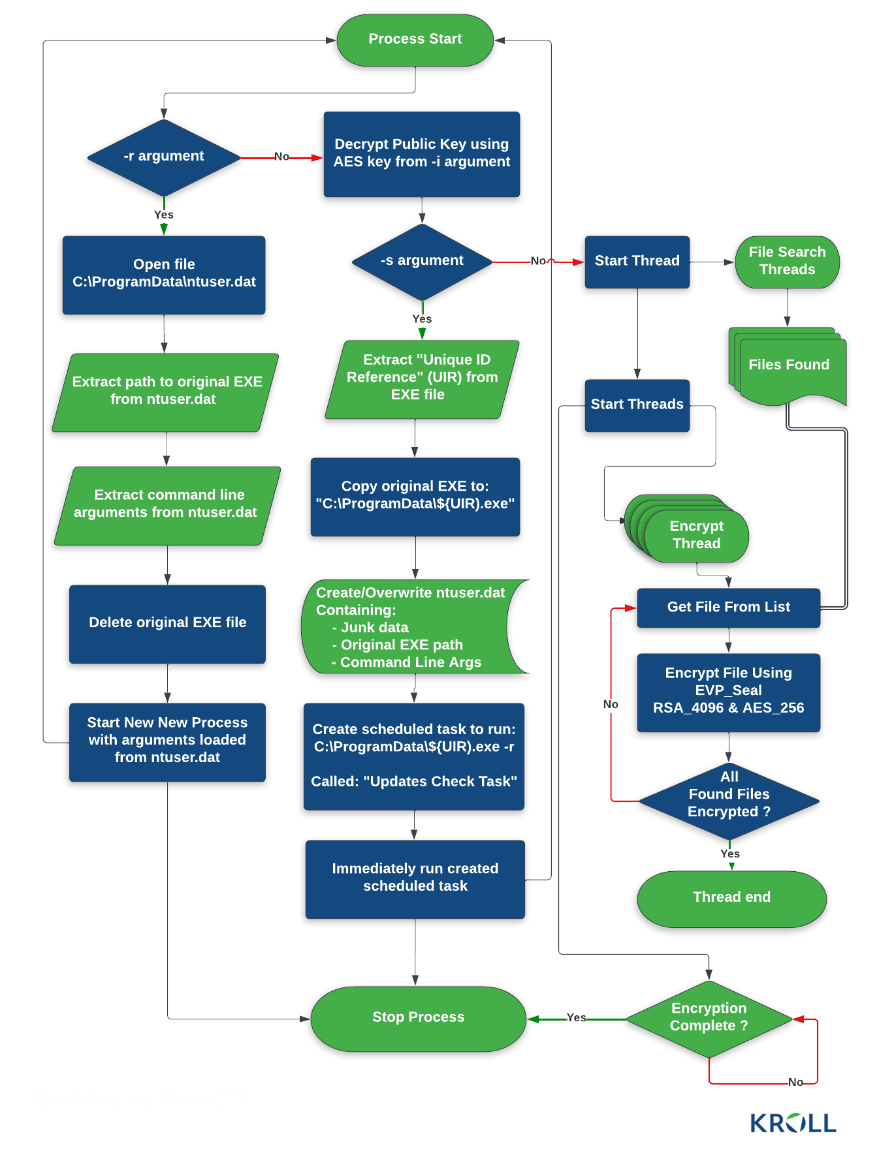
In a technical report, Kroll investigators explain that there are three main execution modes, each selected using a specific command-line switch: setup (-s), read config (-r) and encryption (-I).
THE -s And -r allow threat actors to configure persistence and store data in a C:\ProgramData\ntuser.dat file which is then read by the encryptor when running with the -r command line argument.
However, for file encryption to be possible, a unique AES key known only to attackers must be provided using the -I command line argument.
This key is needed to decrypt the ransomware configuration file and the RSA public key needed to encrypt the files. It is available as a hard-coded HEX string in the encryptor binary.
source: Kroll
Decoding the HEX string provides encrypted data that unlocks with the AES key.
“CACTUS essentially encrypts itself, which makes it harder to detect and helps it evade antivirus and network monitoring tools,” Laurie Iacono, associate general manager for Cyber Risk at Kroll, told Bleeping Computer. .
Run the binary with the correct key for the -I (encryption) unlocks information and allows malware to search for files and start a multi-threaded encryption process.
Kroll researchers have provided the diagram below to better explain Cactus’s binary execution process depending on the selected setting.
source: Kroll
Ransomware Expert Michael Gillespie also analyzed how Cactus encrypts data and told BleepingComputer that the malware uses multiple extensions for the files it targets, depending on the processing state.
When preparing a file for encryption, Cactus changes its extension to .CTS0. After encryption, the extension becomes .CTS1.
However, Gillespie explained that Cactus can also have a “fast mode”, which is akin to a light encryption pass. Consecutive execution of the malware in fast and normal mode causes the same file to be encrypted twice and a new extension to be added after each process (for example, .CTS1.CTS7).
Kroll observed that the number at the end of the .CTS extension varied in several incidents attributed to Cactus ransomware.
Cactus ransomware TTP
Once in the network, the threat actor used a scheduled task for persistent access using an SSH backdoor accessible from the command and control (C2) server.
According to Kroll investigators, Cactus relied on SoftPerfect Network Scanner (netscan) to search for interesting targets on the network.
For further reconnaissance, the attacker used PowerShell commands to enumerate endpoints, identify user accounts by displaying successful logins in Windows Event Viewer, and ping remote hosts.
Researchers also discovered that Cactus ransomware uses a modified variant of open-source psnmap Tool, which is a PowerShell equivalent of Tool nmap network analyzer.
To launch various tools needed for the attack, investigators claim that Cactus ransomware tries several remote access methods via legitimate tools (e.g. Splashtop, AnyDesk, SuperOps RMM) as well as Cobalt Strike and proxy tool based on Go. Chisel.
Kroll investigators claim that after escalating privileges on a machine, Cactus operators run a batch script that uninstalls the most commonly used anti-virus products.
Like most ransomware operations, Cactus also steals data from the victim. For this process, threat actor uses Rclone tool to transfer files directly to cloud storage.
After exfiltrating the data, the hackers used a PowerShell script called TotalExec, often seen in BlackBasta ransomware attacks, to automate the deployment of the encryption process.
Gillespie told us that the encryption routine in Cactus ransomware attacks is unique. Despite this, this does not appear to be specific to Cactus as a similar encryption process has also been recently adopted by the BlackBasta ransomware gang.
source: Kroll
At this time, there is no public information on the ransoms Cactus demands from its victims, but BleepingComputer has been told by a source that they number in the millions.
Even though the hackers are stealing victims’ data, it seems that they haven’t set up a leak site like the other ransomware operations involved in the double extortion.
However, the threat actor threatens the victims to publish the stolen files unless they are paid. This is explicit in the ransom note:
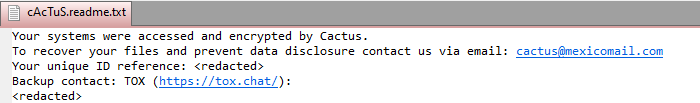
source: Kroll
Extensive details about Operation Cactus, the victims they target, and whether the hackers keep their word and provide a reliable decryptor if paid, are not available at this time.
What is clear is that hacker incursions so far have likely exploited vulnerabilities in the Fortinet VPN appliance and are following the standard double extortion approach of stealing data before encrypting it.
Applying the latest vendor software updates, monitoring the network for large data exfiltration tasks, and responding quickly should protect against the final and most damaging stages of a ransomware attack.
[ad_2]
Source link
