[ad_1]

More than 4,000 Sophos Firewall devices exposed to internet access are vulnerable to attacks targeting a critical remote code execution (RCE) vulnerability.
Sophos disclosed this code injection flaw (CVE-2022-3236) found in the Sophos Firewall User and Webadmin Portal in September and also released patches for several versions of Sophos Firewall (official patches were released three months later, in December 2022).
The company warned at the time that the RCE bug was exploited in the wild in attacks on organizations in South Asia.
The September patches have been deployed to all affected instances (v19.0 MR1/19.0.1 and earlier) since automatic updates are enabled by default unless an administrator has disabled the option.
Instances of Sophos Firewall running older product versions had to be manually upgraded to a supported version to automatically receive the CVE-2022-3236 patch.
Administrators who cannot patch the vulnerable software can also remove the attack surface by deactivation WAN access to user portal and Webadmin.
Thousands of devices are still vulnerable
While scanning the internet for Sophos Firewall devices, VulnCheck vulnerability researcher Jacob Baines discovered that out of over 88,000 instances, around 6% or over 4,000 are running versions that do not have not received a patch and are vulnerable to CVE-2022-3236 attacks. .
“Over 99% of internet-facing Sophos firewalls have not been upgraded to versions containing the official fix for CVE-2022-3236.” Baines said.
“But about 93% are running patch-eligible builds, and the firewall’s default behavior is to automatically download and apply patches (unless disabled by an administrator).
“That still leaves over 4,000 firewalls (or around 6% of internet-facing Sophos firewalls) running versions that haven’t been patched and are therefore vulnerable.”
Luckily, despite being exploited as zero-day already, a proof-of-concept exploit CVE-2022-3236 has not yet been released online.
However, Baines was able to replicate the exploit based on technical information shared by Trend Micro’s Zero Day Initiative (ZDI), so it’s likely that threat actors will soon be able to do so as well.
When and if this happens, it will most likely lead to a new wave of attacks as soon as threat actors create a fully functional version of the exploit and add it to their toolset.
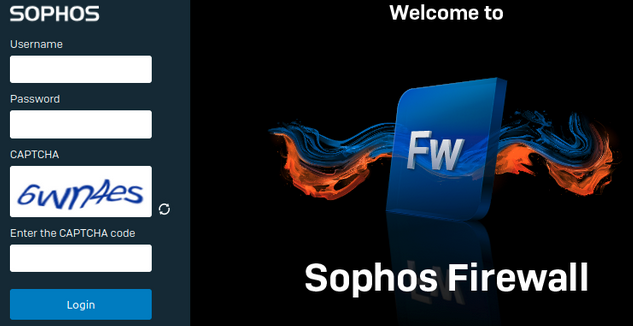
Baines also added that mass mining would likely be hampered by the Sophos firewall requiring default web clients to “solve a captcha upon authentication”.
To circumvent this limitation and reach the vulnerable code, attackers should include an automated CAPTCHA solver.
Sophos Firewall bugs previously targeted by attacks
Fixing Sophos Firewall bugs is critically important, given that this wouldn’t be the first time such a vulnerability has been exploited in the wild.
In March 2022, Sophos fixed a similar Sophos Firewall critical bug (CVE-2022-1040) in the User Portal and Webadmin modules that allowed authentication bypass and arbitrary code execution attacks.
It was also exploited in attacks as day zero since early March (about three weeks before Sophos released patches) against South Asian organizations by a Chinese threat group tracked as DriftingCloud.
A zero-day SQL injection in XG Firewall was also abused by threat actors from early 2020 to steal sensitive data such as usernames and passwords using the Asnarök Trojan Malware.
On the same day zero was operated for deliver Ragnarok ransomware payloads on Windows corporate networks.
[ad_2]
Source link
