[ad_1]
A new Mirai malware botnet variant has been spotted infecting inexpensive Android TV set-top boxes used by millions for media streaming.
According to Dr. Web’s antivirus team, the current trojan is a new version of the ‘Pandora’ backdoor that first appeared in 2015.
The primary targets of this campaign are low-cost Android TV boxes like Tanix TX6 TV Box, MX10 Pro 6K, and H96 MAX X3, which feature quad-core processors capable of launching powerful DDoS attacks even in small swarm sizes.
Malware in the box
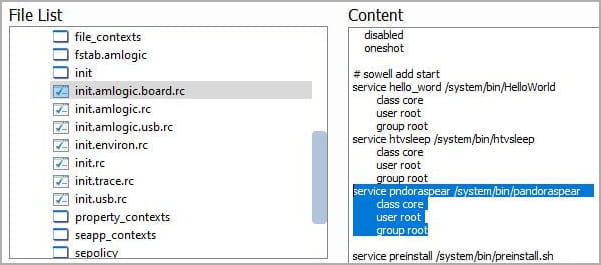
Dr. Web reports that the malware arrives on the devices either via a malicious firmware update signed with publicly available test keys or distributed via malicious apps on domains targeting users interested in pirated content.
In the first case, those firmware updates are either installed by resellers of the devices or the users are tricked into downloading them from websites that promise unrestricted media streaming or better compatibility with a broader range of applications.
The malicious service is in ‘boot.img,’ which contains the kernel and ramdisk components loaded during the Android system boot-up, so it’s an excellent persistence mechanism.
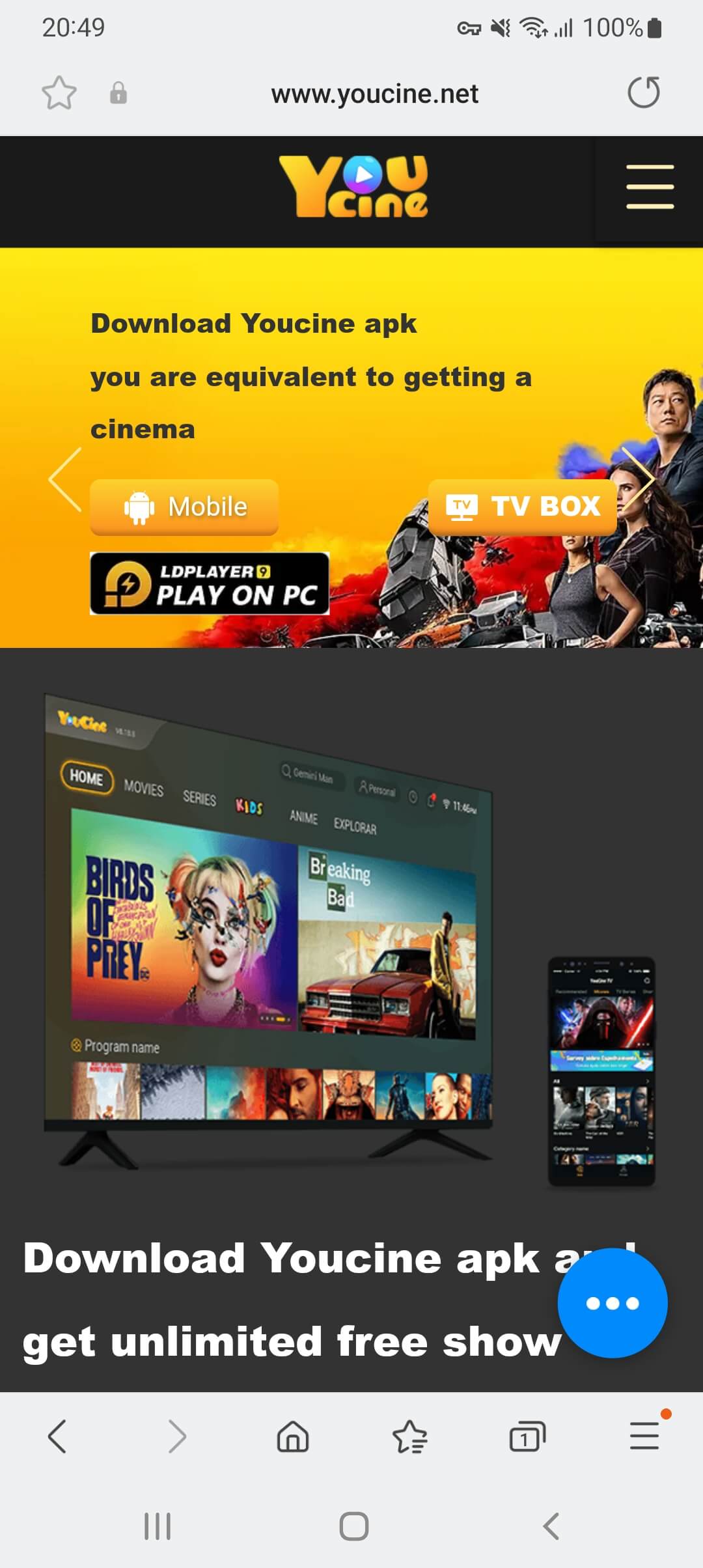
The second distribution channel is pirated content apps that promise access to collections of copyright-protected TV shows and movies for free or at a low fee.
Dr. Web gives examples of Android apps that infected devices with this new Mirai malware variant.
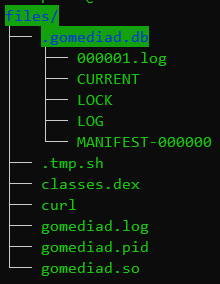
In this case, persistence is achieved during the first launch of the malicious apps, which start the ‘GoMediaService’ in the background without the user’s knowledge and set it to auto-start on device boot.
That service calls the ‘gomediad.so’ program, which unpacks multiple files, including a command-line interpreter that runs with elevated privileges (‘Tool.AppProcessShell.1’) and an installer for the Pandora backdoor (‘.tmp.sh’).
(Dr. Web)
Once active, the backdoor communicates with the C2 server, replaces the HOSTS file, updates itself, and then enters standby mode, waiting for incoming commands from its operators.
Dr. Web reports the malware can perform DDoS attacks over the TCP and UDP protocols, like generating SYN, ICMP, and DNS flood requests, as well as opening a reverse shell, mounting system partitions for modification, and more.
Inherently risky devices
Budget-friendly Android TV boxes often have a murky journey from manufacturer to consumer, leaving the end-user in the dark about their origins, potential firmware alterations, and the various hands they’ve passed through.
Even for cautious consumers who retain the original ROM and are selective about app installations, there’s a lingering risk of the devices arriving with preloaded malware.
That said, it would be advisable to opt for streaming devices from trusted brands such as Google Chromecast, Apple TV, NVIDIA Shield, Amazon Fire TV, and Roku Stick.
[ad_2]
Source link
