[ad_1]

Security researchers have found an easy way to deliver malware to an organization with Microsoft Teams, despite in-app restrictions for files from external sources.
With 280 million monthly active usersMicrosoft Teams has been embraced by organizations as a communication and collaboration platform that is part of Microsoft 365 cloud-based services.
Given the popularity of the product with various organizations, Max Corbridge And Tom Elson – Red team members from UK security services company Jumpsec investigated and found a way to spread malware using Microsoft Teams with an account outside the target organization.
Attack Details
The attack works with Microsoft Teams running the default configuration, which allows communication with Microsoft Teams accounts outside the company, commonly referred to as “external tenants”.
Corbridge explains in a report that while this communication bridge would be sufficient for social engineering and phishing attacks, the method they found is more powerful because it allows a malicious payload to be sent directly to a mailbox. target reception.
Microsoft Teams has client-side protections in place to block file delivery from external tenant accounts.
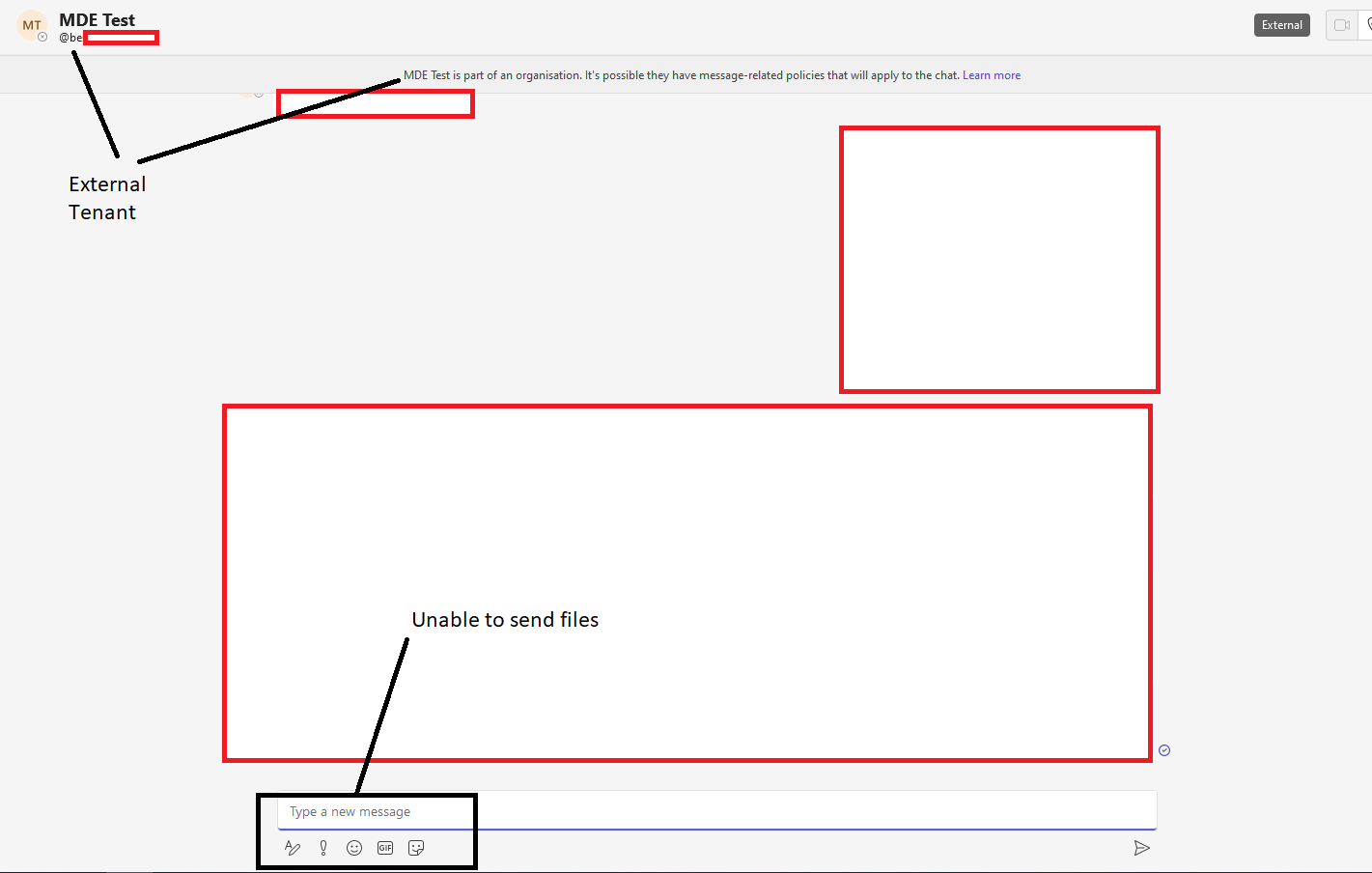
However, the two Jumpsec Red Team members discovered that they could circumvent the restriction by changing the internal and external recipient ID in a message’s POST request, thereby tricking the system into treating an external user as an internal user. .
Researchers tested the technique in the field and successfully delivered a command and control payload to an inbox of target organizations, as part of a covert Red Team engagement.
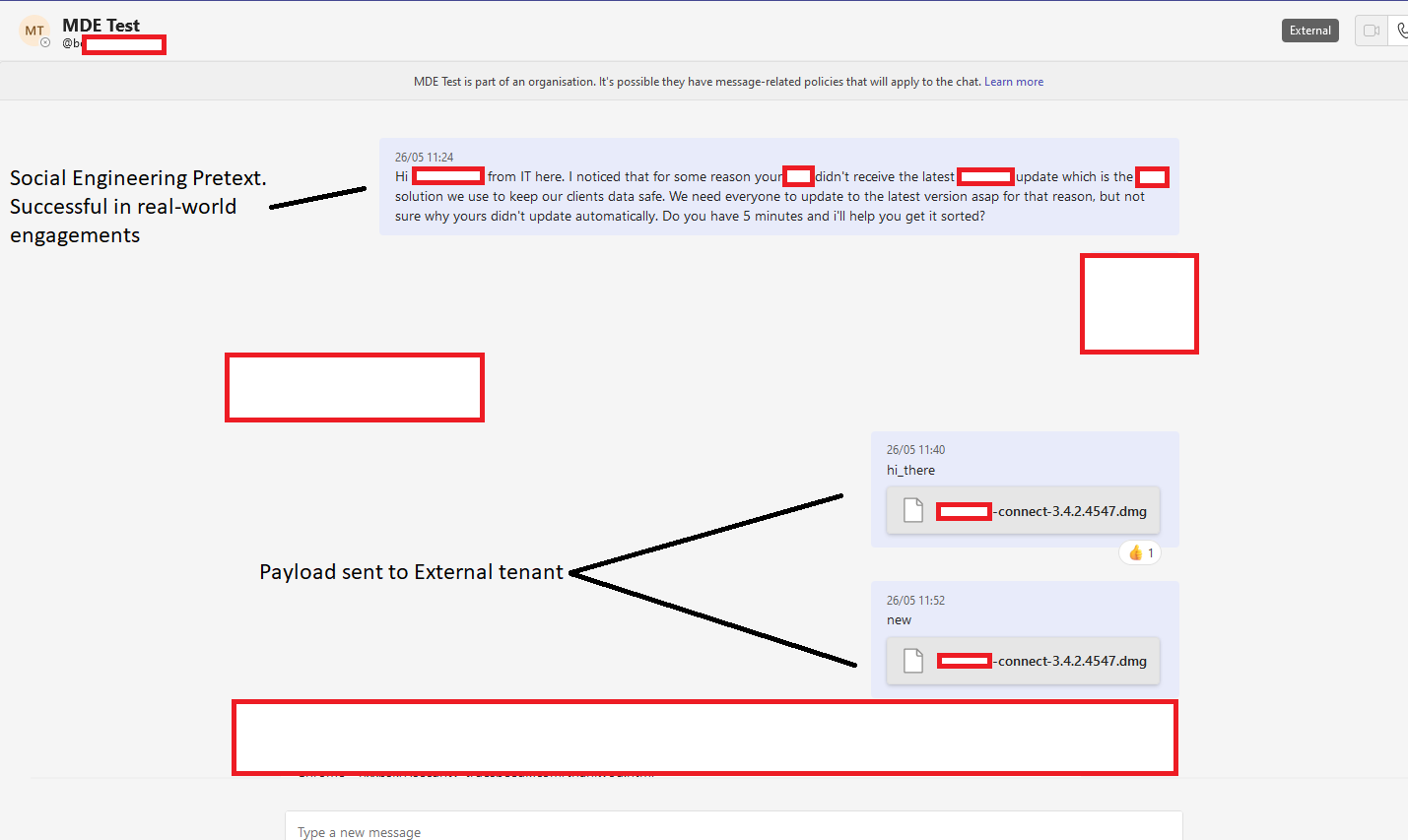
This attack bypasses existing security measures and anti-phishing training guidance, giving attackers a fairly easy way to infect any organization using Microsoft Teams with its default configuration.
Additionally, if the attacker registers a domain similar to the target organizations on Microsoft 365, their messages could appear as if they came from someone inside the organization, and not an external tenant, thus increasing the probability that the target downloads the file. .
Microsoft’s response
The researchers reported their findings to Microsoft, assuming the impact was significant enough to warrant an immediate response from the tech giant.
Although Microsoft confirmed the existence of the flaw, the response was that “it does not meet the bar of immediate services”, which means that the company does not see any urgency in fixing it.
BleepingComputer has also reached out to Microsoft to ask when they plan to fix the issue and if its severity has been reconsidered, but we haven’t received a response as of press time.
The recommended action for organizations that use Microsoft Teams and do not need to maintain regular communication with external tenants is to disable this feature from “Microsoft Teams admin center > External access”.
If external communication channels need to be maintained, organizations can define specific domains in an allowlist, to reduce the risk of exploitation.
Jumpsec researchers have also submitted a request to add tenant-related external events to software logging, which could help prevent attacks as they unfold, so vote if you want to help pressure Microsoft into action.
[ad_2]
Source link
