[ad_1]

Microsoft fixed a known issue triggering Windows security warnings that Local Security Authority (LSA) protection is disabled by removing the UI from the Settings feature.
LSA protection helps defend Windows users against credential theft by preventing the injection of untrusted code into the LSASS.exe process to dump its memory or extract information.
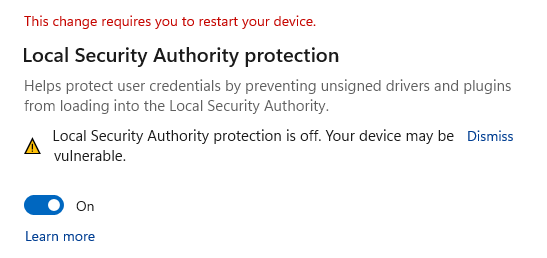
Microsoft recognized a known issue causing persistent alerts asking to restart Windows following a report flow mentioning “Local Security Authority protection is disabled. Your device may be vulnerable.” warnings even if LSA protection was already enabled.
As revealed by the company, the issue affects Windows 11 21H2 and 22H2 systems, and it was caused by a buggy Microsoft Defender Antivirus antimalware platform update.
Redmond now says they have fixed confusing alerts in a new Microsoft Defender Antivirus anti-malware platform update.
“This issue has been addressed in an update to Microsoft Defender Antivirus Antimalware Platform KB5007651 (Version 1.0.2303.27001). If you want to install the update before it installs automatically, you’ll need to check for updates,” read an update to Microsoft’s Windows Health dashboard.
However, BleepingComputer learned that this issue was resolved by completely removing the LSA protection UI from the Windows Settings app, causing the warnings to disappear.
BleepingComputer also learned that LSA protection is still supported, although the UI has been removed from the settings and users can still manually enable/disable security functionality using registry or group/MDM policies.
However, without the UI, there is no longer a way to check from Windows settings if LSA protection is enabled.
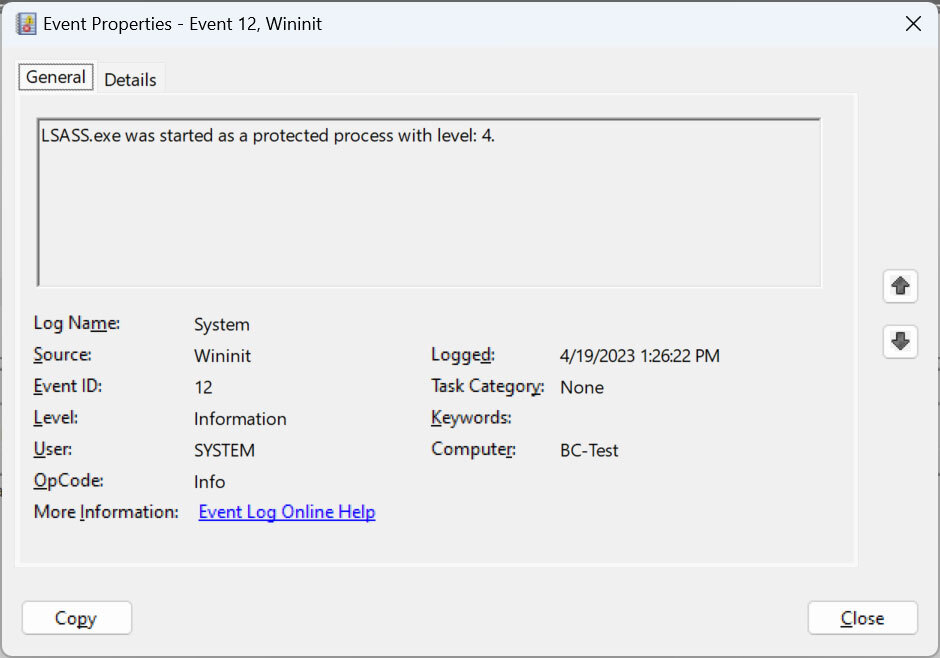
Despite this, users can still check if the feature is enabled using Windows Event Viewer. If you find a Wininit event 12 that says “LSASS.exe was started as a protected process with level: 4”, that means the process is isolated and protected by LSA protection.
Kernel-mode hardware-enforced stack protection warnings
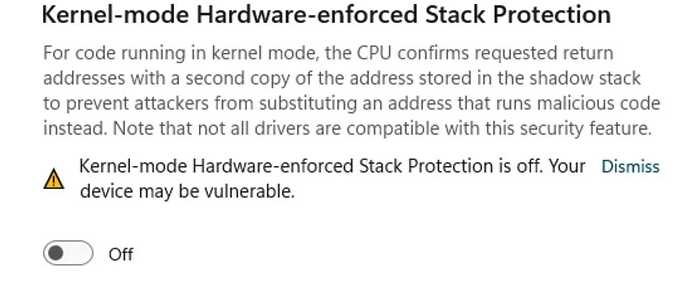
Like BleepingComputer reported last week after removing the LSA protection UI from the Windows Security Settings > Device Security > Core Isolation page, users now see similar alertswarning them this time that their devices may be vulnerable because hardware-enhanced stack protection (HSP) in kernel mode is disabled due to conflicting drivers.
Kernel-mode HSP protects against Return Oriented Programming (ROP)-based control flow attacks that can lead to malicious code execution using modern CPU hardware features such as flow enforcement technology. Intel’s Control (CET) or ARM’s Pointer Authentication Code (PAC).
Once this security feature is enabled, Windows ensures that no incompatible driver is loaded; however, users report that the list of incompatible drivers is empty on affected systems.
Additionally, some conflicting game anti-cheat drivers detected as incompatible will cause Windows to crash or prevent games from launching when kernel-mode HSP is enabled. Games affected by this issue include PUBG, Valorant (Riot Vanguard), blood hunt, Destiny 2, Genshin Impact, Star Fantasy Online 2 (Game Guard), and Dayz.
Last month, Microsoft also announcement that LSA protection would be enabled by default for Windows 11 Insiders in the Canary channel if their systems pass an incompatibility audit check (Microsoft has not yet provided details on the audited compatibility issues).
[ad_2]
Source link
