[ad_1]
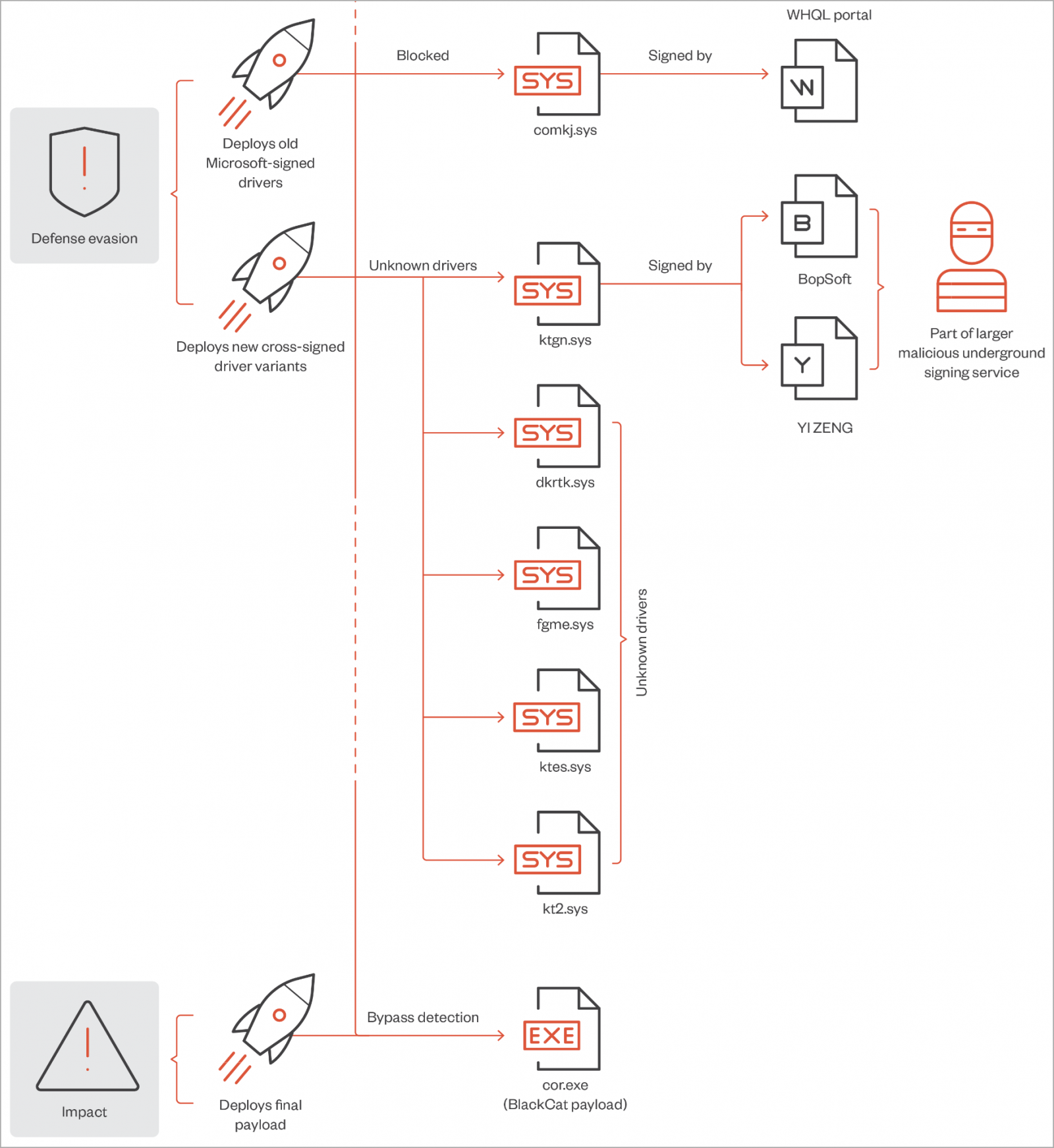
The ALPHV (aka BlackCat) ransomware group has been observed using malicious signed Windows kernel drivers to evade detection by security software during attacks.
The driver seen by Trend Micro is an enhanced version of the malware known as “POORTRY” that Microsoft, Mandiant, Sophos and SentinelOne have spotted in ransomware attacks. at the end of last year.
POORTRY malware is a Windows kernel driver signed using stolen keys belonging to legitimate Microsoft Windows Hardware Developer Program accounts.
This malicious driver was used by the UNC3944 hacking group, also known as 0ktapus and Scattered Spider, to terminate security software running on a Windows device to evade detection.
While security software is generally protected against termination or tampering, since Windows kernel drivers run with the highest operating system privileges, they can be used to shut down almost any process.
Trend Micro claims that ransomware actors attempted to use the Microsoft-signed POORTRY driver, but its detection rates were high due to the publicity it received and code-signing keys were revoked.
Therefore, the hackers deployed an updated version of the POORTRY kernel driver signed using a stolen or leaked cross-signing certificate.
The new driver used by the How BlackCat ransomware works helps them elevate their privileges on compromised machines and then kill processes related to security guards.
Additionally, it can provide a loose connection between the ransomware gang and the UNC3944/Scattered Spider hacking groups.
The Malicious Windows Kernel Driver
The signed driver seen by Trend Micro in the February 2023 BlackCat attacks is “ktgn.sys”, dropped on the victim’s file system in the %Temp% folder, then loaded by a user-mode program named “tjr.exe “.
Analysts say digital signature of ktgn.sys has been revoked; however, the driver will still load smoothly on 64-bit Windows systems with signing policies applied.
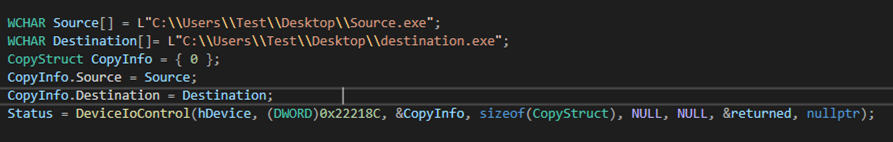
The malicious kernel driver exposes an IOCTL interface that allows the user-mode client, tjr.exe, to issue commands that the driver will execute with Windows kernel privileges.
“From our analysis of what happens when a user interfaces with this driver, we observed that it uses only one of the exposed Device Input and Output Control (IOCTL) codes – Kill Process, which is used to kill the security agent processes installed on the system.” explains the Trend Micro Report.
Trend Micro analysts observed the following exposed commands that can be sent to the driver:
- Enable driver
- Disable the driver after the user mode client completes its operation
- Kill any process in user mode
- Delete specific file paths
- Force deletion of a file by freeing its handles and terminating running processes using it
- Copy files
- Force file copying using a similar mechanism to force delete
- Log process/thread notification callbacks
- Unregister process/thread notification callbacks
- Reboot the system by calling the ‘HalReturnToFirmware’ API
Trend Micro comments that the two commands used for process/thread notification callbacks do not work, indicating that the driver is currently in development or still in testing.
It is recommended that system administrators use indicators of compromise shared by Trend Micro and add malicious drivers used by ransomware actors to the Windows driver block list.
Windows administrators should also ensure that “Driver Signature Enforcement” is enabled, which blocks the installation of any drivers that do not have a valid digital signature.
[ad_2]
Source link
