[ad_1]

The Housing Authority of the City of Los Angeles (HACLA) is warning of a “data security event” after the LockBit ransomware gang targeted the organization and leaked data stolen in the attack.
HACLA is a state-licensed agency that provides affordable housing to low-income individuals and families in Los Angeles, California.
The government agency, which operates on an annual budget of $1 billion, also provides job training and education to help eligible families achieve self-sufficiency and improve their quality of life.
According data breach noticeon December 31, 2022, HACLA discovered that its network’s computer systems had been encrypted, causing the agency’s IT team to shut down all servers and launch an investigation.
The investigation into the incident concluded on February 13, 2023, revealing that hackers gained unauthorized access to the systems between January 15, 2022 and December 31, 2022.
Server logs examined showed that hackers may have accessed the following information belonging to HACLA members:
- Full name
- Social Security Number (SSN)
- Date of birth
- Passport number
- Driving license
- State identification number
- Tax Identification Number
- Military identification number
- Government issued identification number
- Credit/debit card number
- Financial account number
- Health insurance information
- Medical Information
HACLA notified affected individuals via mail, which includes instructions on monitoring their accounts, sending fraud alerts, and reporting incidents of identity theft to authorities.
LockBit claimed responsibility for the attack
The attack on HACLA was claimed by the LockBit 3.0 ransomware gang, one of the most active and notorious RaaS (ransomware-as-a-service) operations.
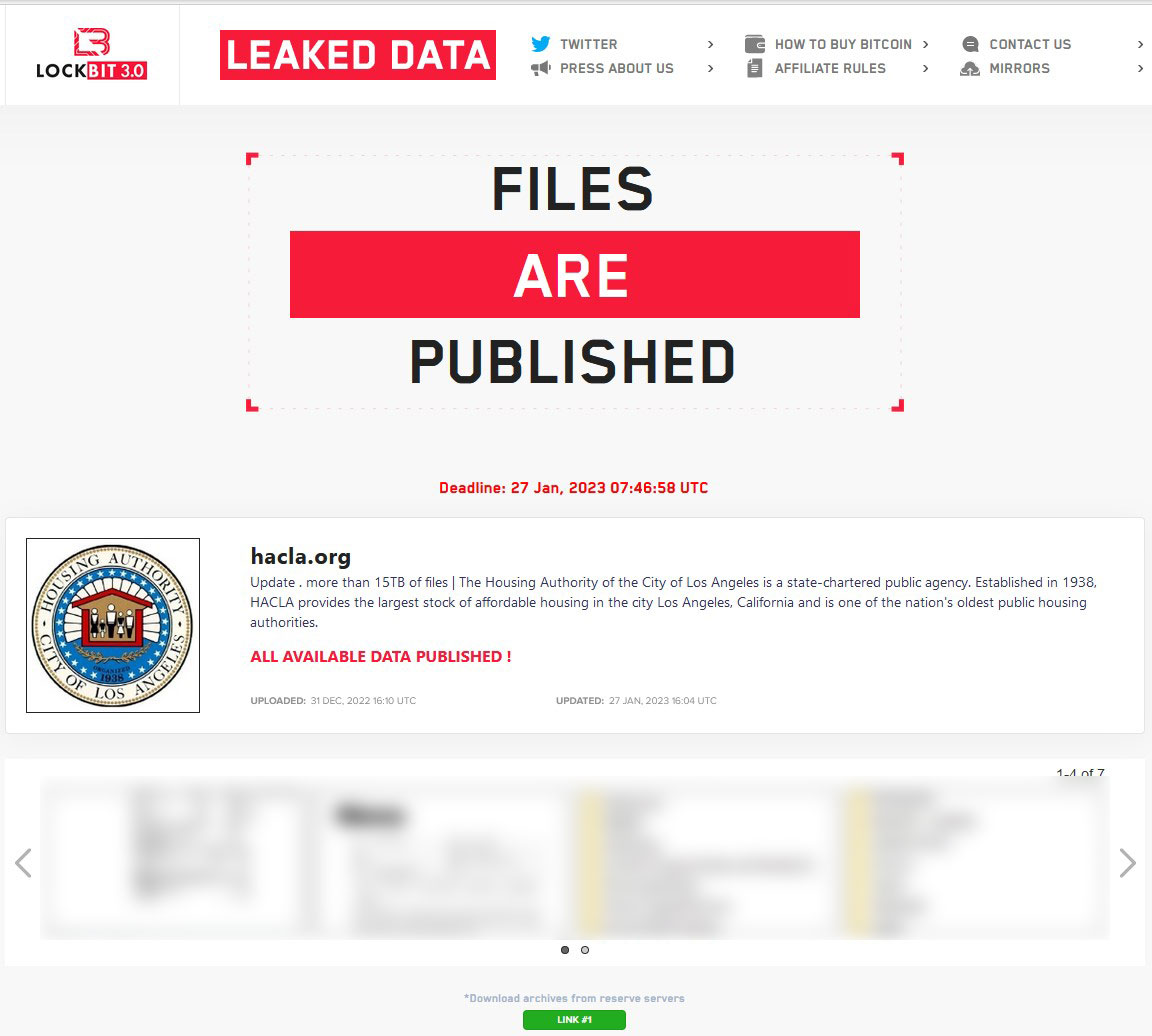
The threat actors uploaded samples of the files they claim to have stolen from HACLA’s network on December 31, 2022, then continued their threat to release all files on January 27, 2023.
This indicates that the negotiations for the ransom payment failed and the government agency refused to fulfill the demands of the cyber criminals.
However, about 1.5 months after this data was published, the download link on LockBit’s extortion site no longer works, mitigating the impact somewhat.
The leaked dataset has not yet been redistributed on known hacker forums either.
[ad_2]
Source link
