[ad_1]

Another ransomware operation, the LockBit gang, is now threatening to release what it describes as stolen files from systems in the city of Oakland.
However, the gang has yet to release any evidence that they stole files from the West Coast Port City network.
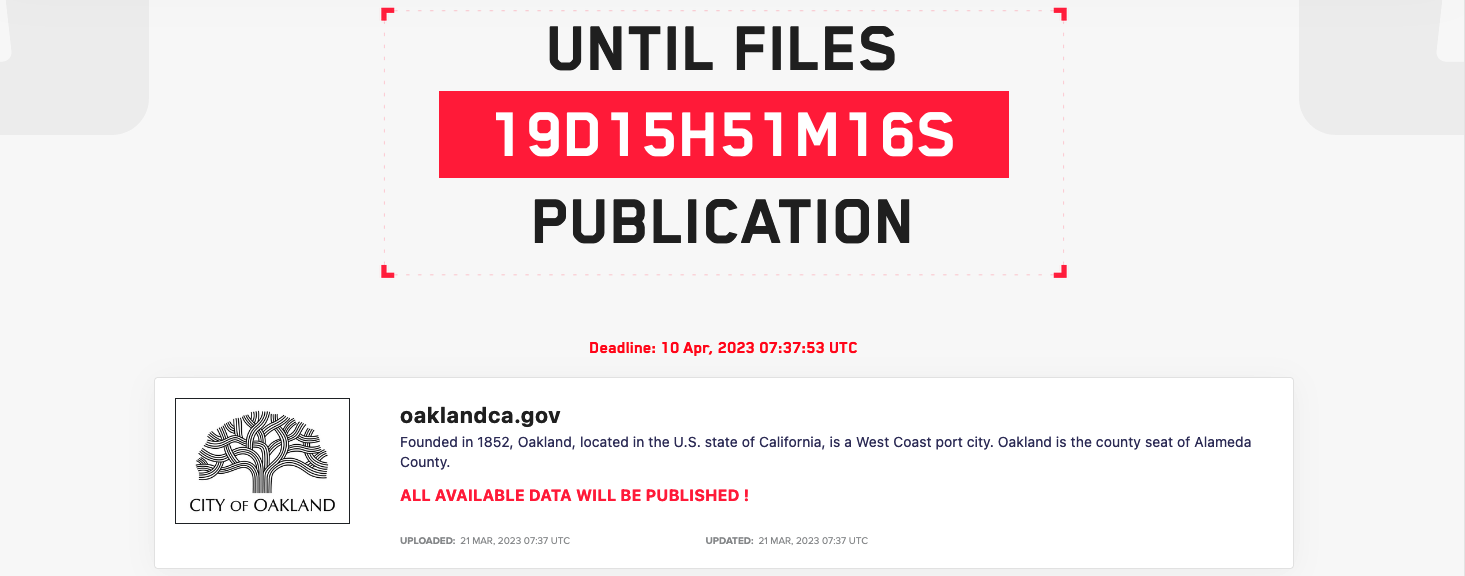
On the new entry added to the LockBit dark web data leak website, they only warn that all the data they have will be released in 19 days, April 10.
LockBit has already made statements that have proven to be false at least once.
In June 2022, the ransomware group claimed to have hacked into Mandiant’s systems and stolen hundreds of thousands of files, which turned out to be a publicity stunt after releasing a statement saying he had no connection to the Evil Corp cybercrime gang instead of leaking stolen data.
The City of Oakland has yet to release a statement regarding the LockBit ransomware gang’s claims.
This is the second ransomware gang claiming to have stolen Oakland city data after Play ransomware took the responsibility beginning of March for a cyberattack in mid-February.
The Play gang then began to release what they claimed was the stolen City of Oakland data in the form of 10GB multipart RAR archives containing confidential documents, employee information, passports and identity documents.
Employee Personal Information Disclosed Online
The City issued a statement the day after the attack claimed by the Play ransomware gang, confirming an investigation into what was leaked online and began sending data breach notification letters to those concerned on March 15.
“On February 8, 2023, the City of Oakland experienced a cybersecurity incident involving malware, which encrypted some of our systems,” the City of Oakland said in letters sent to affected employees.
“Through investigation, the City has determined that between February 6, 2023 and February 9, 2023, an unauthorized actor accessed and/or took certain files stored on the City’s computer servers.”
The affected employees were told that some of their personal information had been stolen from the city’s compromised systems, including names, addresses, driver’s license numbers and social security numbers.
The city of Oakland also has declared a local state of emergency the same day due to the impact of the ransomware attack which forced him to take all of his computer systems offline on February 8 until the network was secured.
While this ransomware attack did not impact 911 and the city’s emergency services, other systems had to be taken offline, including phone service and systems used to process calls. reports, collect payments and issue permits and licenses.
Municipal systems will likely be online next month
A page on the city’s official website tracking the latest developments and efforts to restore services after the February ransomware attack was last updated nearly two weeks ago, on March 8.
In a Monday press conferenceOakland Mayor Sheng Thao said the city was still working to restore the affected systems and the FBI was also assisting with the ongoing investigation into the incident.
When asked when all systems in the city will be back online, Thao replied, “We’re optimistic we can get there in the next few weeks, or maybe next month.”
The city of Oakland wouldn’t be the first victim of ransomware breached multiple times in days or weeks.
As Sophos X-Ops Incident Responders revealed in an August 2022 reportan automotive supplier had its systems encrypted by three different ransomware gangs in two weeks, with two of the attacks occurring in just two hours.
[ad_2]
Source link
