[ad_1]

RTM Locker is the latest enterprise-targeted ransomware operation that deploys a Linux encryptor that targets virtual machines on VMware ESXi servers.
The RTM (Read The Manual) cybercrime gang has been active in financial fraud since at least 2015known to distribute a custom banking Trojan used to steal money from victims.
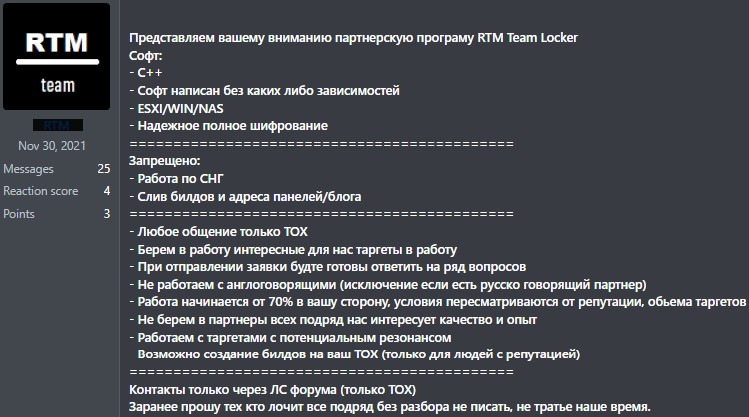
This month, cybersecurity firm Trellix reported that RTM Locker launched a new Ransomware-as-a-Service (Raas) operation and began recruiting affiliates, including those from the former cybercrime syndicate Conti.
“The ‘Read The Manual’ Locker gang uses affiliates to ransom victims, who are all forced to abide by the gang’s strict rules,” explains Trellix.
“The group’s business setup, where affiliates are required to remain active or notify the gang of their departure, shows the organizational maturity of the group, as has also been seen in other groups, such as Conti.”
Security researcher MalwareHunterTeam also shared a sample of RTM Locker with BleepingComputer in December 2022, indicating that this RaaS has been active for at least five months.
At the time, Trellix and MalwareHunterTeam only saw a Windows ransomware encryptor, but as Uptycs reported yesterday, RTM has expanded its targeting to Linux and VMware ESXi servers.
Target VMware ESXi
In recent years, the company has moved to virtual machines (VMs) as they offer improved device management and much more efficient resource management. For this reason, an organization’s servers are typically spread across a combination of dedicated devices and VMware ESXi servers running multiple virtual servers.
Ransomware operations have followed this trend and created dedicated Linux encryptors targeting ESXi servers to properly encrypt all data used by the enterprise.
BleepingComputer has seen this with nearly every enterprise-targeted ransomware operation, including Royal, basta black, LockBit, BlackMatter, AvosLocker, REvil, Hello Kitty, RansomEXX, Hiveand now, RTM Locker.
In a new report by Uptycs, researchers analyzed a Linux variant of the RTM Locker based on the leaked source code of the now defunct Babuk ransomware.
The RTM Locker Linux encryptor appears to have been created explicitly to attack VMware ESXi systems, as it contains numerous references to commands used to manage virtual machines.
Once launched, the encryptor will first attempt to encrypt all VMware ESXi VMs by first gathering a list of running VMs using the following esxcli command:
esxcli vm process list >> vmlist.tmp.txt
The encryptor then shuts down all running VMs using the following command:
esxcli vm process kill -t=force -wAfter all virtual machines have been shut down, the encryptor begins to encrypt files with the following file extensions: .log (log files), .vmdk (virtual disks), .vmem (virtual machine memory), .vswp (files swap) and .vmsn (virtual machine snapshots).
All of these files are associated with virtual machines running on VMware ESXi.
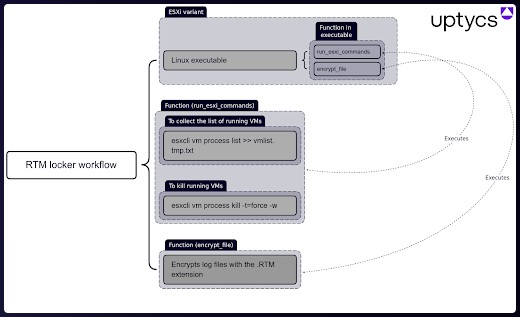
Like Babuk, RTM uses random number generation and ECDH on Curve25519 for asymmetric encryption, but instead of Sosemanuk it relies on ChaCha20 for symmetric encryption.
The result is secure and has not been cracked yet, so there are no free decryptors available for RTM Locker at the moment.
Uptycs also comments that the cryptographic algorithms are “statically implemented” in the binary code, which makes the encryption process more reliable.
When encrypting files, the encryptor adds the .RTM file extension to encrypted filenames, and after that creates ransom notes named !!! Warning !!! on the infected system.
The notes threaten to contact RTM “support” within 48 hours via Tox to negotiate a ransom payment, otherwise the victim’s stolen data will be released.
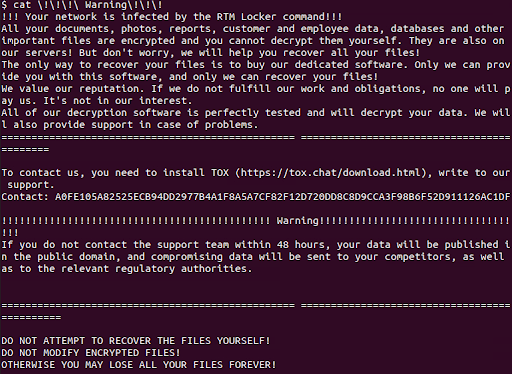
In the past, RTM Locker used payment trading sites on the following TOR sites, but recently switched to TOX for communications.
nvfutdbq3ubteaxj4m2jyihov5aa4akfudsj5h7vhyrvfarfra26ksyd.onion
3wugtklp46ufx7dnr6j5cd6ate7wnvnivsyvwuni7hqcqt7hm5r72nid.onionThe existence of a version targeting ESXi is enough to categorize RTM Locker as a significant threat to the enterprise.
However, the good news is that BleepingComputer’s research has shown that the group isn’t particularly active, although that may change in the future.
[ad_2]
Source link
