[ad_1]

Notorious North Korean state-backed hackers, known as the Lazarus Group, are now targeting vulnerable Windows Internet Information Services (IIS) web servers to gain initial access to corporate networks.
Lazarus is primarily financially motivated, with many analysts believing that the hackers’ malicious activities help fund North Korea’s weapons development programs. However, the group has also been involved in several espionage operations.
The latest tactic of targeting Windows IIS servers has been discovered by South Korean researchers in AhnLab Security Emergency Response Center (A SECOND).
Attacks on IIS servers
Windows Internet Information Services (IIS) web servers are used by organizations of all sizes to host web content such as sites, applications, and services, such as Outlook on the Web to Microsoft Exchange.
It is a flexible solution available since the launch of Windows NT, supporting HTTP, HTTPS, FTP, FTPS, SMTP and NNTP protocols.
However, if servers are poorly managed or outdated, they can serve as network entry points for hackers.
Previously, Symantec reported hackers deploying malware on IIS execute commands on hacked systems via web requests, avoiding detection by security tools.
A separate report revealed that a hacking group named “Cranfly” employed a unknown technique malware control using IIS web server logs.
Lazarus attacks against IIS
Lazarus first gains access to IIS servers using known vulnerabilities or misconfigurations that allow hackers to create files on the IIS server using the w3wp.exe process.
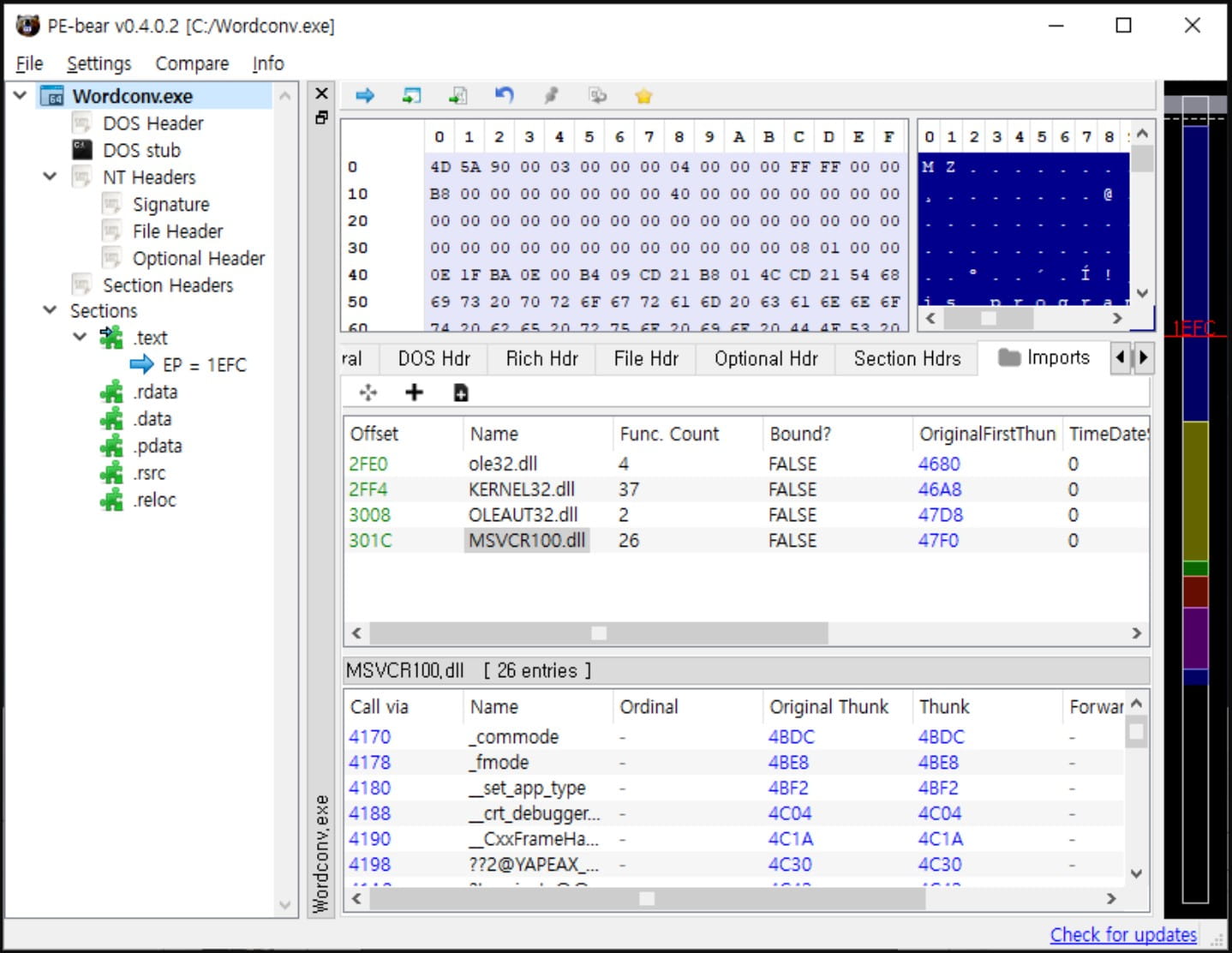
Hackers drop “Wordconv.exe”, a legitimate file that is part of Microsoft Office, a malicious DLL (“msvcr100.dll”) in the same folder and an encoded file named “msvcr100.dat”.
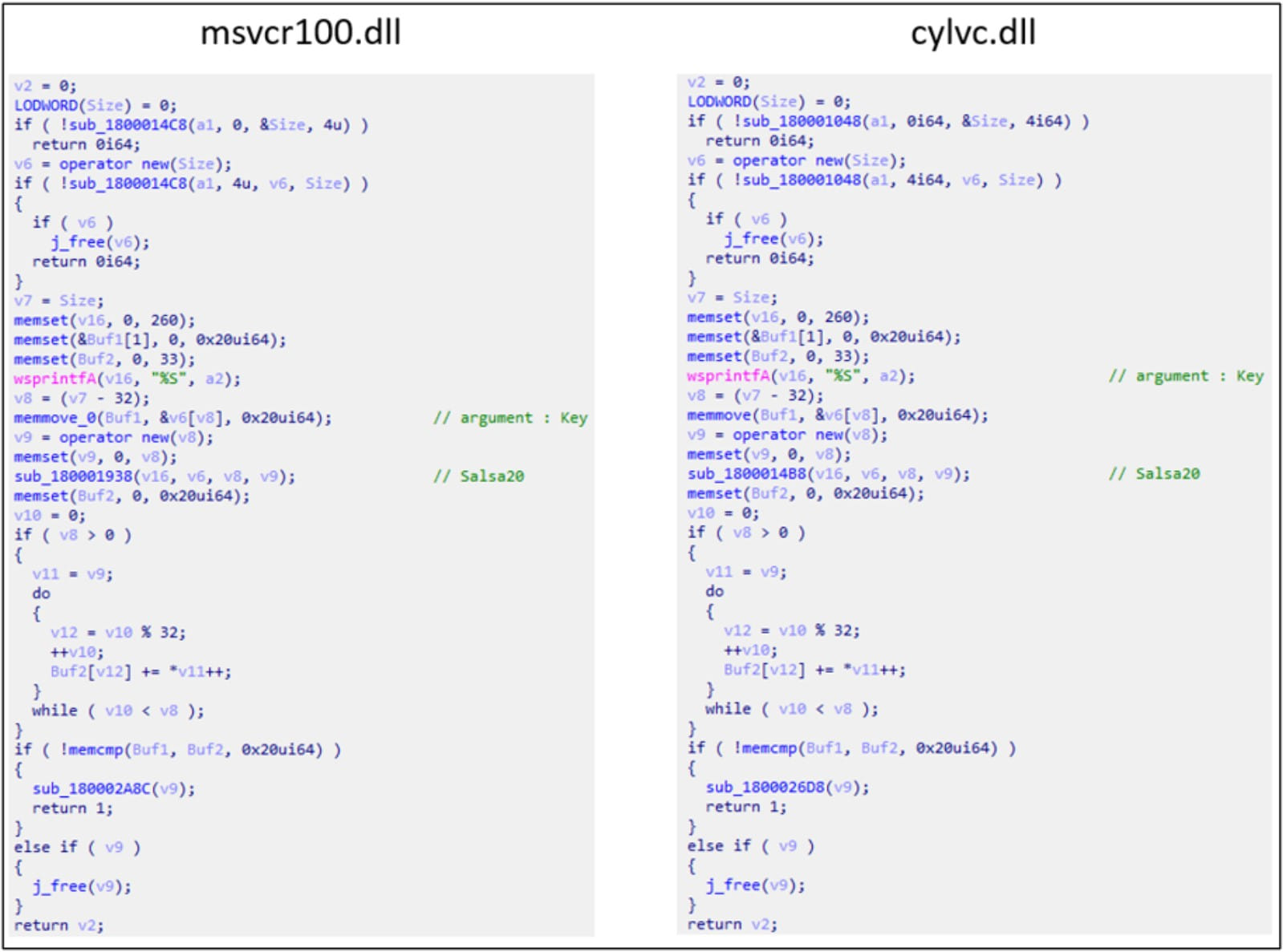
When launching “Wordconv.exe”, the malicious code in the DLL loads to decrypt the Salsa20 encoded executable from msvcr100.dat and run it in memory where anti-virus tools cannot detect it.
ASEC found several code similarities between ‘msvcr100.dll’ and another malware it observed last year‘cylvc.dll’, which was used by Lazarus to disable anti-malware programs using the “bring your own vulnerable driver” technique.
Therefore, ASEC considers the newly discovered DLL file as a new variant of the same malware.
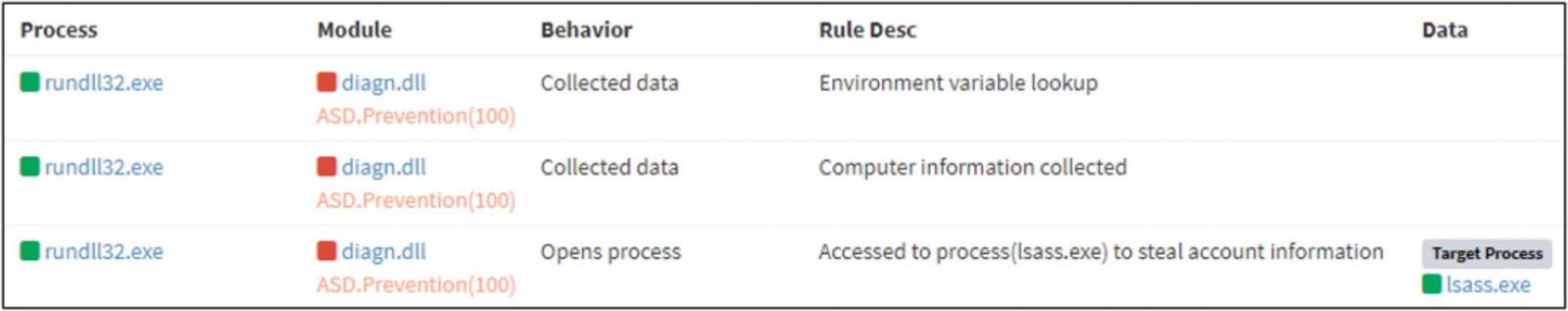
In the second phase of the attack, Lazarus creates a second piece of malware (‘diagn.dll’) by exploiting a Notepad++ plugin.
This second malware this time receives a new payload encoded with the RC6 algorithm, decrypts it using a hard-coded key and executes it in memory for evasion.
ASEC could not determine what this payload did to the hacked system, but saw signs of LSASS dumps indicating credential theft activity.
The final step of the Lazarus attack was to perform network reconnaissance and lateral movement through port 3389 (Remote Desktop) using valid user credentials, presumably stolen in the previous step.
However, ASEC did not discover any further malicious activity after the attackers spread laterally through the network.
As Lazarus relies heavily on DLL sideloading as part of its attacks, ASEC recommends that organizations monitor abnormal process execution.
“In particular, since the threat group mainly uses the DLL side-loading technique during its initial infiltrations, enterprises should proactively monitor abnormal process execution relationships and take preventive measures to prevent the group from threats to carry out activities such as information exfiltration and lateral movement,” concludes the ASEC report.
[ad_2]
Source link
