[ad_1]

The North Korean state-sponsored hacking group Lazarus is attacking Windows Internet Information Service (IIS) web servers to hijack them for the purpose of distributing malware.
IIS is Microsoft’s web server solution used to host websites or application services, such as Microsoft Exchange’s Outlook on the web.
South Korean security analysts ASEC previously reported that Lazarus targets IIS servers for a first access to corporate networks. Today, the cybersecurity firm claims that the threat group exploits poorly protected IIS services for malware distribution Also.
The main advantage of this technique is the ease of infecting visitors to websites or users of services hosted on hacked IIS servers belonging to trustworthy organizations.
Attacks on South Korea
In recent attacks observed by ASEC analysts, Lazarus compromised legitimate South Korean websites to perform “Watering Hole” attacks on visitors using a vulnerable version of the INISAFE CrossWeb EX V6 software.
Many public and private organizations in South Korea use this particular software for electronic financial transactions, security certification, internet banking, etc.
The INISAFE vulnerability has already been documented by both Symantec And A SECOND in 2022, explaining that it was operated using HTML attachments at the time.
“A typical attack begins when a malicious HTM file is received, likely in the form of a malicious link in an email or downloaded from the web. The HTM file is copied into a DLL file called scskapplink.dll and injected into the legitimate INISAFE Web EX Client system management software,” Symantec’s 2022 report explains.
Exploiting the flaw retrieves a malicious “SCSKAppLink.dll” payload from an IIS web server that was already compromised before the attack to use as a malware distribution server.
“The download URL for ‘SCSKAppLink.dll’ has been identified as the aforementioned IIS web server,” says ASEC’s new report.
“This means the threat actor attacked and took control of IIS web servers before using them as servers to distribute malware.”
ASEC has not analyzed the particular payload, but says it is likely a malware downloader seen in other recent Lazarus campaigns.
Then, Lazarus uses the “JuicyPotato” privilege escalation malware (“usopriv.exe”) to gain higher-level access to the compromised system.
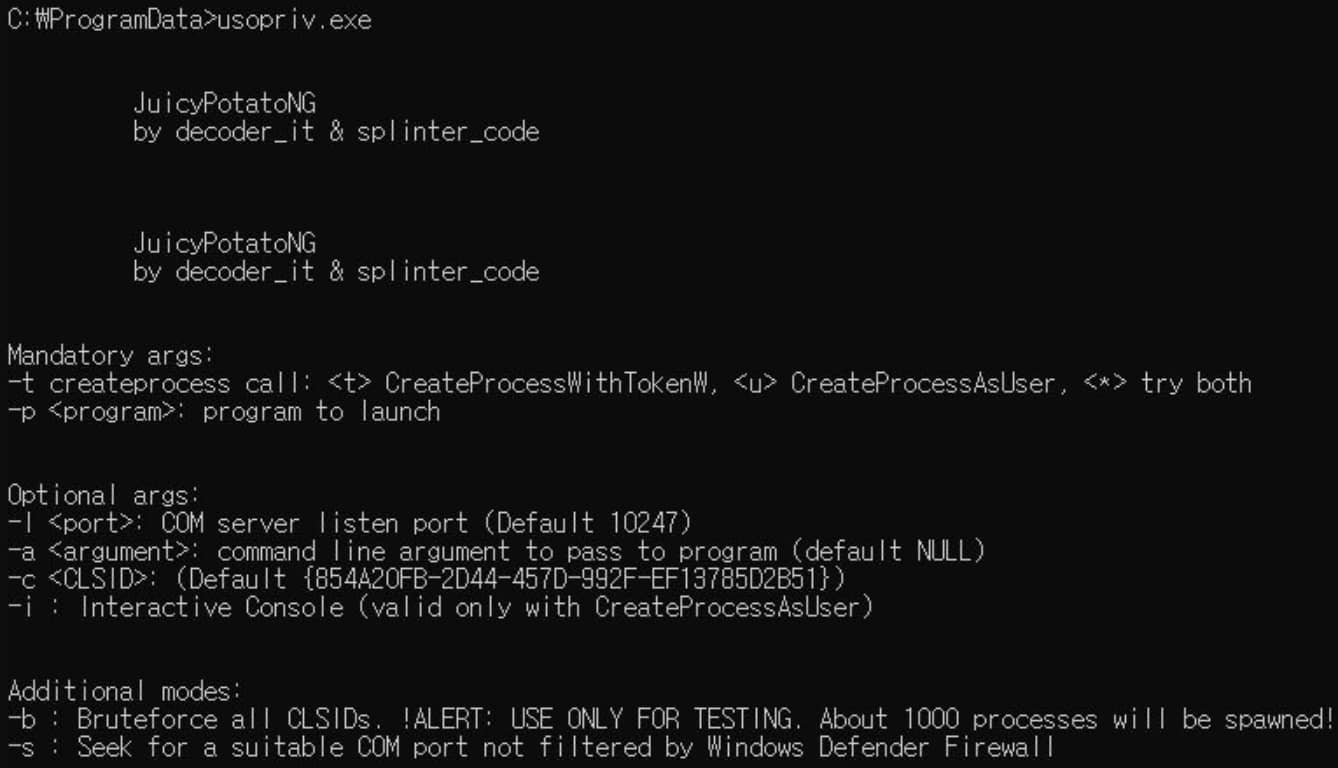
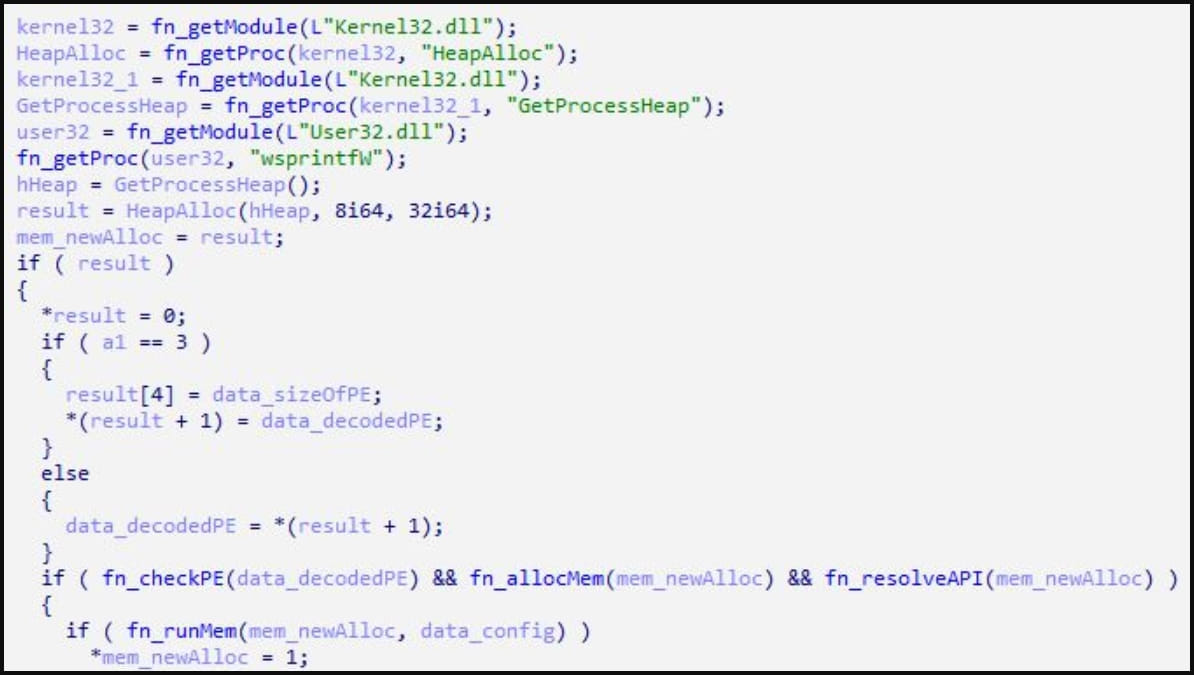
JuicyPotato is used to execute a second malware loader (‘usoshared.dat’) which decrypts downloaded data files and executes them in memory for AV evasion.
ASEC recommends that NISAFE CrossWeb EX V6 users update the software to its latest version, as Lazarus exploitation of known vulnerabilities in the product has been ongoing since at least April 2022.
The security company advises users to upgrade to version 3.3.2.41 or later and states fix instructions it was published four months ago, highlighting the Lazarus menace.
Microsoft application servers are becoming a popular target for hackers to use in distributing malware, likely due to their trusted nature.
Just last week, CERT-UA and Microsoft reported that Russian Turla hackers were using compromised Microsoft Exchange servers to provide backdoors to their targets.
[ad_2]
Source link
