[ad_1]

The state-sponsored North Korean hacker group Kimsuky (aka APT43) has posed as journalists and academics in spear-phishing campaigns to gather intelligence from think tanks, research centers , academic institutions and various media.
The warning comes from several government agencies in the United States and South Korea that track hacker activity and have analyzed the group’s recent campaigns and themes used for attacks.
A joint advisory by the Federal Bureau of Investigation (FBI), US State Department, National Security Agency (NSA), alongside South Korea’s National Intelligence Service (NIS), National Police Agency (NPA) and the Ministry of Foreign Affairs (MOFA), notes that Kimsuky is part of the Reconnaissance General Bureau (RGB) of North Korea.
Also known as Thallium and Velvet Chollima, Kimsuky has conducted large-scale espionage campaigns supporting national intelligence objectives since at least 2012.
“Some targeted entities may be unaware of the threat posed by these social engineering campaigns, either because they do not perceive their research and communications to be of a sensitive nature, or because they are unaware of how these efforts are fueling the efforts broader cyber espionage activities of the regime”, read the review.
“However, […] North Korea relies heavily on intelligence obtained by compromising political analysts […] (and) successful compromises allow Kimsuky actors to create more credible and effective spear-phishing emails that can be exploited against more sensitive and higher-value targets.
Spear-phishing as journalists
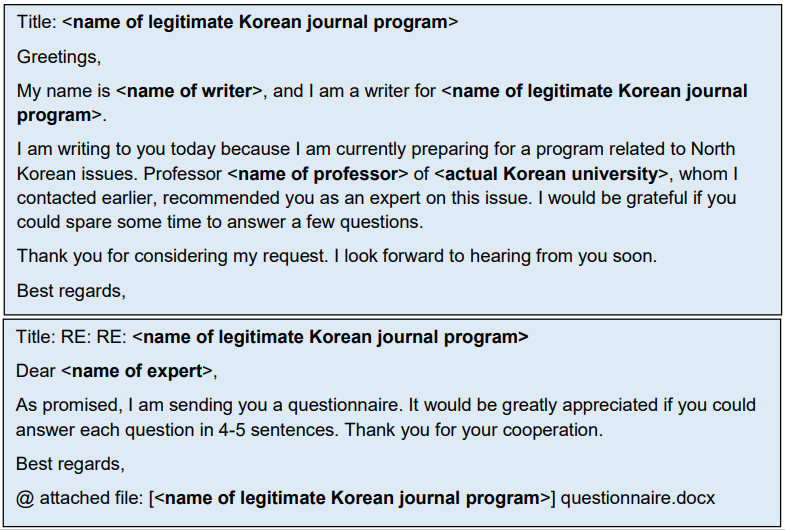
Kimsuky hackers meticulously plan and execute their spear attacks using email addresses that closely resemble those of real individuals and creating compelling and realistic content for communication with the target.
“For more than a decade, the Kimsuky cast continued to hone their social engineering techniques and made their spear-phishing efforts increasingly difficult to discern,” the notice warns.
In many cases, hackers pose as journalists and writers to inquire about current political events on the Korean Peninsula, North Korea’s weapons program, US talks, China’s position, etc. .
Themes observed include requests for information, invitations to interviews, ongoing investigation, and requests for reports or document reviews.
The initial emails are usually free of malware or attachments, as their role is to gain the trust of the target rather than to reach a quick compromise.
If the target does not respond to these emails, Kimsuky comes back with a follow-up message after a few days.
The FBI says that despite adversary efforts, English emails sometimes have sentence structure and may contain entire excerpts of the victim’s previous communication with legitimate contacts, which has been stolen.
source: US government
When the target is South Korean, the phishing message may contain a distinct North Korean dialect.
Additionally, the addresses used to send phishing emails impersonate legitimate individuals or entities; however, they still contain subtle misspellings.
How to Stop Kimsuky
The advisory provides a set of mitigations, including using strong passwords to protect accounts and enabling multi-factor authentication (MFA).
Also, users are advised not to enable macros on documents in emails sent by strangers, regardless of the claim of the messages.
The same caution applies to documents sent from known cloud hosting services, as the legitimacy of the platforms is no guarantee of the security of these files.
If in doubt about a message claiming to be from a media group or journalist, visit that organization’s official website and confirm the validity of the contact information.
The joint advisory recommends conducting a preliminary video call as an effective strategy to dispel any uncertainty about potential spoofing before deciding to pursue communication.
[ad_2]
Source link
