[ad_1]

One of the easiest ways to steal a user’s credentials is to use a fake login page or application. An unwitting user can quickly give an attacker crucial entry into an organization’s systems with the daily act of typing their password in the wrong place.
Often a phishing attempt comes in the form of an email that looks dangerously realistic and directs a user to a fake login page. Truly convincing phishing attempts mimic pixel-perfect logos, verbiage, and layout.
Often the only freebie is the URL, but there are also ways to obfuscate and hide it.
Protect users with enhanced phishing protection in Windows 11
To help combat the constant risk of password theft, Microsoft has added phishing protection in Windows 11 Version 22H2.
When activated, Improved Phishing Protection is offered through Microsoft Defender SmartScreen. But what does it actually offer users?
Enhanced Phishing Protection inspects URLs and all running processes to assess whether the site or application appears to possibly host malicious content or is insecure.
If so, SmartScreen leverages telemetry data from a host of Microsoft security products to notify the user and block the offending site or app.
Because this integration is deeply integrated into Windows through OS-level integration with Microsoft Defender, deeper inspection of processes and URLs is available compared to many competing products. Additionally, Enhanced Phishing Protection is offered as a built-in feature in Windows 11 without requiring additional installation or licensing.
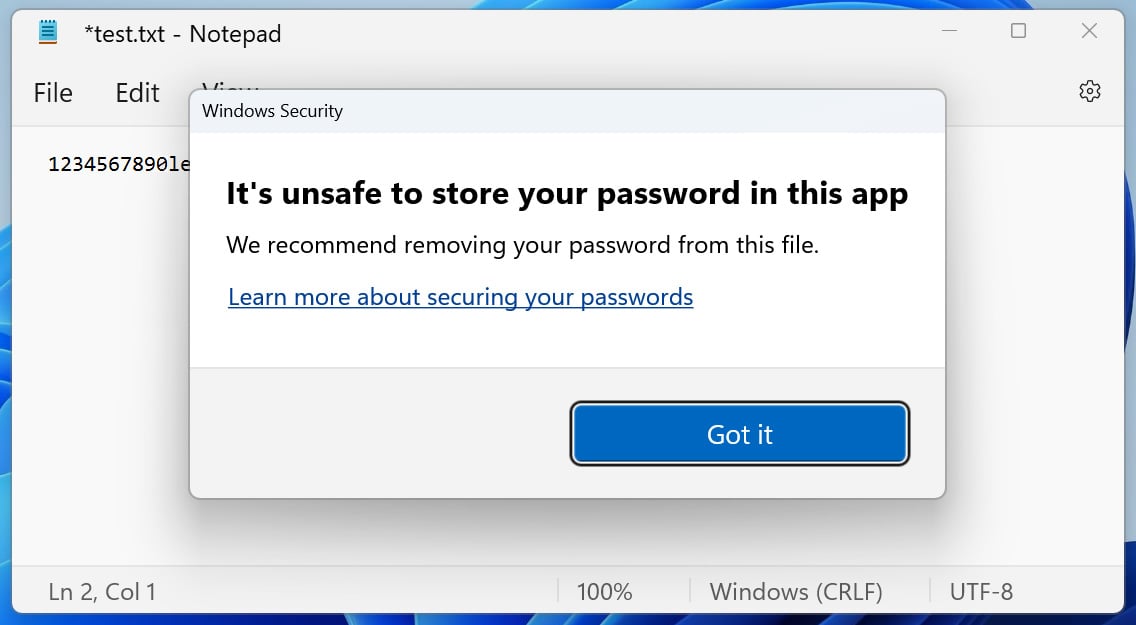
If Enhanced Phishing Protection detects that a user has entered their Windows password on a website or application, an alert and prompt appear to notify the user to change their password.
If the password is simply entered into an application like notepad, the protection recommends the user to remove their password from this file.
This proactive approach helps keep users safe and does not allow a potential attacker to take advantage of their new credentials.
Real consequences of phishing attacks
Phishing campaigns are becoming too easy for hackers to create.
A Phishing-as-a-service (PhaaS) platform named Caffeine offers open registration and focuses on Microsoft 365 connections but with a subscription model and anti-detection and anti-analysis protections.
The speed at which a new threat actor can attempt a realistic phishing attempt on a victim becomes difficult to manage.
A a concrete example of this is American Airlines. They discovered that an employee’s Microsoft 365 account had been hacked. From this perspective, multiple employee accounts were accessed and exploited to send even more phishing emails from inside the organization.
At the depots, the data breach appears to affect more than 1,700 employees and customers. American Airlines must now offer compensation and protection against future threats. Not to mention the time it will take to secure and deal with the damage caused by the phishing attack.
Considerations when configuring Enhanced Phishing Protection
As with most solutions, there are several caveats. This integration only works with non-Windows Hello logins. If you don’t use a password to log on to your computer, enhanced protection is not available.
Additionally, browser-level integration currently only works with Chromium-based browsers, leaving Firefox and Opera out of the equation. Since Microsoft Edge is Chromium-based, this makes sense for Microsoft, but may not meet the requirements of all organizations.
For system administrators, the Enhanced Phishing Protection is configurable via Group Policy which facilitates organization-wide deployments.
These include settings such as whether or not to enable the feature, whether or not to notify a user of a malicious website, reuse a password, or detect an insecure app.
For those using Microsoft Endpoint Manager, add Enhanced Phishing Protection to your users with an appropriate profile and settings. Additionally, organizations using Microsoft 365 Defender view alerts in the Defender for Endpoint portal.
The other side of the coin: Specops password policy
Microsoft’s enhanced phishing protection is only part of the equation; keeping track of passwords and blocking weak passwords is the other side of actively protecting users and your organization.
With Specops password policyyou get a constantly updated list of breached/stolen passwords and powerful, customizable password policies.
Phishing attacks involving the loss of passwords make it possible to quickly infiltrate an organization. But, an organization with Enhanced Phishing Protection coupled with Specops password policy and List of broken passwords feature ensures the safety of your users.
By scanning your accounts against a constantly updated list of over 3 billion cracked passwords, when a stolen password is added to the list, you can act quickly and remove the potential vulnerability from your environment.
With Specops Authentication Client, when changing passwords, instantly let your users know why their password won’t work, especially if the password was stolen by a phishing scam sophisticated.
Specops Passwords offers more than breached password protection; many features exist to secure accounts and protect users from costly mistakes. Ensure your users are using secure passwords by auditing existing accounts and providing valuable feedback to ensure your users know exactly what is expected.
Some of the valuable features of Specops Password Policy:
- Use custom dictionary lists to add common words to your organization.
- Block usernames, display names, specific words, consecutive characters, incremental passwords, and reuse of part of the current password.
- Leverage granular GPO-based targeting for any organizational unit (OU), computer, user, or population group.
- Use regular expressions to further customize requirements.
- Use helpful end-user client messaging in case password changes fail.
Combine Microsoft’s enhanced phishing protection and Specops password policy to protect both your users and your environment. You can test the Specops password policy in your Active Directory for free, here.
Sponsored and written by Specops software
[ad_2]
Source link
