[ad_1]

The U.S. government today issued an alert about state-backed hackers who are using custom “CovalentStealer” malware and the Impacket framework to steal sensitive data from a U.S. Defense Industrial Base organization ( DIB).
The compromise lasted approximately ten months and it is likely that multiple Advanced Persistent Threat (APT) groups likely compromised the organization, some of them gaining initial access through the victim’s Microsoft Exchange server in January of the last year.
Entities in the defense industrial base sector provide products and services that enable the support and deployment of military operations.
They are engaged in the research, development, design, production, delivery and maintenance of military weapon systems, including all necessary components and parts.
ProxyLogon, RAT and Custom Malware
A joint report by the Cybersecurity and Infrastructure Agency (CISA), the Federal Bureau of Investigation (FBI), and the National Security Agency (NSA) provides technical details gathered during incident response activity that spanned between November 2021 and January 2022.
The hackers combined custom malware called CovalentStealer, the open source Impacket collection of Python classes, the HyperBro Remote Access Trojan (RAT), and well over a dozen ChinaChopper webshell samples.
They also exploited the ProxyLogon collection four vulnerabilities for Exchange Server when Microsoft released an emergency security update to fix them.
At the time, Microsoft detected the ProxyLogon exploit chain when the vulnerabilities were zero-day (unknown to the vendor), in attacks attributed to a Chinese state-sponsored hacking group they call Hafnium.
- CVE-2021-26855 is a server-side request forgery (SSRF) vulnerability in Exchange that allows sending arbitrary HTTP requests and authenticating as an Exchange server
- CVE-2021-26857 is an insecure deserialization vulnerability in the Unified Messaging service. Hafnium used it to run code as SYSTEM on Exchange Server
- CVE-2021-26858 is a post-authentication arbitrary file write vulnerability in Exchange. It could be exploited after compromising the credentials of a legitimate administrator.
- CVE-2021-27065 is a post-authentication arbitrary file write vulnerability in Exchange
Although the initial access vector is unknown, the current advisory indicates that hackers gained access to the organization’s Exchange server in mid-January 2022.
Within four hours, the threat actor ran mailbox searches and used a compromised administrator account belonging to a former employee to access the Exchange Web Services (EWS) API, which is used to send and receive web service messages from client applications.
Less than a month later, in early February 2021, the attackers again accessed the network using the same administrator credentials through a virtual private network (VPN) connection.
After four days, the hackers embarked on reconnaissance activity using a command shell. They learned about the victim’s environment and manually archived (WinRAR) sensitive data, such as contract-related information stored on shared drives, preparing it for exfiltration.
“These files have been split into approximately 3MB chunks located on the Microsoft Exchange Server in the CU2\he\debug directory » – joint report from the CISA, the FBI and the NSA
In early March, hackers exploited ProxyLogon vulnerabilities to install no less than 17 China Chopper webshells on the Exchange server.
China Chopper offers powerful capabilities in a very small package (only 4 kilobytes). It was first used by Chinese threat actors, but became so popular that other groups adopted it.
The activity to establish persistence on the network and move laterally began in April 2021 and was possible Impacket, which allows working with network protocols.
CISA says the attacker used Impacket with compromised credentials to obtain a service account with higher privileges, which allowed remote access from multiple external IP addresses to the Exchange server. organization via Outlook Web Access (OWA).
Access to the remote Exchange server was done through the services of two VPN and virtual private server providers, M247 and SurfShark, a common tactic to hide interaction with the victim network.
Buried deep in the victims’ network, the hackers relied on the custom CovalentStealer to upload additional sensitive files to a Microsoft OneDrive location between late July and mid-October 2022.
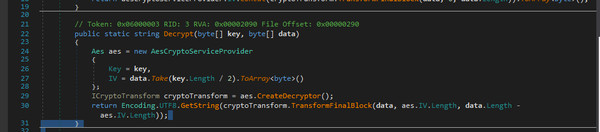
In a separate report, CISA provides technical analysis for CovalentStealer noting that the malware relies on code from two publicly available utilities, ClientUploader and the Export-MFT PowerShell script, to upload compressed files and extract the master file table (MFT) from a local storage volume.
CovalentStealer also contains resources for encrypting and decrypting downloaded data and configuration files, and for securing communications.
CISA-Shares technical details for the HyperBro RAT in a separate report, stating that the malware’s capabilities include downloading files to and from the system, logging keystrokes, executing commands on the infected host, and circumventing control protection. user account to run with full administrator privileges.
The US government does not currently provide any indication of the origin of the threat actors, but notes that “CISA has discovered that several APT groups have likely compromised the organization’s network”.
A set of recommendations are available in the joint report to detect persistent and long-term access threat activity, one of which is to monitor logs for connections from unusual VPS and VPNs.
Defenders should also examine connections from unexpected ranges and, for this particular attacker, verify machines hosted by SurfShark and M247.
Monitoring for suspicious account usage, such as improper or unauthorized use of administrator accounts, service accounts, or third-party accounts, is also on the list.
Using compromised credentials with a VPS can also indicate a potential breach that could be discovered by:
- Examination of logs for “unable to connect”, e.g. connections with changing username, user agent strings and IP address combinations or connections where IP addresses do not match location geographical location of the expected user
- Finding “travel impossible”, which occurs when a user connects from multiple geographically distant IP addresses. False positives can result when legitimate users connect through a VPN
- Searching for an IP address used on multiple accounts, excluding expected logins (successful remote logins from M247 and SurfShark IP addresses may be a red flag)
- Identifying suspicious use of privileged accounts after resetting passwords or applying user account mitigations
- Finding unusual activity in generally inactive accounts
- Check for unusual user agent strings, such as strings that are not typically associated with normal user activity, which may indicate bot activity
Gasket CISA, FBI and NSA report shares a set of YARA rules created to detect the activity of this particular threat actor and indicators of compromise for the tools used in the attack: CovalentStealer, HyperBrotherand China chopper.
[ad_2]
Source link
