[ad_1]
Microsoft blocked code-signing certificates primarily used by Chinese hackers and developers to sign and load malicious kernel-mode drivers on hacked systems by exploiting a Windows policy loophole.
Kernel-mode drivers operate at the highest privilege level on Windows (Ring 0), allowing full access to the target machine for stealth persistence, undetectable data exfiltration, and the ability to terminate almost any process.
Even if security tools are active on the compromised device, a kernel-mode driver can interfere with their operation, disable their advanced protection capabilities, or make targeted configuration changes to evade detection.
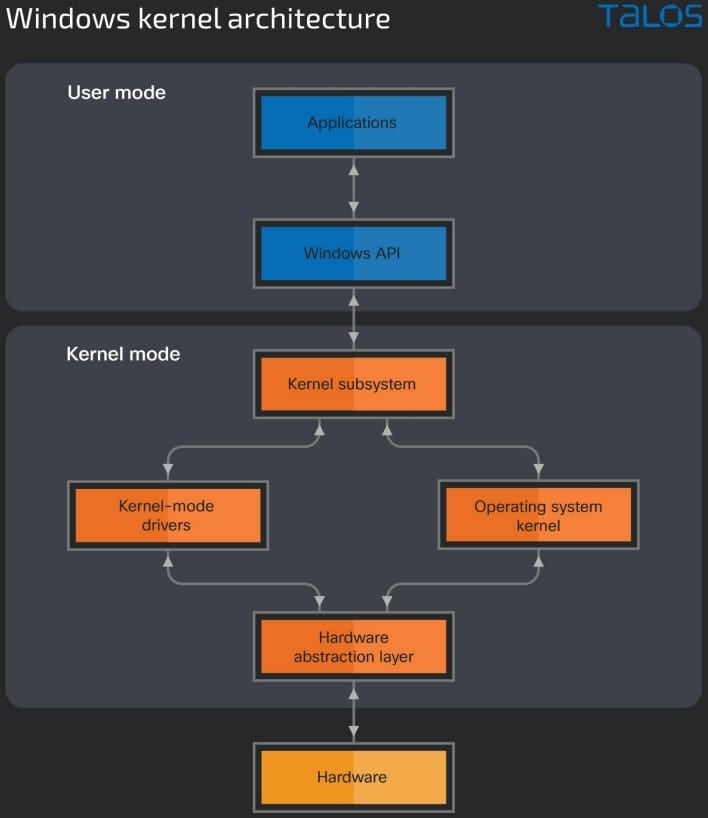
With Windows Vista, Microsoft introduced policy changes limiting how Windows kernel-mode drivers could be loaded into the operating system, requiring developers to submit their drivers for review and sign them through the Windows Developer Portal. Microsoft.
However, to avoid issues with older applications, Microsoft introduced the following exceptions that allowed older kernel-mode drivers to continue to be loaded:
- The PC was upgraded from an earlier version of Windows to Windows 10, version 1607.
- Secure Boot is disabled in the BIOS.
- The drivers were [sic] signed with an end-entity certificate issued before July 29, 2015 that is bound to a supported cross-signature CA
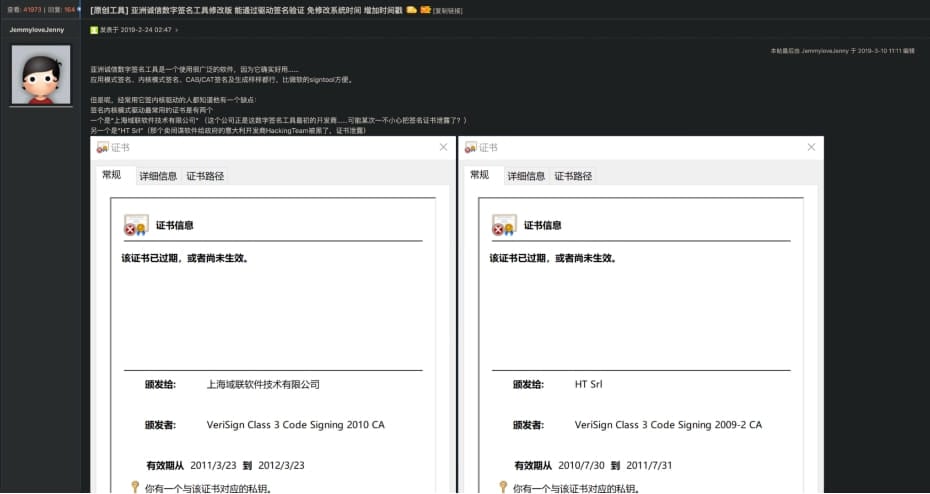
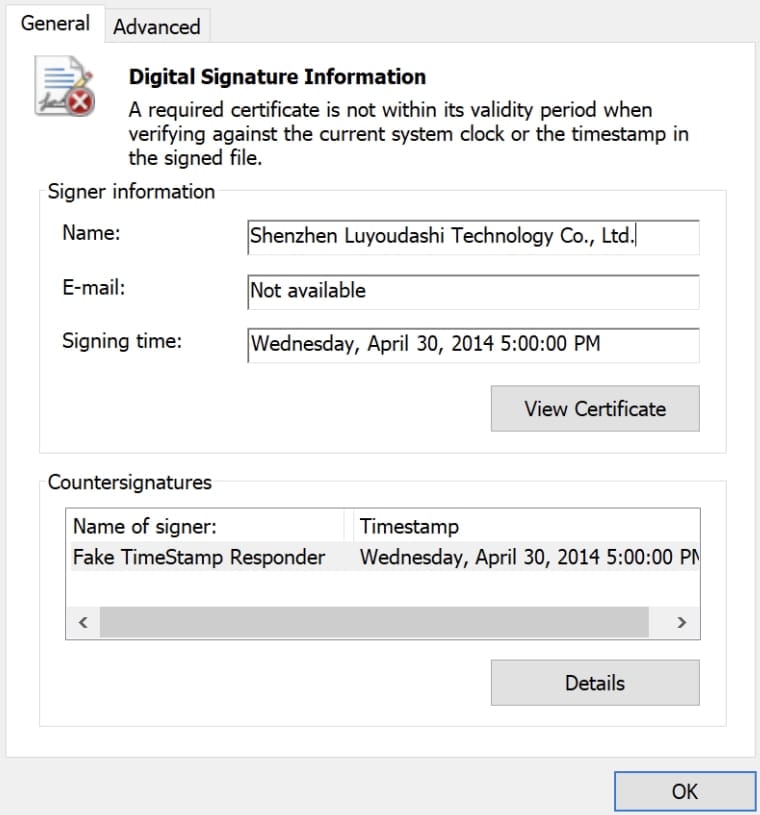
A new report by Cisco Talos explains that Chinese hackers exploit the third policy by using two open source tools, “HookSignTool” and “FuckCertVerify”, to change the signature date of malicious drivers before July 29, 2015.
By changing the signing date, threat actors can use older, leaked, and unrevoked certificates to sign their drivers and load them into Windows for elevation of privilege.
HookSignTool and FuckCertVerify
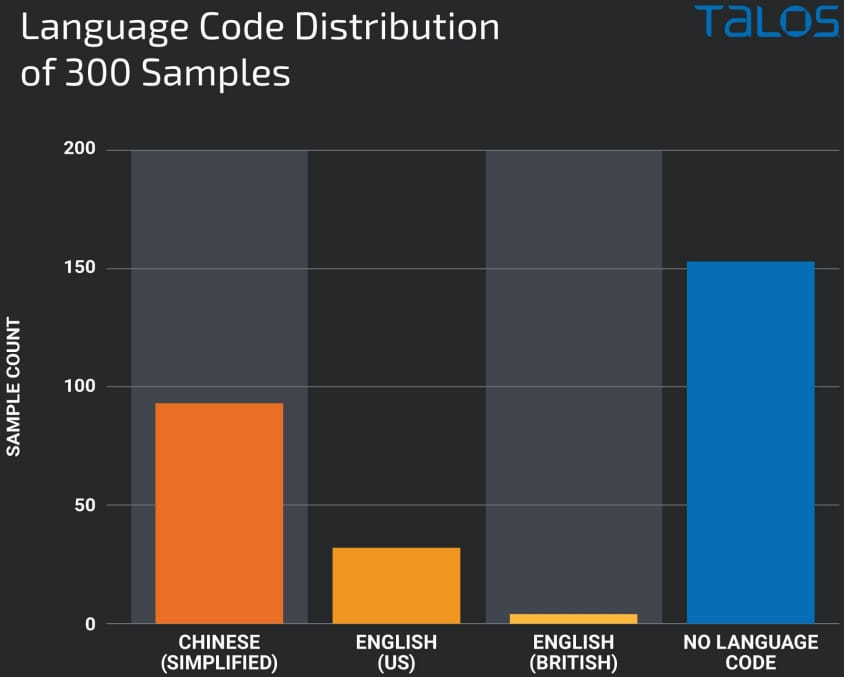
HookSignTool is a feature-rich tool released in 2019 on a Chinese software hacking forum, using the Windows API with a legitimate code signing tool to perform malicious driver signing.
The tool uses the Microsoft Detours library to intercept and monitor Win32 API calls and a custom implementation of the “CertVerifyTimeValidity” function named “NewCertVerifyTimeValidity”, which checks for invalid times.
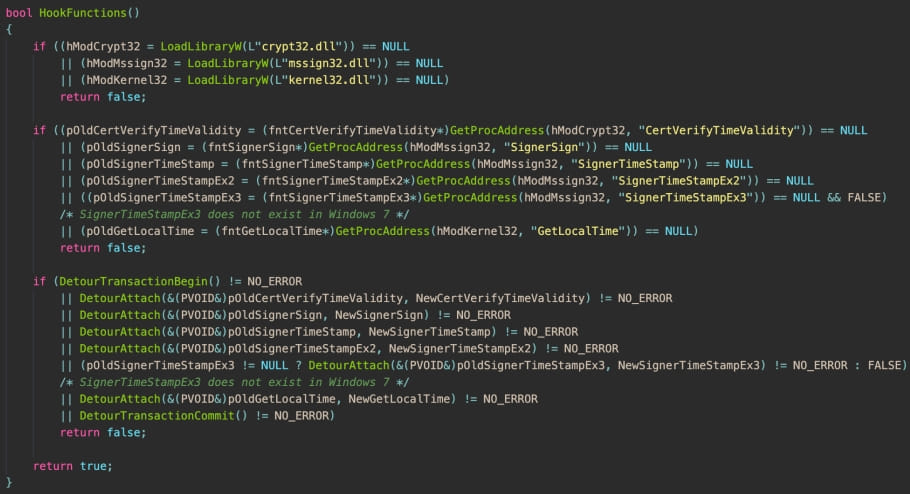
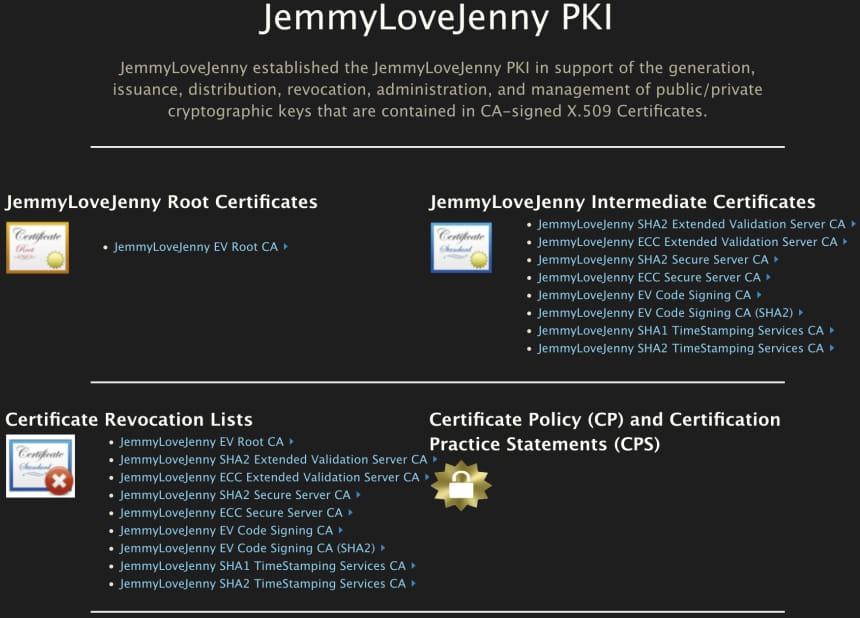
HackSignTool requires the presence of the “JemmyLoveJenny EV Root CA certificate” to sign driver files with a backdated timestamp, which is available on the tool author’s website.
However, using this certificate leaves artifacts in the forged signature, which helps identify drivers signed with HookSignTool.
In a separate report also published today, Cisco Talos details a real-life example of a malicious driver called “RedDriver”, signed using HookSignTool.
RedDriver is a browser hijacker that intercepts browser traffic, targeting Chrome, Edge, and Firefox, as well as a long list of popular browsers in China.
FuckCertVerify is another tool used by threat actors to modify the signature timestamps of malicious kernel-mode drivers, originally made available on GitHub in December 2018 as a game cheat tool.
“FuckCertVerifyTimeValidity works similarly to HookSignTool in that it uses the Microsoft Detours package to hook into the ‘CertVerifyTimeValidity’ API call and sets the timestamp to a chosen date,” Cisco Talos explains.
“[But] Unlike HookSignTool, FuckCertVerifyTimeValidity does not leave artifacts in the binary it signs, which makes it very difficult to identify when this tool was used.”
Both tools require an unrevoked code-signing certificate issued before July 29, 2015, when Microsoft introduced the policy change, and the corresponding private key and password.
Cisco researchers have found more than a dozen certificates in GitHub repositories and Chinese language forums that can be used by these tools, which are widely used for game cracks that can bypass DRM checks and kernel drivers malicious.
Microsoft revokes certificates
In a related advisory released today, Microsoft says Sophos and Trend Micro also reported this malicious activity.
After being responsibly disclosed, Microsoft revoked associated certificates and suspended developer accounts by abusing this Windows policy flaw.
“Microsoft has released security updates to Windows (see Security Updates table) that no longer trusts drivers and driver signing certificates for affected files and has suspended partner seller accounts” , explains the Microsoft Reviews.
“Additionally, Microsoft has implemented blocking detections (Microsoft Defender 1.391.3822.0 and later) to help protect customers against legitimately signed drivers that have been maliciously used in post-exploit activity.”
“For more information on how the Windows Code Integrity feature protects Microsoft customers against revoked certificates, see: Windows Driver.STL Revocation List Notice.”
Cisco Talos told BleepingComputer that Microsoft did not assign a CVE to this abuse because the company does not classify it as a vulnerability.
In a report also released today, Sophos said they found over a hundred malicious kernel drivers used as “EDR Killers” to terminate security software usually protected from user-mode programs.
As these drivers provide kernel privileges, they can be used to stop any software, including anti-virus protected processes.
Microsoft has also revoked these drivers as part of its Windows Driver.STL CRL update.
While the certificates discovered by Cisco and Sophos have now been revoked, the risk is far from eliminated as other certificates likely remain exposed or stolen, allowing threat actors to continue to abuse this Windows policy flaw. .
Update 7/11/23: Added information from Sophos.
[ad_2]
Source link
