[ad_1]

An APT hacking group known as “Dragon Breath”, “Golden Eye Dog”, or “APT-Q-27” demonstrates a new trend of using several complex variations of the classic DLL sideloading technique to evade detection.
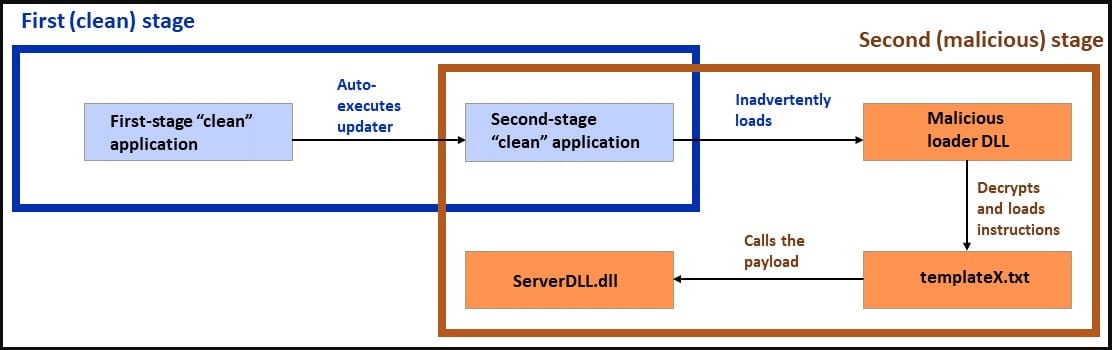
These attack variants start with an initial vector that leverages a clean application, most often Telegram, which loads a second stage payload, sometimes also clean, which in turn loads a malicious malware loader DLL.
The bait for the victims is Trojan Telegram, LetsVPN or WhatsApp apps for Android, iOS or Windows that have supposedly been localized for people in China. Trojanized apps are believed to be promoted using BlackSEO or malvertising.
According Sophos analysts following the threat actor’s recent attacks, the scope of this campaign is focused on Chinese-speaking Windows users in China, Japan, Taiwan, Singapore, Hong Kong and the Philippines.
Double sideloading of DLLs
DLL sideloading is a technique exploited by attackers since 2010, taking advantage of the insecure way Windows loads DLL (Dynamic Link Library) files required by an application.
The attacker places a malicious DLL with the same name as the legitimate required DLL in an application’s directory. When the user launches the executable, Windows prioritizes the local malicious DLL over the one in the system folders.
The attacker’s DLL contains malicious code which loads at this point, giving the attacker privileges or executing commands on the host by exploiting the trusted and signed application loading it.
In this campaign, victims run the installer of the mentioned applications, which drops components on the system and creates a desktop shortcut and a system startup entry.
If the victim attempts to launch the newly created desktop shortcut, which is the expected first step, instead of launching the application, the following command is executed on the system.
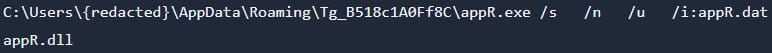
The command runs a renamed version of ‘regsvr32.exe’ (‘appR.exe’) to run a renamed version of ‘scrobj.dll’ (‘appR.dll’) and provides a DAT file (‘appR.dat’) as contribution to it. The DAT contains JavaScript code to be executed by the script execution engine library (‘appR.dll’).
The JavaScript code launches the Telegram app UI in the foreground while installing various sideloading components in the background.
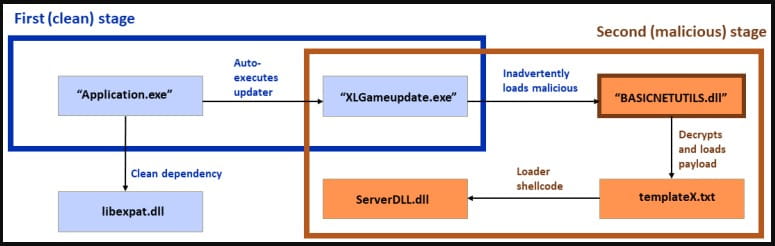
Then the installer loads a second stage application using a clean dependency (‘libexpat.dll’) to load a second clean application as an intermediate attack stage.
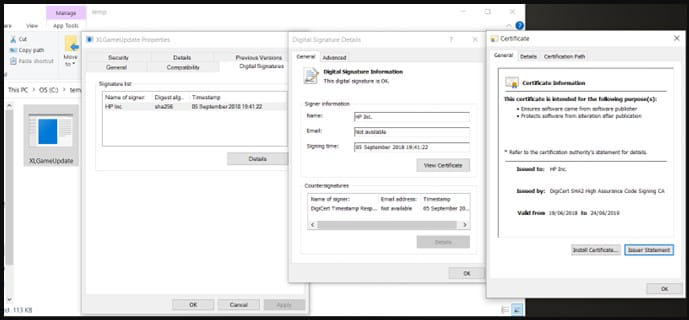
In a variant of the attack, the own application “XLGame.exe” is renamed “Application.exe”, and the second stage loader is also an own executable, signed by Beijing Baidu Netcom Science and Technology Co., Ltd.
In another variant, the clean second-stage loader is “KingdomTwoCrowns.exe”, which is not digitally signed, and Sophos has not been able to determine what benefit it offers besides obfuscating the execution chain.
In a third variant of the attack, the second-stage loader is the own executable “d3dim9.exe”, digitally signed by HP Inc.
This “double DLL sideloading” technique enables evasion, obfuscation, and persistence, making it harder for defenders to adapt to specific attack patterns and effectively protect their networks.
The final payload
In all observed attack variants, the final payload DLL is decrypted from a txt file (‘templateX.txt’) and executed on the system.
This payload is a backdoor that supports multiple commands, such as system reboot, registry key modification, file recovery, stealing clipboard contents, running commands on a hidden CMD window, etc.
The backdoor also targets the Chrome extension of the MetaMask cryptocurrency wallet, aiming to steal victims’ digital assets.
In summary, sideloading DLLs remains an effective attack method for hackers and one that Microsoft and developers have failed to solve for over a decade.
In the latest APT-Q-27 attack, analysts observed hard-to-track DLL side-loading variations; therefore, they achieve a stealthier chain of infection.
[ad_2]
Source link
