[ad_1]

GitHub now automatically blocks the leak of sensitive information such as API keys and access tokens for all public code repositories.
Today’s announcement comes after the company introduction of thrust protection in beta over a year ago, in April 2022.
This feature proactively prevents leaks by scanning secrets before “git push” operations are accepted, and it works with 69 types of tokens (API keys, private keys, secret keys, authentication tokens, access tokens, management certificates, credentials, etc.) detectable with a low “false positive” detection rate.
“If you push a commit containing a secret, a push protection prompt will appear with information about the type of secret, location, and how to remediate the exposure”, GitHub said Today.
“Push protection only blocks secrets with a low false positive rate, so when a commit is blocked, you know it’s worth investigating.”
Since its beta release, software developers who enabled it have managed to prevent approximately 17,000 accidental exposures of sensitive information, saving more than 95,000 hours that would have been spent revoking, rotating and patching compromised secrets, according to GitHub.
Whereas before today this feature could only be enabled for private repositories by organizations with a GitHub Advanced Security license, GitHub has now also made it generally available on all public repositories.
“Today, push protection is generally available for private repositories with a GitHub Advanced Security (GHAS) license,” the company said.
“Additionally, to help developers and maintainers across open source proactively secure their code, GitHub is making push protection free for all public repositories.”
How to enable secret scan push protection
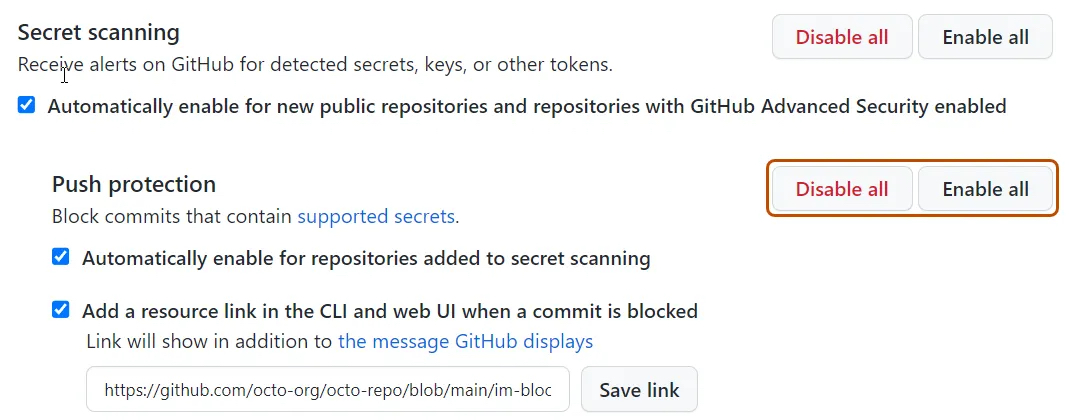
Organizations with GitHub Advanced Security can enable secret scan push protection at the repository and organization level through the API or with a single click from the UI.
The step-by-step procedure for enabling push protection for your organization requires that you:
- On GitHub.com, go to the organization’s main page.
- Under your organization name, click Settings.
- In the “Security” section of the sidebar, click Security and code analysis.
- Under “Configure security and code analysis”, look for “GitHub Advanced Security”.
- Under “Secret Scan”, click Activate all next to “Push protection”.
- If desired, click “Automatically enable for private repositories added to secret scan”.
It can also be enabled for single repositories by toggling it from the Settings > Security & Analytics > GitHub Advanced Security dialog for each repository.
More details on using push protection from the command line or allowing certain secrets to be pushed can be found at GitHub documentation site.
Exposed credentials and secrets have led to high-impact breaches in recent years, as BleepingComputer previously reported. [1, 2, 3].
Therefore, enabling push protection for private repositories or for free on public repositories to ensure code pushes are automatically blocked if they contain secrets is an easy way to defend against accidental leaks with potentially massive impacts. .
[ad_2]
Source link
