[ad_1]

The “FakeCalls” Android malware is once again circulating in South Korea, mimicking phone calls from more than 20 financial organizations and attempting to trick bankers into divulging their credit card details.
The particular malware is not new, as Kaspersky published a report about it one year ago. However, Check Point researchers are now reporting that newer versions have implemented several evasion mechanisms not seen in previous samples.
“We discovered over 2500 samples of the FakeCalls malware that used a variety of combinations of impersonated financial organizations and implemented anti-analysis techniques,” it reads. The CheckPoint report.
“Malware developers have paid special attention to protecting their malware, using several unique evasions that we have yet to see in the wild.”
Voice Phishing
The first stage of the attack is to install malware on the victim’s device, which can happen via phishing, black listing, or malicious advertising.
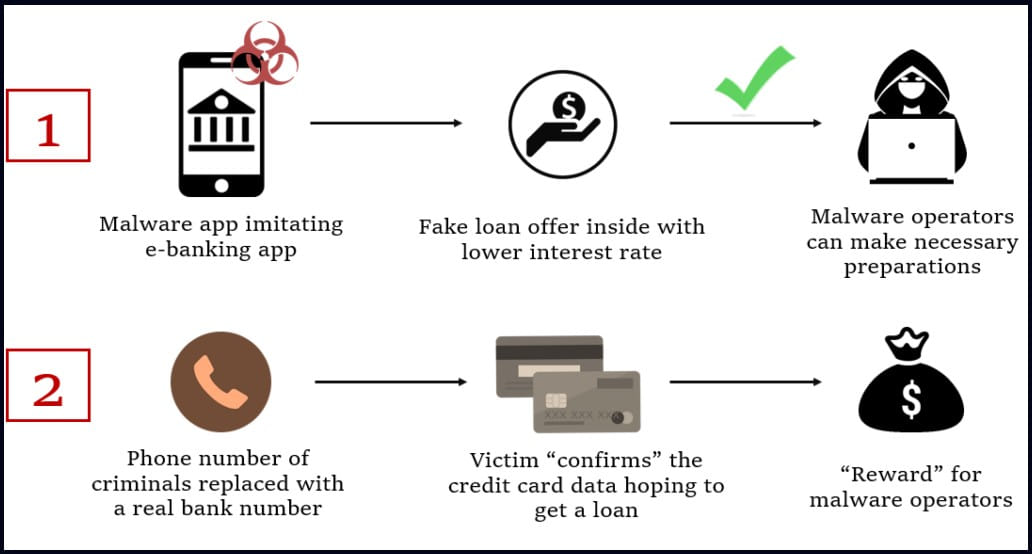
The FakeCalls malware is distributed on fake banking apps that impersonate major financial institutions in Korea, so victims think they are using a legitimate app from a trustworthy provider.
The attack begins with the app offering the target a low-interest loan. Once the victim is interested, the malware initiates a phone call that plays a recording of the bank’s real customer support with instructions to get the loan application approved.
However, the malware can hide the called number, which belongs to the attackers, and display the real number of the spoofed bank instead, making the conversation realistic.
At some point, the victim is tricked into confirming their credit card details, supposedly needed to receive the loan, which are then stolen by the attackers.
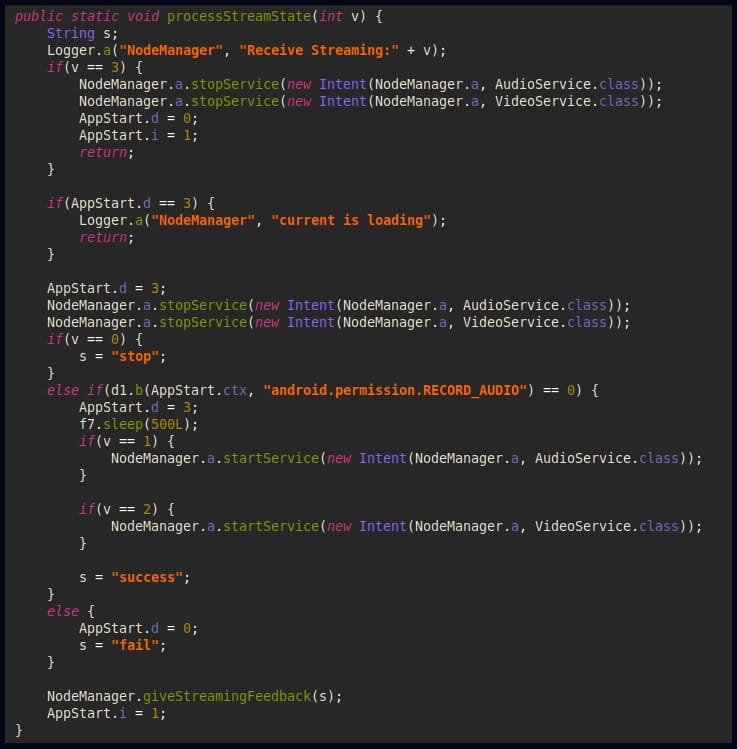
In addition to the vishing process, FakeCalls can capture live audio and video streams from the compromised device, which could help attackers gather additional information.
Avoid detection
In the latest samples captured and analyzed by CheckPoint researchers, FakeCalls incorporates three new techniques that help it evade detection.
The first mechanism is called “cross-disk”, which consists in manipulating the ZIP header data of the APK file (Android package), by setting abnormally high values for the EOCD record in order to confuse the analysis tools automated.
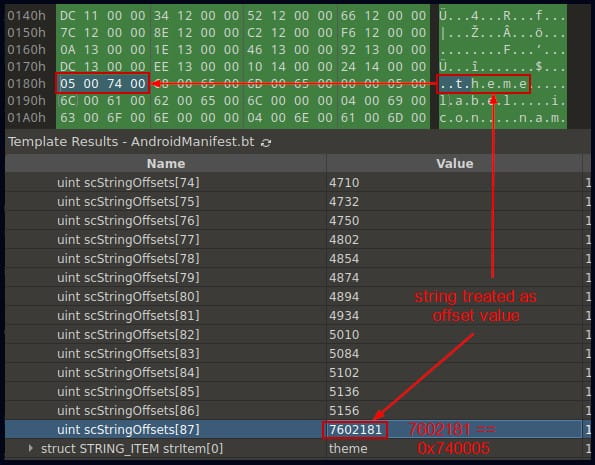
The second evasion technique involves manipulating the AndroidManifest.xml file to make its starting marker indistinguishable, modifying the structure of strings and styles, and altering the offset of the last string to cause incorrect interpretation.
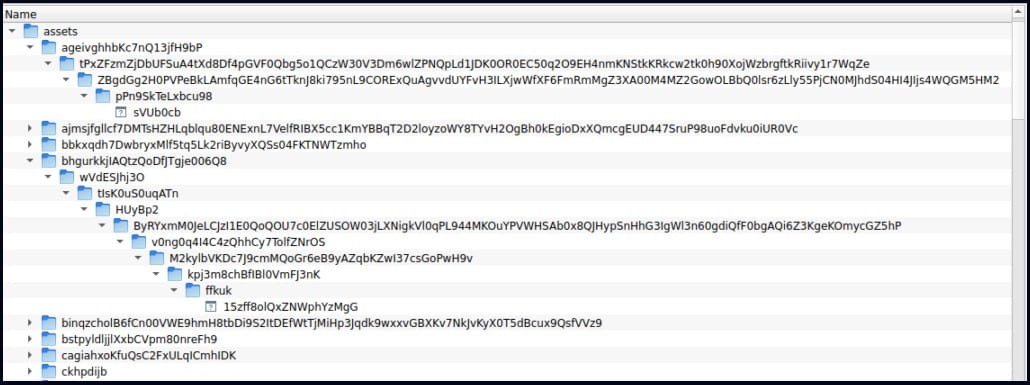
Finally, the third evasion method is to add many files in nested directories in the APK’s assets folder, resulting in filenames and paths exceeding 300 characters. Check Point says this can cause some security tools to fail, preventing them from detecting the malware.
A costly problem
According to the South Korean government Statisticsvishing is a problem that cost victims nationwide $600 million in 2020 alone, while there were 170,000 reported victims between 2016 and 2020.
While FakeCalls has remained in South Korea, the malware could easily expand its operations to other regions if its developers or affiliates develop a new language kit and app overlay to target banks in different countries.
Vishing has always been a serious problem, but the rise of machine learning speech models capable of generating natural speech and mimicking the voice of real people with minimal training data is about to take hold. amplify the threat shortly.
[ad_2]
Source link
