[ad_1]

Horizon3 security researchers have released proof-of-concept (PoC) exploit code for a remote code execution (RCE) bug in the managed file transfer (MFT) solution MOVEit Transfer abused by the Clop ransomware gang in data theft attacks.
This critical defect (monitored as CVE-2023-34362) is an SQL injection vulnerability that allows unauthenticated attackers to access unpatched MOVEit servers and execute arbitrary code remotely.
May 31, days after the Clop ransomware gang started exploiting it on a large scale like a zero dayProgress released security updates to fix the bug and advised all customers to apply them immediately to block exploit attempts.
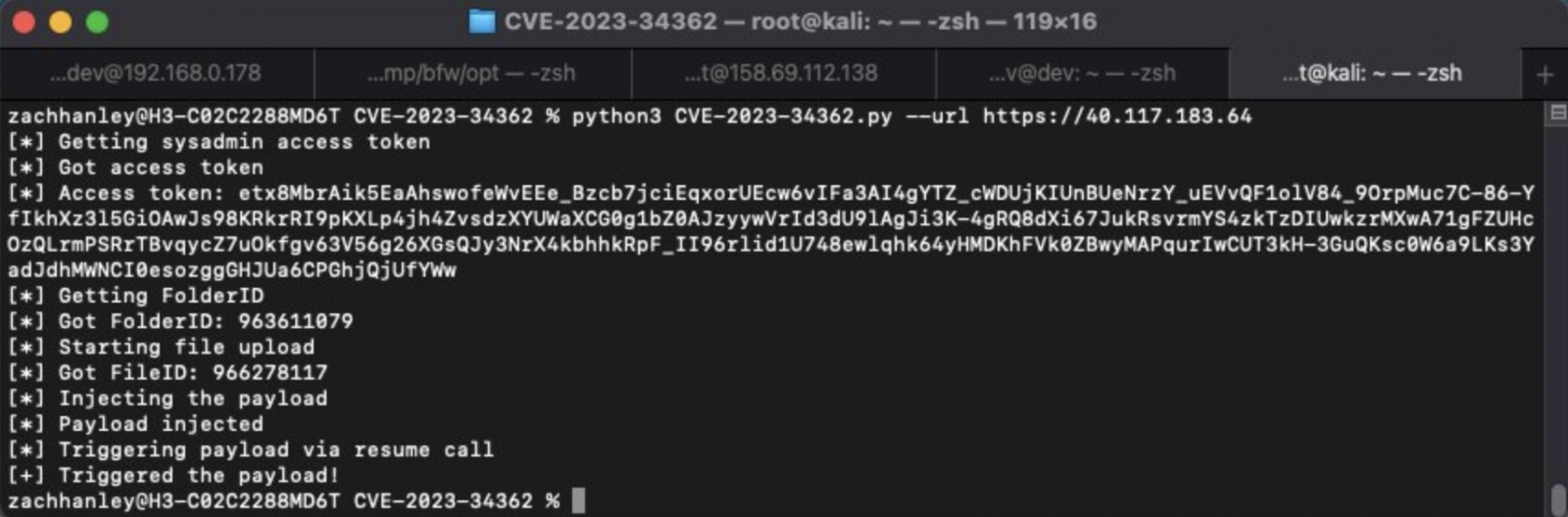
Horizon3 has released a proof-of-concept (PoC) exploit and technical analysis of the vulnerability Fridayas well as a list of Indicators of Compromise (IOC) that network defenders could use to detect exploitation on vulnerable servers.
“This POC abuses an SQL injection to obtain a sysadmin API access token, then uses that access to abuse a deserialization call to obtain remote code execution,” the authors said. Horizon3 researchers. explain.
“This POC must reach an identity provider endpoint that hosts the appropriate RS256 certificates used to forge arbitrary user tokens – by default, this POC uses our IDP endpoint hosted in AWS.”
With the release of this RCE PoC exploit, more malicious actors are likely to rapidly deploy it in attacks or create their own custom versions to target any unpatched servers left exposed to internet access.
However, given the widespread media coverage of attacks exploiting the vulnerability, it is expected that the number of insecure MOVEit Transfer servers on the Internet has dropped sharply since Clop began exploiting the bug.
Zero-day in the hands of Clop since 2021
The Clop ransomware gang claimed responsibility for data theft attacks exploiting CVE-2023-34362 MOVEit Transfer zero-day in a message sent to Bleepingomputer, attacks that allegedly affected “hundreds of businesses”.
Clop was also linked to the attacks by Microsoftwho attributed this data theft campaign to the Lace Tempest hacking group, which overlaps FIN11 and TA505 activities.
According to a Kroll report, evidence suggests that Clop actively sought opportunities to exploit the patched MOVEit zero-day vulnerability since 2021. They are also researching methods to extract data from compromised MOVEit servers since at least April 2022.
The list of organizations that have disclosed data breaches following these attacks includes, among others, the British multinational EY, the Irish Director of Health Services (HSE) public health system, UK provider of payroll and human resources solutions Zellis and some of its customers (i.e. British airline British Airways, Irish airline Aer Lingus and the Minnesota Department of Education).
Known for its history of orchestrating data theft campaigns, this cybercrime group has targeted vulnerabilities in several managed file transfer platforms over the past few years.
Notable cases include the zero-day violation of Accellion FTA Servers in December 2020, the 2021 SolarWinds Serv-U Managed file transfer attacks and the exploitation of a GoAnywhere MFT zero-day during widespread attacks in January 2023.
Friday, progress patched and warned newly discovered critical SQL injection vulnerabilities in MOVEit Transfer allowing unauthenticated attackers to steal information from customer databases.
[ad_2]
Source link
