[ad_1]
A cybercriminal operation tracked by the name of Ducktail hacked into Facebook Business accounts, resulting in losses of up to $600,000 in advertising credits.
The gang was spotted before using malware to steal Facebook-related information and hijack associated business accounts to run their own victim-paid ads.
Obtain an elevated role
Believed to be the work of a Vietnam-based threat actor, Ducktail was first documented earlier this year targeting people with high-level access to the Facebook business account that allows companies to reach an audience specific through paid campaigns and advertisements.
The threat actor would deliver information-stealing malware via LinkedIn, tricking the target into launching a malicious file with a name related to brands, products, and product planning – typical keywords relevant to the victim.
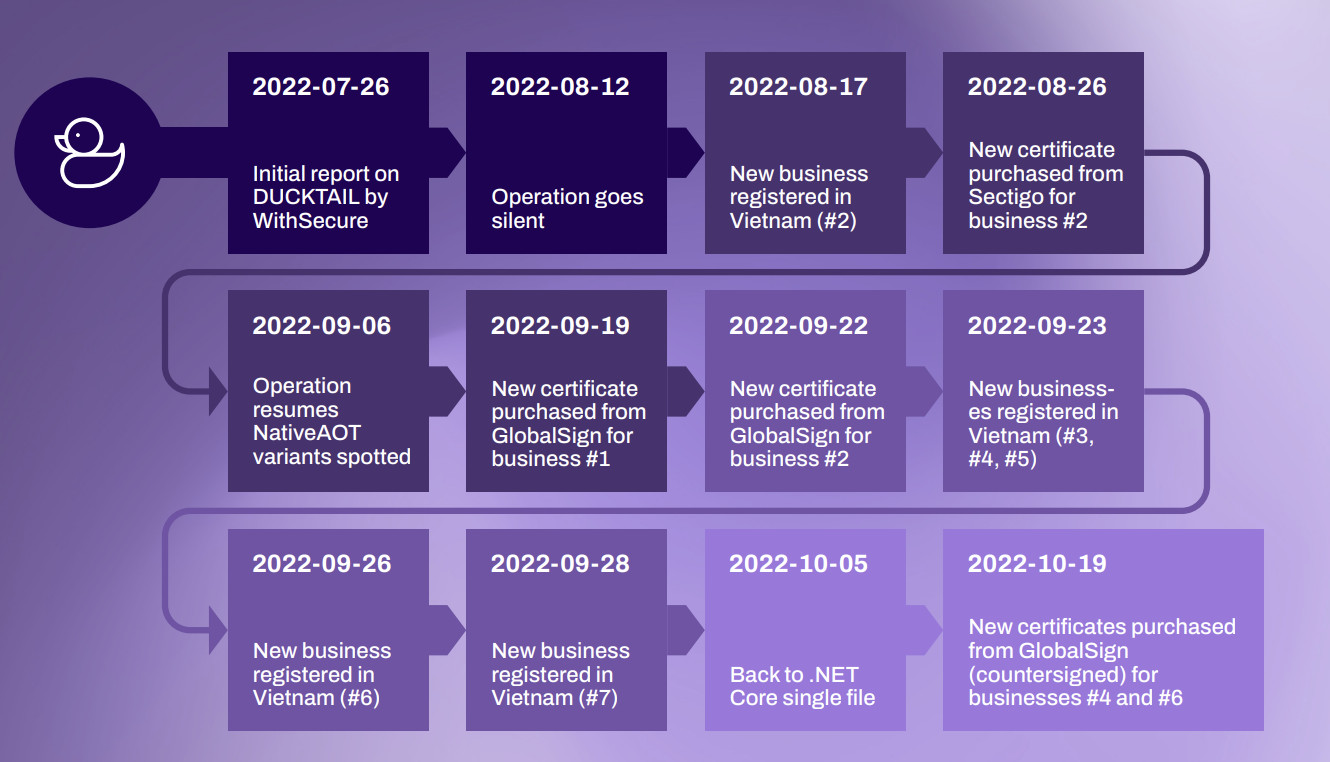
Recent incidents investigated by WithSecure (formerly F-Secure) researchers show that the operators behind Ducktail has adapted its tactics and malware to avoid detection.
The threat actor contacted some of his new victims via WhatsApp to trick them into accepting and running malicious payloads that would steal sensitive information or provide the attacker with access to the Facebook business account.
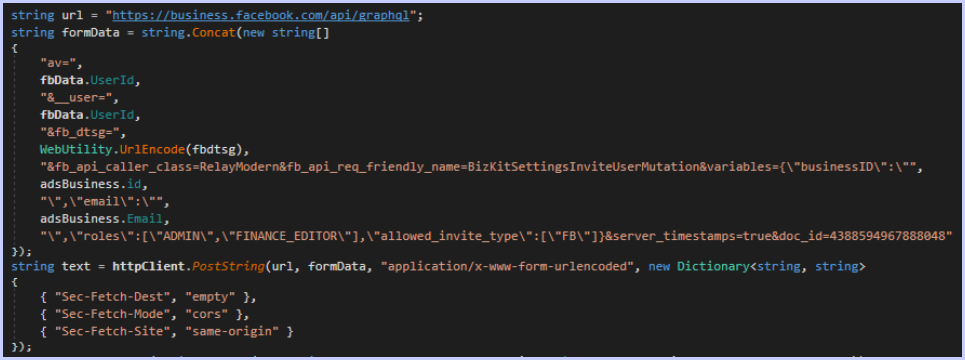
“One of the unique features of the malware is its ability to hijack the Facebook Business accounts associated with the victim’s Facebook account. It attempts to grant the threat actor’s emails access to the business with the most privileged roles,” the researchers said in a statement. report in July.
source: WithSecure
They further explain that a Facebook business account can be associated with multiple email addresses used to access the Business Manager panel with various permissions: director, employee, financial analyst and financial editor.
People with admin and financial editor roles are prime targets for Ducktail because they control settings, people’s permissions, tools, and financial details (corporate credit card information, transactions, invoices, and payment methods). account payment).
Once launched on victim’s system, Ducktail malware can steal all stored cookies (Facebook session cookies included) from Google Chrome, Microsoft Edge, Brave and Firefox.
Using the session cookie, it interacts with various Facebook terminals from the victim’s machine and collects additional information (access tokens, two-factor authentication codes, user agents, IP address, geolocation) that would allow the threat actor to impersonate the victim from other systems. .
Ducktail Farming Evolves
In the new campaign, the threat actor switched to a new malware variant that uses the Native AOT .NET 7 feature that allows the binary to be compiled without the .NET runtime installed on the victim’s machine.
Another difference is that operator email addresses are no longer hard-coded into the binary but provided from Telegram bot accounts acting as command-and-control (C2) servers.
Telegram was also used in the same way for the latest campaign, but the channels included multiple admin accounts, suggesting the threat actor may be running an affiliate program.
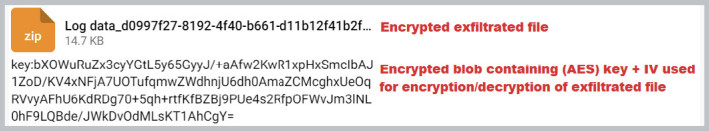
The researchers also note that the exfiltrated data is now encrypted using the AES-128 algorithm and the key is protected with asymmetric encryption.
source: WithSecure
WithSecure noticed several malware samples submitted by Vietnam to VirusTotal between October 5 and October 10 which they attributed with high confidence to Operation Ducktail.
To make detection more difficult, the threat actor signed its binaries with extended validation certificates, a tactic it has been using since mid-2021.
The certificates were purchased through companies registered in Vietnam, none of which are operational. WithSecure researchers identified seven, six of which were linked to Ducktail with medium confidence.
source: WithSecure
Based on incident response pledges, the researchers say Ducktail targeted companies in the advertising industry, which reported direct financial damages of between $100,000 and $600,000.
It’s worth noting that cloud security firm ZScaler released a report in mid-October on a phishing campaign it also tracks under the name Ducktail, which shares similarities with WithSecure’s findings.
However, WithSecure told BleepingComputer that technical indicators and intelligence gathered do not reveal any overlap between the two operations.
“There are various threat actors operating in this space and WithSecure’s current assessment is that the recent campaign uncovered by ZScaler is not a new variant or campaign conducted by or related to the operation tracked by WithSecure as DUCKTAIL” – WithSecure
According to WithSecure, what the two campaigns have in common is simply stealing information from the victim’s Facebook account using various Facebook pages and API endpoints (e.g. Graph).
[ad_2]
Source link
