[ad_1]

Sports betting company DraftKings revealed last week that more than 67,000 customers had their personal information exposed following a id attack in november.
In credential stuffing attacks, automated tools are used to make massive numbers of attempts (up to millions at a time) to log into accounts using credentials (user/password pairs). password) stolen from other online services.
This tactic works exceptionally well against user accounts whose owners have reused the same login credentials across multiple platforms.
The attackers aim to take control of as many accounts as possible to steal personal and financial information, which is sold on hacking forums or on the dark web. However, stolen information can also be used in identity theft scams to make unauthorized purchases or drain bank accounts linked to compromised accounts.
Nearly 68,000 DraftKings customers affected
In a data breach notification filed with the senior attorney general’s office, DraftKings revealed that the data of 67,995 people was exposed in the incident last month.
The company said the attackers obtained the credentials needed to log into customer accounts from a source other than DraftKings.
“In the event of access to an account, among other things, the attacker could have seen the name, address, telephone number, email address of the account holder, the last four digits of the card payment card, profile picture, previous transaction information, account balance, and last password change date,” the breach notification reads.
“At this time, there is currently no evidence that attackers have accessed your social security number, driver’s license number, or financial account number.
“While bad actors may have seen the last four digits of your payment card, your full payment card number, expiration date, and CVV are not stored in your account.”
After detecting the attack, DraftKings reset passwords for affected accounts and said it had additional fraud alerts in place.
It also restored funds withdrawn following the credential attack, reimbursing up to $300,000 identified as stolen in the incident, as stated by DraftKings president and co-founder Paul Liberman. , in November.
Bank accounts of hacked DraftKings users targeted in attack
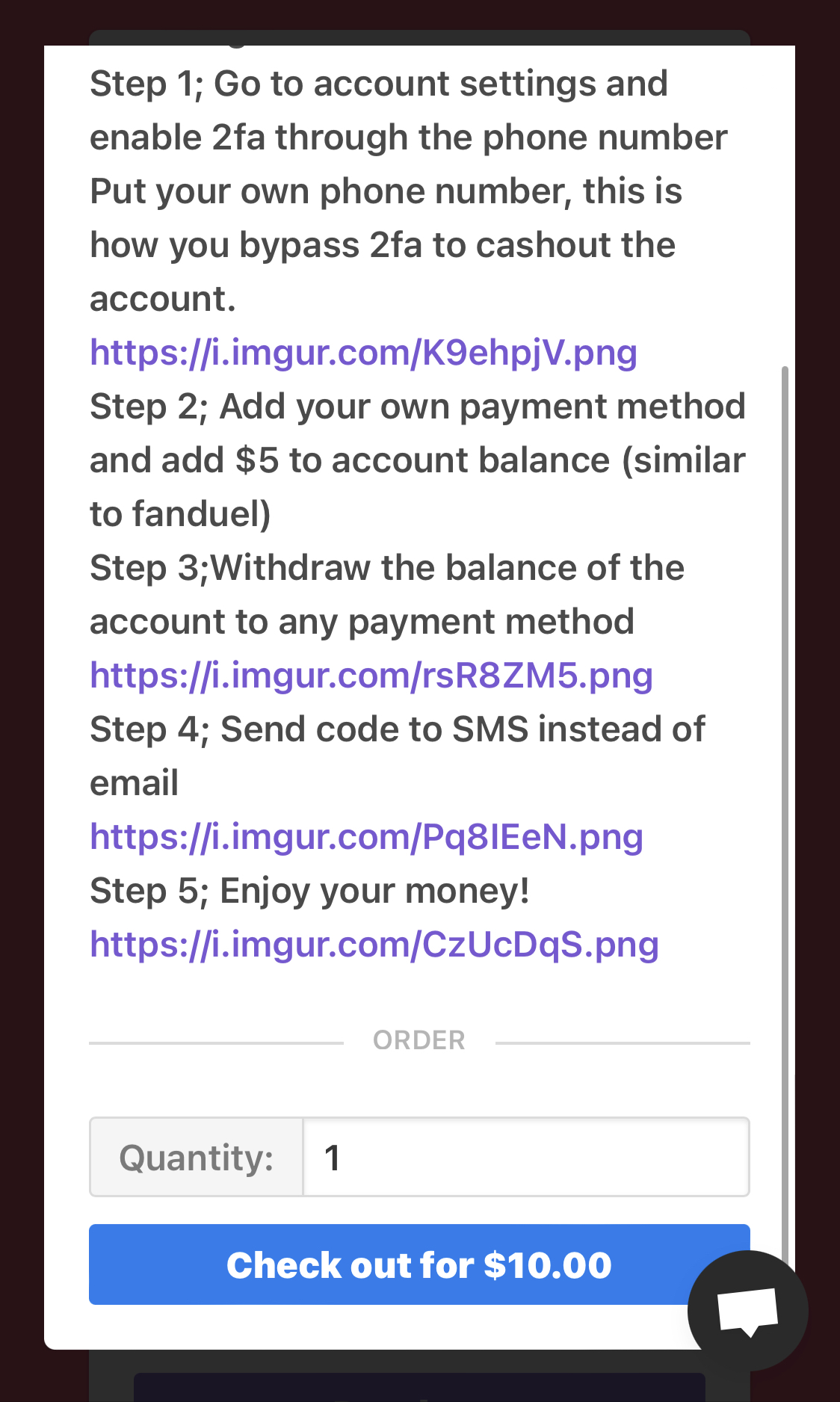
The common denominator of user accounts that have been hacked appears to be an initial deposit of $5 followed by a password change, enabling two-factor authentication (2FA) on a different phone number, then withdrawing as much as possible of the linked bank accounts of the victims.
Although DraftKings did not share additional information on how the attackers stole funds, BleepingComputer has since learned that the attack was carried out by a malicious actor selling stolen accounts with deposit balances on a marketplace. online for $10 to $35.
The sales included instructions on how buyers could make $5 deposits and withdraw all money from hacked DraftKings user accounts.
After DraftKings announced the credential stuffing attack, they locked down the hacked accounts, with threat actors warning that their campaign was no longer working.
The company now advises its customers to never use the same password for multiple online services, never share their credentials with third-party platforms, immediately enable 2FA on their accounts, and remove banking details or unlink their bank accounts to block any future fraudulent withdrawals. requests.
As the The FBI recently warnedCredential stuffing attacks are rapidly increasing in volume due to readily available automated tools and aggregate lists of leaked credentials.
In September, identity and access management company Okta also reported that the situation has worsened significantly this year since it recorded more than 10 billion credential stuffing events in the first three months of 2022.
This represents approximately 34% of the overall authentication traffic tracked by Okta, which means that one in three login attempts is malicious and fraudulent.
[ad_2]
Source link
