[ad_1]
The Clop ransomware gang has begun extorting companies whose data has been stolen using a zero-day vulnerability in the Fortra GoAnywhere MFT secure file sharing solution.
In February, the developers of file transfer solution GoAnywhere MFT warned customers of a zero-day remote code execution vulnerability. be operated on exposed admin consoles.
GoAnywhere is a secure web-based file transfer solution that allows businesses to securely transfer encrypted files with their partners while maintaining detailed audit logs of who accessed the files.
While no details have been shared publicly on how the vulnerability was exploited, a proof-of-concept exploit released soonfollowed by patch for the rift.
The day after the GoAnywhere patch was released, the Clop ransomware gang contacted BleepingComputer and claimed responsibility for the attacks.
The extortion group said they used the loophole for ten days to steal data from 130 companies. At the time, BleepingComputer could not independently confirm these claims and Fortra did not respond to our emails.
Since then, two companies, Community Health Systems (CHS) And hatch bankrevealed that data was stolen during the GoAnywhere MFT attacks.
Clop begins extorting GoAnywhere customers
Last night, the Clop ransomware gang began publicly exploiting victims of GoAnywhere attacks by adding seven new companies to their data leak site.
Only one of the victims, Hatch Bank, is publicly known to have been breached using the vulnerability. However, BleepingComputer has learned that at least two other publicly traded companies also had their data stolen using this flaw.
Entries on the data leak site all state that the data release is “coming soon”, but include screenshots of allegedly stolen data.
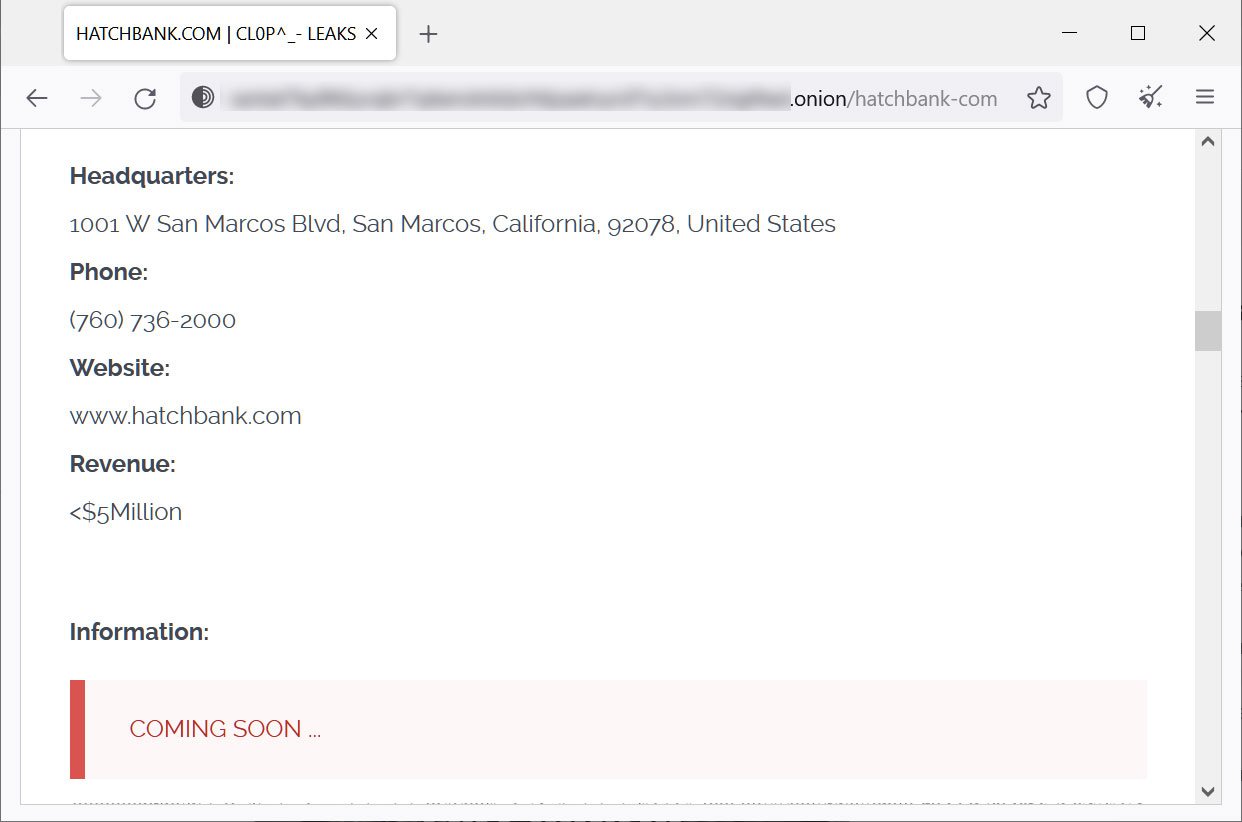
Source: BleepingComputer
Additionally, BleepingComputer has been informed that victims have started receiving ransom demands from the ransomware gang.
While it’s unclear how much the threat actors are demanding, they previously demanded $10 million in ransoms in similar situations. attacks using Zero Day Accellion FTA vulnerability in December 2020.
During these attacks, the extortion group stole large amounts of data from nearly 100 companies worldwide, with threat actors slowly leaking data to the companies while demanding million dollar ransoms.
Organizations whose Accellion servers have been hacked include, among others, energy giant Shell, cybersecurity company Qualys, supermarket giant Krogerand several universities around the world such as Stanford Medicine, University of ColoradoUniversity of Miami, University of California and University of Maryland Baltimore (UMB).
[ad_2]
Source link
