[ad_1]

The Clop ransomware gang claims to have attacked Saks Fifth Avenue on its dark website.
The cybersecurity incident is part of Clop’s ongoing attacks against vulnerable GoAnywhere MFT servers owned by established companies. While the company says no actual customer data is affected, it hasn’t addressed whether company or employee data was stolen.
Founded in 1867 by Andrew Saks and based in New York, Saks Fifth Avenue remains one of the leading luxury brand retailers serving the United States, Canada and parts of the Middle East.
Clop on a series of GoAnywhere exploits
The Clop ransomware gang listed “Saks Fifth Avenue” on its data leak website as one of its latest victims yesterday, as seen by BleepingComputer:
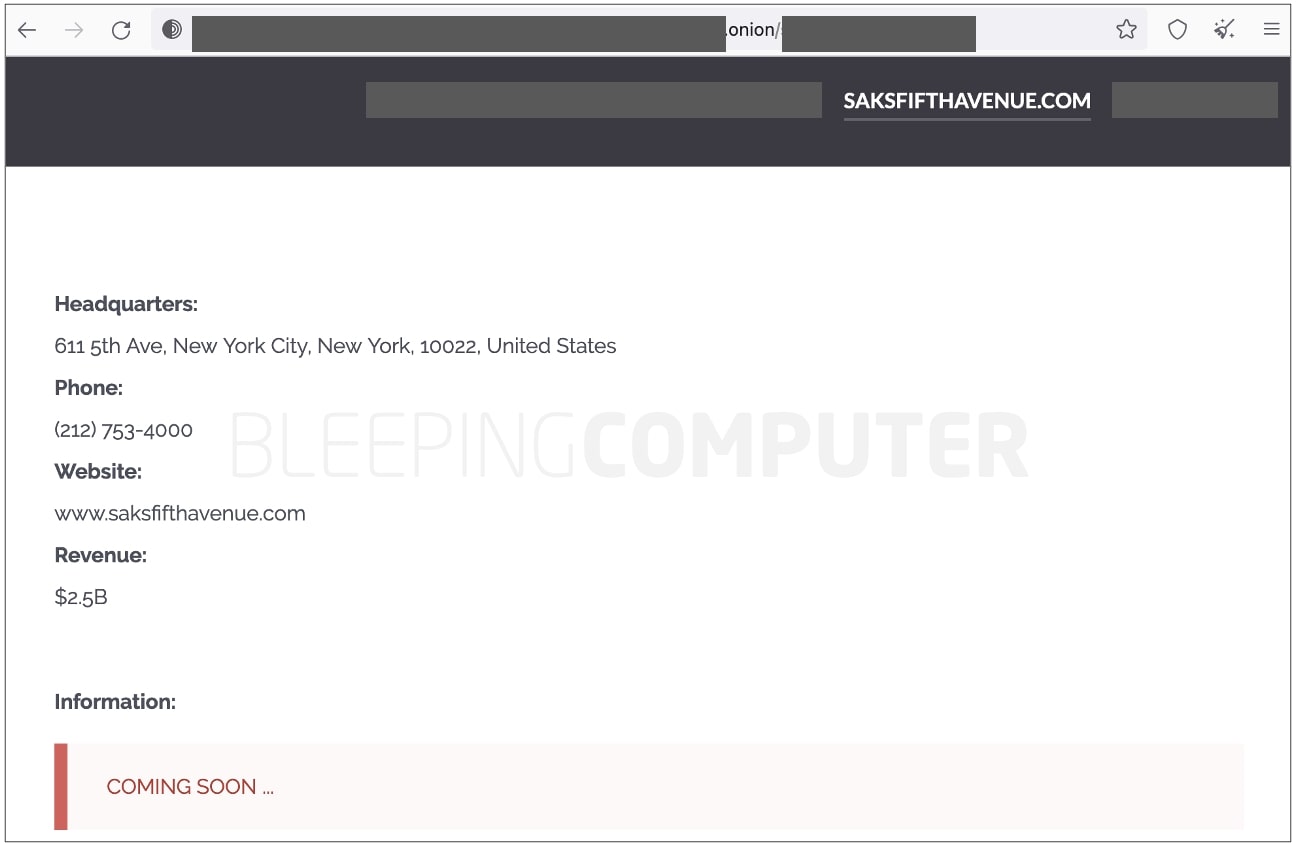
The threat actor has yet to release additional information, such as any data he stole from the luxury brand retailer’s systems, or details of ongoing ransom negotiations.
BleepingComputer has, however, confirmed that the cybersecurity incident is related to Clop’s ongoing attacks targeting GoAnywhere servers vulnerable to a security breach.
The fault, now tracked as CVE-2023-0669allows attackers to achieve remote code execution on Unpatched GoAnywhere MFT instances with their admin console exposed to internet access.
Fortra (formerly HelpSystems), the developer of GoAnywhere MFT, previously disclosed to customers that the vulnerability had been exploited as zero-day in the wild and urged customers to fix their systems. The official notice stay hidden to the public, but that was earlier released by investigative journalist Brian Krebs.
In February, Clop contacted BleepingComputer and claimed it violated more than 130 organizations and stole their data for ten days by exploiting this particular vulnerability on corporate servers.
Saks says no real customer data was stolen
BleepingComputer contacted Saks to better understand the scope of this incident. A spokesperson confirmed that the incident was related to Fortra.
“Fortra, a supplier to Saks and many other companies, recently experienced a data security incident that led to the taking of false customer data from a storage location used by Saks,” a carrier said. word from Saks to BleepingComputer.
“Fictitious customer data does not include actual customer or payment card information and is only used to simulate customer orders for testing purposes.”
While the retail giant says no “real” customer data or payment information was stolen, it didn’t answer our follow-up question about whether company data or employees were compromised in this incident.
“We take information security very seriously and are conducting an ongoing investigation into this incident alongside outside experts and law enforcement. As organizations increasingly face cybersecurity threats , we remain committed to ensuring the security of the information we hold,” Saks concluded in his statement. ours.
For the avoidance of doubt, Saks OFF 5TH– while previously a subsidiary of Saks Inc., is now a separate company and as such is unrelated to this incident.
In 2018, the cybercrime syndicate Fin7 had hacked Saks Fifth Avenue and Lord & Taylor to steal payment card information from 5 million customers. Almost a year ago, BuzzFeed News had reported that Saks Fifth Avenue stored the personal information of tens of thousands of customers on publicly accessible pages.
[ad_2]
Source link
