[ad_1]

The City of Toronto is among the latest victims of the Clop ransomware gang in the ongoing GoAnywhere hacking spree.
Other victims listed alongside the Toronto city government include the UK’s Virgin Group and the statutory company, Pension Protection Fund.
By exploiting a remote code execution flaw in Fortra’s GoAnywhere secure file transfer tool, Clop claims to have managed to breach more than 130 organizations so far.
City of Toronto confirms data theft
The Clop ransomware gang has hit the city of Toronto in its ongoing attacks targeting organizations running the vulnerable GoAnywhere file transfer utility.
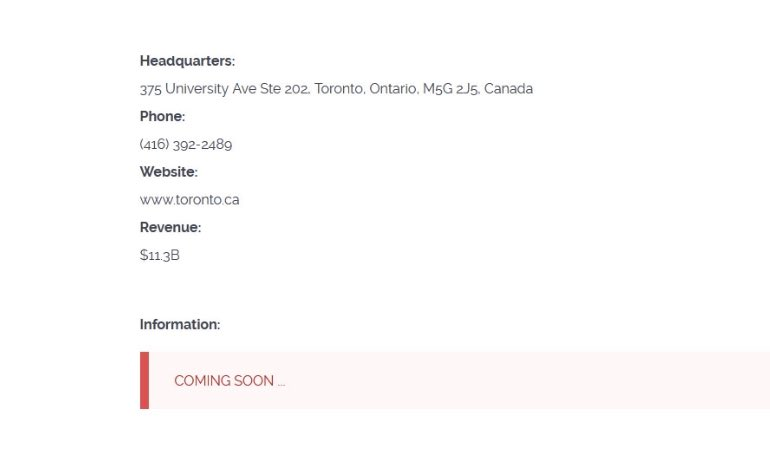
The ransomware group had previously listed the victim on its dark data leak website, according to an Intel threat analyst Dominique Alvieriwho followed the development and shared the discovery with BleepingComputer.
“On March 20, the City became aware of potential unauthorized access to City data,” a City of Toronto spokesperson told BleepingComputer.
“Today the City of Toronto confirmed that unauthorized access to City data has occurred through a third-party vendor. Access is limited to files that could not be processed through the third-party secure file transfer system.”
The spokesperson said the city government is actively investigating the details of the identified files.
“The City of Toronto is committed to protecting the privacy and security of Torontonians whose information is in its care and control and to successfully fending off cyberattacks every day.”
Toronto is among the growing list of Clop victims running vulnerable versions of a Fortra (formerly HelpSystems) program called GoAnywhere.
The fault, now tracked as CVE-2023-0669allows attackers to achieve remote code execution on Unpatched GoAnywhere MFT instances with their admin console exposed to internet access.
Fortra previously disclosed to customers that the vulnerability was exploited as zero day in the wild and urged customers to fix their systems.
In February, Clop contacted BleepingComputer and claimed it violated more than 130 organizations and stole their data for ten days by exploiting this particular vulnerability on corporate servers. And since then, the list of victims continues to grow day by day.
This month, Hitachi Energy, Saks Fifth Avenueas well as a cybersecurity company, Heading Clop’s disclosed impact resulting from the same day zero.
Clop hits UK’s Virgin Red, government pension fund
This week’s Clop victims also include Virgin Red in the UK, the Virgin Group’s rewards club that allows customers to earn and spend points at Virgin businesses, such as Virgin Atlantic, and other partner organisations. .
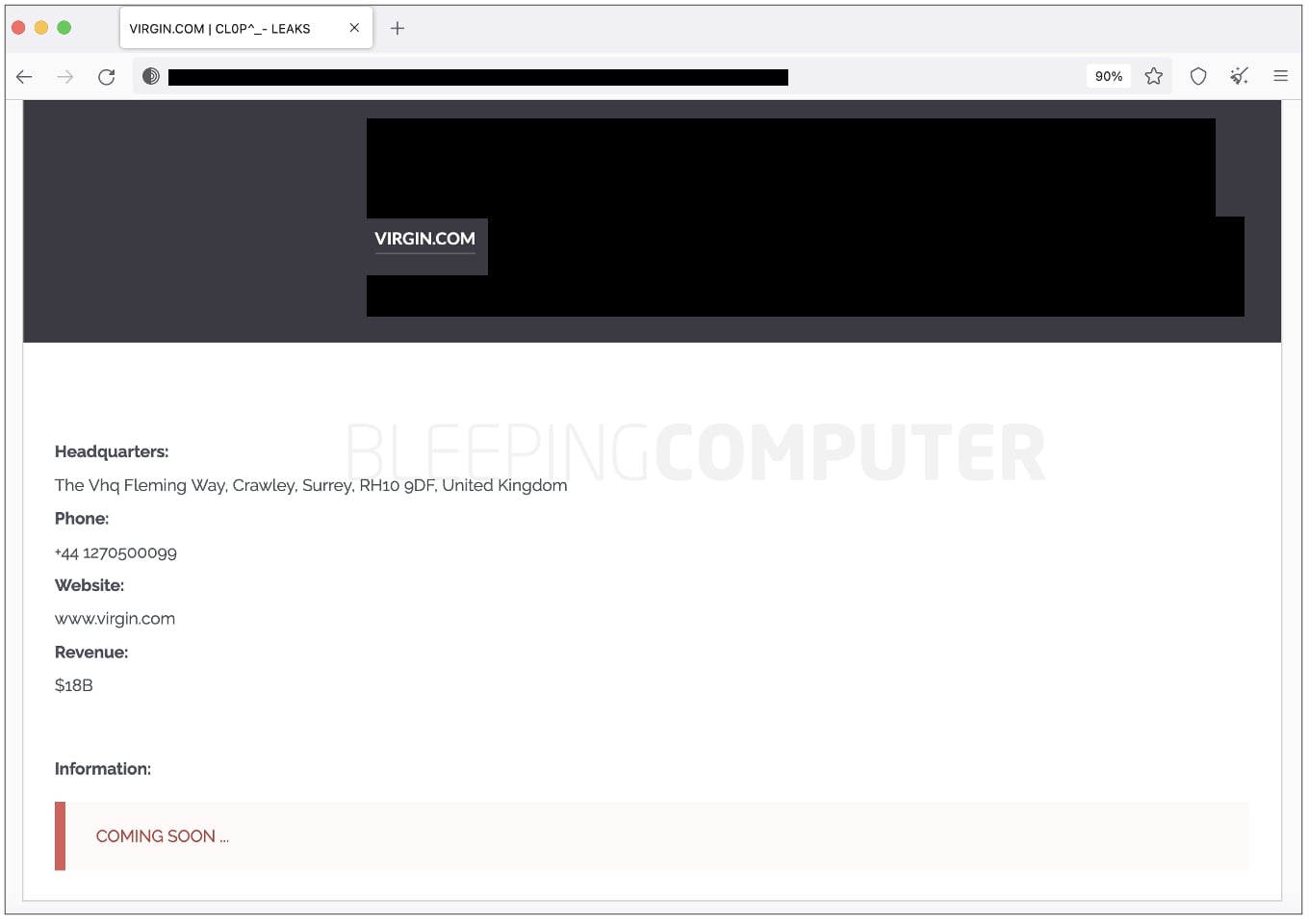
“We were recently contacted by a ransomware group, calling themselves Cl0p, who illegally obtained Virgin Red files via a cyber attack on our provider, GoAnywhere,” a Virgin spokesperson told BleepingComputer.
“The files in question pose no risk to customers or employees as they do not contain any personal data.”
Another organization to confirm the impact of the file transfer software provider is the UK’s Pension Protection Fund (PPF), a statutory public corporation that is accountable to the UK Parliament through the Secretary of State for the Department for Work and Pensions.
In the case of PPF, the ransomware and extortion group managed to get their hands on employee data.
“Unfortunately, some of our current and former employees have been impacted by the potential breach,” the organization said in a statement. statement.
“We have already informed all those affected of the situation and offered them our support and additional monitoring services to help them.”
PPF has since discontinued using GoAnywhere and continues to work closely with Fortra, its security partners, and law enforcement on investigative activities.
“Understanding what data may have been compromised and contacting anyone potentially affected has been our top priority. We can reassure our current members and taxpayers that none of their data was implicated in the breach.”
“We want to emphasize that our own systems have not been compromised and we remain vigilant, working to the highest information security standards and certifications…”
Organizations running the vulnerable GoAnywhere Secure File Transfer Utility should patch their systems as soon as possible to protect against such cyberattacks.
[ad_2]
Source link
