[ad_1]

Today, the United States Cybersecurity & Infrastructure Security Agency (CISA) announced a new pilot program to help critical infrastructure entities protect their information systems from ransomware attacks.
“Through the Ransomware Vulnerability Warning Pilot (RVWP), which began on January 30, 2023, CISA is undertaking a new effort to warn critical infrastructure entities that their systems have exposed vulnerabilities that could be exploited by threat actors from ransomware,” the cybersecurity agency said. said.
CISA’s New Ransomware Vulnerability Warning Pilot (RVWP) has two purposes: to scan the networks of critical infrastructure entities for Internet-exposed systems with vulnerabilities that ransomware attackers often exploit to breach networks and help vulnerable organizations fix flaws before they are hacked.
“As part of the RVWP, CISA leverages existing authorities and technology to proactively identify information systems that contain security vulnerabilities commonly associated with ransomware attacks,” the cybersecurity agency said. said.
“Once CISA identifies these affected systems, our regional cybersecurity staff notifies system owners of their security vulnerabilities, enabling rapid mitigation before damaging intrusions occur.”
It’s part of a broader effort to fend off the growing threat of ransomware that began nearly two years ago after a deluge of cyberattacks targeting critical infrastructure organizations and US government agencies, beginning with attacks of ransomware that hit the networks of Colonial Pipeline, JBS FoodsAnd Kaseya.
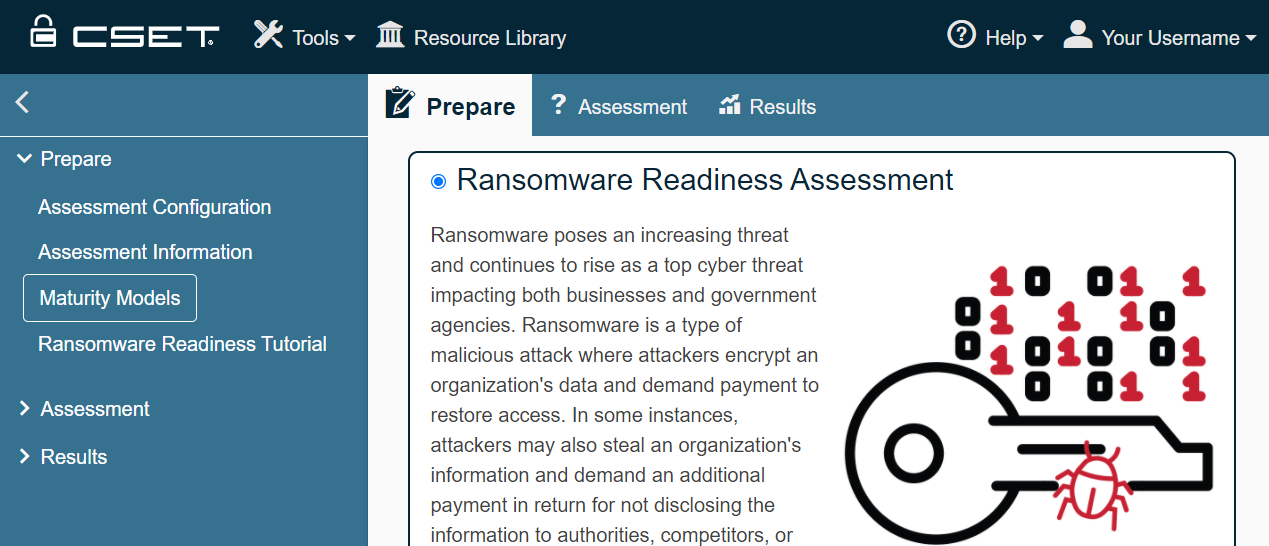
In June 2021, the agency released ransomware readiness assessment (RRA), a new module for its Cyber Security Assessment Tool (CSET).
RRA helps organizations assess their readiness to prevent and recover from ransomware attacks and can be customized for different levels of cybersecurity maturity.
Two months later, in August 2021, CISA published guidelines to help at-risk government and private sector organizations prevent ransomware data breaches.
This list of best practices was published in response to several ransomware gangs using data stolen from victims in double extortion schemes where they threatened to release the stolen information on their dedicated leak site, a tactic now embraced by most. ransomware operations.
Earlier that month, CISA launched a new partnership to protect the United States’ critical infrastructure from ransomware and other cyber threats, known as the Joint Cyber Defense Collaborative (JCDC).
JCDC has brought together federal agencies, state and local governments, and private sector organizations to create cyber defense plans for resilience against malicious cyber activity targeting critical infrastructure.
When announced, the JCDC enlisted several private sector partners, such as Microsoft, Google Cloud, Amazon Web Services, AT&T, Crowdstrike, FireEye Mandiant, Lumen, Palo Alto Networks, and Verizon, and government organizations like the Ministry of Defense, the NSA, the Department of Justice, the FBI, the US Cyber Command and the Office of the Director of National Intelligence.
Since then, CISA has also launched a dedicated portal provide all the necessary resources to prepare, defend and block ransomware attacks, including the necessary tools to report incidents related to ransomware and request technical assistance.
[ad_2]
Source link
