[ad_1]

Chinese threat group “ChamelGang” infects Linux devices with a previously unknown implant codenamed “ChamelDoH”, allowing DNS communications over HTTPS with attackers’ servers.
The particular threat actor was first documented in September 2021 by Positive Technologies; however, the researchers focused only on the Windows Toolkit.
A report published yesterday by Staircase and shared with BleepingComputer describes a new Linux implant written in C++ that expands the threat actor’s intrusion arsenal and, by extension, attackers’ indicators of compromise.
The link between ChamelGang and the new Linux malware is based on a domain previously associated with the threat actor and a custom privilege escalation tool observed by Positive Technologies in previous ChamelGang campaigns.
DNS over HTTPS for malware communication
The DNS (Domain Name System) protocol is used by software and operating systems to resolve human-readable host names to IP addresses, which are then used to establish network connections.
However, DNS queries are sent as unencrypted plain text, allowing organizations, ISPs, and others to monitor DNS queries.
As this is considered a privacy risk and allows governments to censor the internet, a new DNS protocol named DNS-over-HTTPS has been created to encrypt DNS queries so that they cannot be snooped.
However, this is a double-edged sword, as malware can use it as an effective encrypted communication channel, making it harder for security software to monitor malicious network communications.
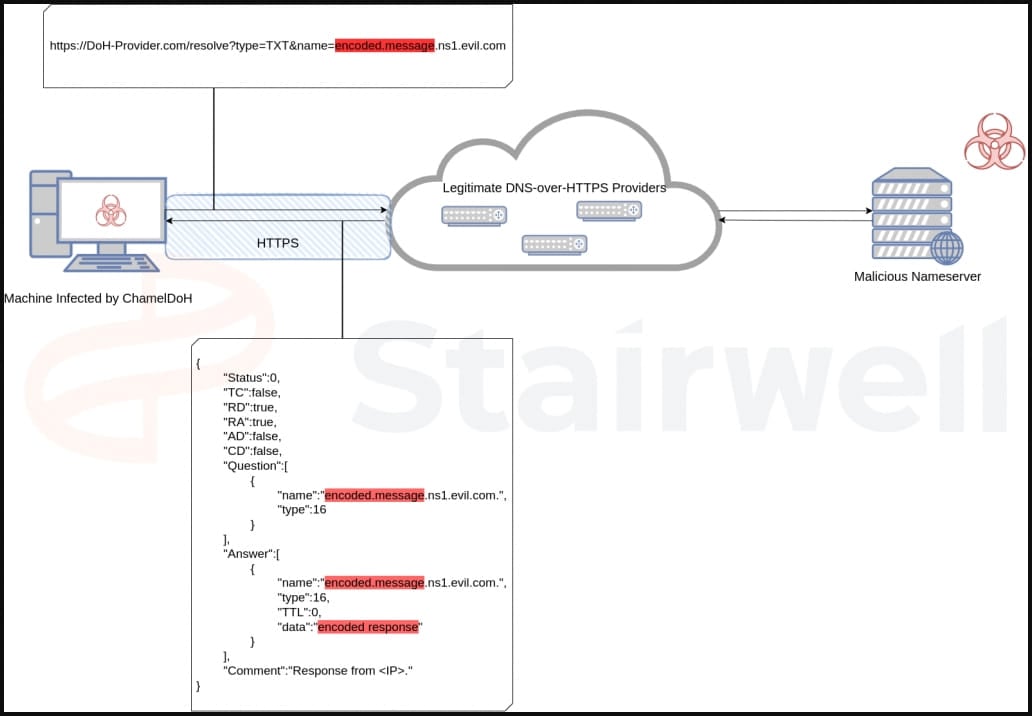
In the case of ChamelDoH, DNS-over-HTTPS provides encrypted communication between an infected device and the command and control server, making malicious requests indistinguishable from normal HTTPS traffic.
Additionally, DoH can help bypass local DNS servers by using DoH-compliant servers provided by reputable organizations, which was not seen in this case.
Finally, because DNS requests use legitimate DoH servers from Google and Cloudflare, blocking them is next to impossible without impacting legitimate traffic.
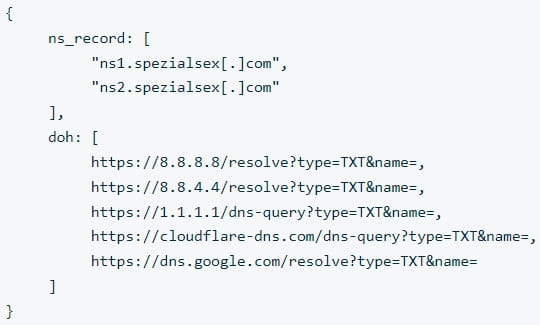
ChamelDoH uses two keys stored in its JSON configuration, “ns_record” and “doh”, to obtain C2 hostnames and a list of legitimate DoH cloud providers that can be abused to make DoH requests.
All malware communications are encrypted using AES128 and a modified base64 encoding that contains substitutes for non-alphanumeric characters. The transmitted data is then added as hostnames to the listed malware command and control servers.
This change allows the malware to issue TXT requests for domains containing encoded command and control (C2) server communications, masking the nature of these requests and reducing the likelihood of detection.
For example, when querying the TXT record, a malware DoH request would use
The C2 would respond with an encoded TXT record containing the commands the malware should execute on the infected device.
When executed, the malware will collect basic data about its host, including name, IP address, CPU architecture and system version, and generate a unique ID.
Stairwell researchers found that ChamelDoH supports the following commands that its operators can issue remotely via TXT records received in DNS queries over HTTPS:
- run – Run a file/shell command
- sleep – Set the number of seconds until the next recording
- wget – Download a file from a URL
- download – Read and download a file
- download – Download and write a file
- rm – Delete a file
- PC – Copy a file to a new location
- CD – Change the working directory
Stairwell’s analysis showed that ChamelDoH was first uploaded to VirusTotal in December 2022.
As of this writing, it is not flagged as malicious by any of the platform’s AV engines.
[ad_2]
Source link
