[ad_1]

Brave Browser version 1.47 was released yesterday, adding the Snowflake extension in the software settings, allowing users to turn their devices into proxies that help users in censored countries connect to Tor.
Brave had already added support for Tor bridges in private windows with Tor in version 1.44, released in September 2022, helping users get around restriction in the countries using the company’s own resources.
As of yesterday, Brave users can now participate in the volunteer effort to promote freedom of information in areas where oppressive governments may attempt to restrict it.
Tor Bridges
Tor bridges are volunteer-operated relays to help people circumvent Tor censorship and blocks by giving them an alternative entry point to the Onion network.
The bridges are not publicly listed to protect them from local regimes and their operators, who might try to block access to them, rendering them useless.
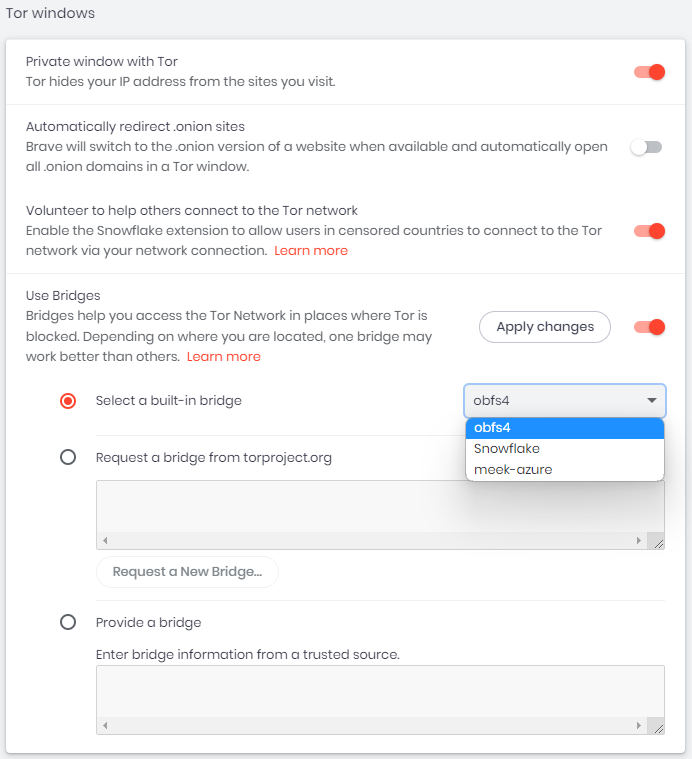
Brave allows users to use Bridges by navigating to “Settings Menu → Privacy and Security → Tor Windows”. From here, users can select a built-in bridge, request one from torproject.org, or enter a bridge they received from a trusted source.
For more information on using Tor Bridges in Brave, see this webpage with detailed instructions.
Snowflake Tor
Snowflake is a peer-to-peer network traffic connectivity system created by the Tor Project. It combines a proxy with the WebRTC protocol to automatically assign ephemeral Tor bridges to those who need them while maintaining their privacy and anonymity.
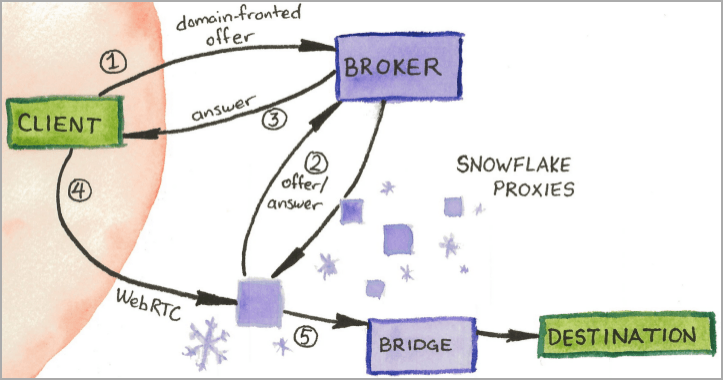
This essentially makes the block bypass system much tougher and harder to track or stop relying on the power of volunteers.
Brave users can select Snowflake in the Tor Bridge settings or volunteer to help others by adding and enabling the Snowflake extension. Turning the settings to “on” will automatically perform the required installations on Brave.
See Brave’s analytics guide for details on enabling Snowflake on your browser.
Should You Run Snowflake Proxies?
There are no known risks associated with running Snowflake proxies, and the system does not threaten to expose volunteer data. All IP addresses are kept private to accommodate system functionality.
Volunteer computers do not simply act as intermediaries, connecting to websites on behalf of others, but instead relay encrypted messages between Snowflake users and other computers on the Tor network. .
The only categories of users who should not volunteer on the Snowflake network are those who live in countries where Tor is blocked, those who use work/corporate computers, and those with limited internet connectivity.
[ad_2]
Source link
