[ad_1]

It was a big year for cybersecurity in 2022 with massive cyberattacks and data breaches, innovative phishing attacks, privacy issues and, of course, zero-day vulnerabilities.
Some stories, however, were more popular with our readers than others.
While the recent discovery that hackers stole data from LastPass vault in his August cloud storage breach was too new to make the top ten list, it deserves a mention.
Below are the ten most popular stories on BleepingComputer in 2022, with a summary of each.
ten. Russia creates its own TLS certificate authority to circumvent sanctions
Russia has created its own TLS certificate authority (CA) to allow websites to continue providing HTTPS connections after sanctions prevented them from renewing certificates from Western companies.
Since CAs must first be trusted by companies before being used in their browsers, Russian-based Yandex Browser and Atom Products were the only companies to recognize the new CA at the time.
For this reason, Russia has asked citizens to use these browsers instead of Chrome, Firefox, Edge, etc.
9. Malicious Android apps with over 1 million installs found on Google Play
Four malicious Android apps were available on Google Play that stole sensitive information from victims’ devices and generated “pay-per-click” revenue for operators.
The malware mimicked Bluetooth apps that only displayed malicious functionality 72 hours after installation. This delay allowed apps to evade detection by security software and Google’s review process.
8. BIG sabotage: famous npm package deletes files in protest against war in Ukraine
The developer of the very popular npm package named “node-ipc” has released sabotaged versions of the library that delete all data and overwrite all files on the developer’s machines, in addition to creating new text files with “peace “.
7. GIFShell attack creates a reverse shell using Microsoft Teams GIFs
A new social engineering attack has enabled a method that could be used to abuse Microsoft Teams for phishing attacks and secretly execute commands to steal data using GIFs.
This method abused various flaws to exfiltrate data directly through Microsoft’s own servers, making it look like legitimate Microsoft Team traffic.
It should be noted that the attacker must first convince a user to install a malicious stager that runs commands and uploads the output to a Microsoft Teams webhook.
6. Chrome extensions with 1 million installs hijack target browsers
Over thirty malicious Google Chrome extensions with a combined million installs on the Chrome Web Store have been used to inject affiliate links into websites and hijack searches.
The extensions themselves did not contain any malicious code, which made them difficult to detect.
However, once installed, they redirect users to other sites that encourage installation of other extensions that load malicious JavaScript into the browser.
5. Linux system service bug gives root on all major distros, exploit published
A Linux vulnerability named PwnKit has been found in the pkexec component of Polkit which attackers could exploit to gain full root privileges on the system.
This vulnerability was tracked because CVE-2021-4034 was present in the default configuration of all major Linux distributions, making it a significant concern for administrators and security professionals.
4. Microsoft Teams stores authentication tokens in clear text on Windows, Linux and Mac
Security researchers have discovered that the desktop app for Microsoft Teams saves authentication tokens in clear text in various places in Windows.
These authentication tokens could be stolen by hackers who accessed the device to log in as a user, even if they had multi-factor authentication (MFA) enabled.
Microsoft and many security researchers didn’t think this was a problem on its own, as it requires a user to have previously gained access to a system before they can steal the tokens, which already means that their “game is over” for the user because the threat actor could access all locally stored data.
However, other researchers found this report very concerning due to the rising tide of information thieves who could steal the tokens and send them back to remote attackers.
3. Okta source code stolen after its GitHub repositories were hacked
BleepingComputer was the first to report that threat actors gained access to Okta’s GitHub repositories and stole the company’s source code.
Okta began alerting customers last month via a “confidential” email shared with BleepingComputer, warning that Okta Workforce Identity Cloud (WIC) source code was exposed in the breach.
However, they said the hackers did not access the source code of Auth0 (Customer Identity Cloud) products during the breach.
2. Dev corrupts ‘colors’ and ‘faker’ of NPM libraries by breaking thousands of apps
The developer of the popular “colors” and “faker” open source libraries intentionally introduced an infinite loop that has bricked thousands of projects that depend on the packages.
Applications using these libraries suddenly found their projects displaying gibberish messages on their console stating “LIBERTY LIBERTY LIBERTY” followed by a sequence of non-ASCII characters:
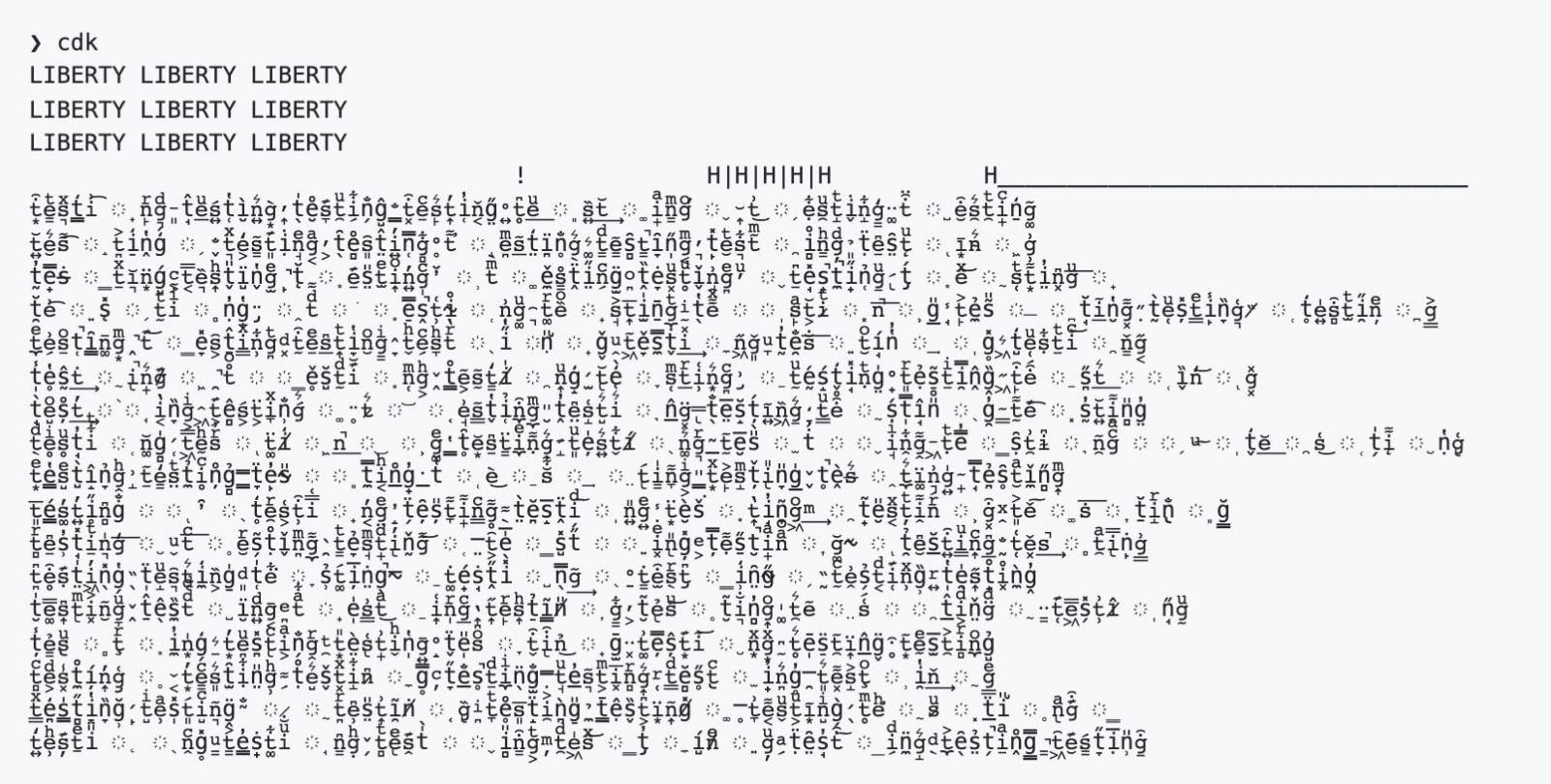
This change appears to have been introduced in retaliation against mega-corporations and commercial consumers of open-source projects that rely heavily on freeware and community-powered software but which, according to the developer, do not give back to the community.
1. Android phone owner accidentally finds a way to bypass the lock screen
This year’s most-read story tells how a security researcher accidentally discovered a way to bypass the lock screen on his fully patched Google Pixel 6 and Pixel 5 Android smartphones.
This vulnerability is identified as CVE-2022-20465 and has been addressed in Android security updates released on November 7, 2022.
A demonstration of this workaround is shown in the view below.
[ad_2]
Source link
